Malicious PowerShell Commandlets - ProcessCreation
Detects Commandlet names from well-known PowerShell exploitation frameworks
Sigma rule (View on GitHub)
1title: Malicious PowerShell Commandlets - ProcessCreation
2id: 02030f2f-6199-49ec-b258-ea71b07e03dc
3related:
4 - id: 89819aa4-bbd6-46bc-88ec-c7f7fe30efa6
5 type: derived
6 - id: 7d0d0329-0ef1-4e84-a9f5-49500f9d7c6c
7 type: similar
8status: test
9description: Detects Commandlet names from well-known PowerShell exploitation frameworks
10references:
11 - https://adsecurity.org/?p=2921
12 - https://github.com/S3cur3Th1sSh1t/PowerSharpPack/tree/master/PowerSharpBinaries
13 - https://github.com/BC-SECURITY/Invoke-ZeroLogon/blob/111d17c7fec486d9bb23387e2e828b09a26075e4/Invoke-ZeroLogon.ps1
14 - https://github.com/xorrior/RandomPS-Scripts/blob/848c919bfce4e2d67b626cbcf4404341cfe3d3b6/Get-DXWebcamVideo.ps1
15 - https://github.com/rvrsh3ll/Misc-Powershell-Scripts/blob/6f23bb41f9675d7e2d32bacccff75e931ae00554/OfficeMemScraper.ps1
16 - https://github.com/dafthack/DomainPasswordSpray/blob/b13d64a5834694aa73fd2aea9911a83027c465a7/DomainPasswordSpray.ps1
17 - https://unit42.paloaltonetworks.com/threat-assessment-black-basta-ransomware/ # Invoke-TotalExec
18 - https://research.nccgroup.com/2022/06/06/shining-the-light-on-black-basta/ # Invoke-TotalExec
19 - https://github.com/calebstewart/CVE-2021-1675 # Invoke-Nightmare
20 - https://github.com/BloodHoundAD/BloodHound/blob/0927441f67161cc6dc08a53c63ceb8e333f55874/Collectors/AzureHound.ps1
21 - https://bloodhound.readthedocs.io/en/latest/data-collection/azurehound.html
22 - https://github.com/HarmJ0y/DAMP
23 - https://github.com/samratashok/nishang
24 - https://github.com/DarkCoderSc/PowerRunAsSystem/
25 - https://github.com/besimorhino/powercat
26 - https://github.com/Kevin-Robertson/Powermad
27 - https://github.com/adrecon/ADRecon
28 - https://github.com/adrecon/AzureADRecon
29 - https://github.com/sadshade/veeam-creds/blob/6010eaf31ba41011b58d6af3950cffbf6f5cea32/Veeam-Get-Creds.ps1
30 - https://github.com/The-Viper-One/Invoke-PowerDPAPI/
31 - https://github.com/Arno0x/DNSExfiltrator/
32author: Nasreddine Bencherchali (Nextron Systems)
33date: 2023-01-02
34modified: 2025-12-10
35tags:
36 - attack.execution
37 - attack.discovery
38 - attack.t1482
39 - attack.t1087
40 - attack.t1087.001
41 - attack.t1087.002
42 - attack.t1069.001
43 - attack.t1069.002
44 - attack.t1069
45 - attack.t1059.001
46logsource:
47 category: process_creation
48 product: windows
49detection:
50 selection:
51 # Note: Please ensure alphabetical order when adding new entries
52 CommandLine|contains:
53 - 'Add-Exfiltration'
54 - 'Add-Persistence'
55 - 'Add-RegBackdoor'
56 - 'Add-RemoteRegBackdoor'
57 - 'Add-ScrnSaveBackdoor'
58 - 'Check-VM'
59 - 'ConvertTo-Rc4ByteStream'
60 - 'Decrypt-Hash'
61 - 'Disable-ADIDNSNode'
62 - 'Disable-MachineAccount'
63 - 'Do-Exfiltration'
64 - 'Enable-ADIDNSNode'
65 - 'Enable-MachineAccount'
66 - 'Enabled-DuplicateToken'
67 - 'Exploit-Jboss'
68 - 'Export-ADR'
69 - 'Export-ADRCSV'
70 - 'Export-ADRExcel'
71 - 'Export-ADRHTML'
72 - 'Export-ADRJSON'
73 - 'Export-ADRXML'
74 - 'Find-Fruit'
75 - 'Find-GPOLocation'
76 - 'Find-TrustedDocuments'
77 - 'Get-ADIDNS' # Covers: Get-ADIDNSNodeAttribute, Get-ADIDNSNodeOwner, Get-ADIDNSNodeTombstoned, Get-ADIDNSPermission, Get-ADIDNSZone
78 - 'Get-ApplicationHost'
79 - 'Get-ChromeDump'
80 - 'Get-ClipboardContents'
81 - 'Get-FoxDump'
82 - 'Get-GPPPassword'
83 - 'Get-IndexedItem'
84 - 'Get-KerberosAESKey'
85 - 'Get-Keystrokes'
86 - 'Get-LSASecret'
87 - 'Get-MachineAccountAttribute'
88 - 'Get-MachineAccountCreator'
89 - 'Get-PassHashes'
90 - 'Get-RegAlwaysInstallElevated'
91 - 'Get-RegAutoLogon'
92 - 'Get-RemoteBootKey'
93 - 'Get-RemoteCachedCredential'
94 - 'Get-RemoteLocalAccountHash'
95 - 'Get-RemoteLSAKey'
96 - 'Get-RemoteMachineAccountHash'
97 - 'Get-RemoteNLKMKey'
98 - 'Get-RickAstley'
99 - 'Get-Screenshot'
100 - 'Get-SecurityPackages'
101 - 'Get-ServiceFilePermission'
102 - 'Get-ServicePermission'
103 - 'Get-ServiceUnquoted'
104 - 'Get-SiteListPassword'
105 - 'Get-System'
106 - 'Get-TimedScreenshot'
107 - 'Get-UnattendedInstallFile'
108 - 'Get-Unconstrained'
109 - 'Get-USBKeystrokes'
110 - 'Get-VaultCredential'
111 - 'Get-VulnAutoRun'
112 - 'Get-VulnSchTask'
113 - 'Grant-ADIDNSPermission'
114 - 'Gupt-Backdoor'
115 - 'HTTP-Login'
116 - 'Install-ServiceBinary'
117 - 'Install-SSP'
118 - 'Invoke-ACLScanner'
119 - 'Invoke-ADRecon'
120 - 'Invoke-ADSBackdoor'
121 - 'Invoke-AgentSmith'
122 - 'Invoke-AllChecks'
123 - 'Invoke-ARPScan'
124 - 'Invoke-AzureHound'
125 - 'Invoke-BackdoorLNK'
126 - 'Invoke-BadPotato'
127 - 'Invoke-BetterSafetyKatz'
128 - 'Invoke-BypassUAC'
129 - 'Invoke-Carbuncle'
130 - 'Invoke-Certify'
131 - 'Invoke-ConPtyShell'
132 - 'Invoke-CredentialInjection'
133 - 'Invoke-DAFT'
134 - 'Invoke-DCSync'
135 - 'Invoke-DinvokeKatz'
136 - 'Invoke-DllInjection'
137 - 'Invoke-DNSUpdate'
138 - 'Invoke-DNSExfiltrator'
139 - 'Invoke-DomainPasswordSpray'
140 - 'Invoke-DowngradeAccount'
141 - 'Invoke-EgressCheck'
142 - 'Invoke-Eyewitness'
143 - 'Invoke-FakeLogonScreen'
144 - 'Invoke-Farmer'
145 - 'Invoke-Get-RBCD-Threaded'
146 - 'Invoke-Gopher'
147 - 'Invoke-Grouper' # Also Covers Invoke-GrouperX
148 - 'Invoke-HandleKatz'
149 - 'Invoke-ImpersonatedProcess'
150 - 'Invoke-ImpersonateSystem'
151 - 'Invoke-InteractiveSystemPowerShell'
152 - 'Invoke-Internalmonologue'
153 - 'Invoke-Inveigh'
154 - 'Invoke-InveighRelay'
155 - 'Invoke-KrbRelay'
156 - 'Invoke-LdapSignCheck'
157 - 'Invoke-Lockless'
158 - 'Invoke-MalSCCM'
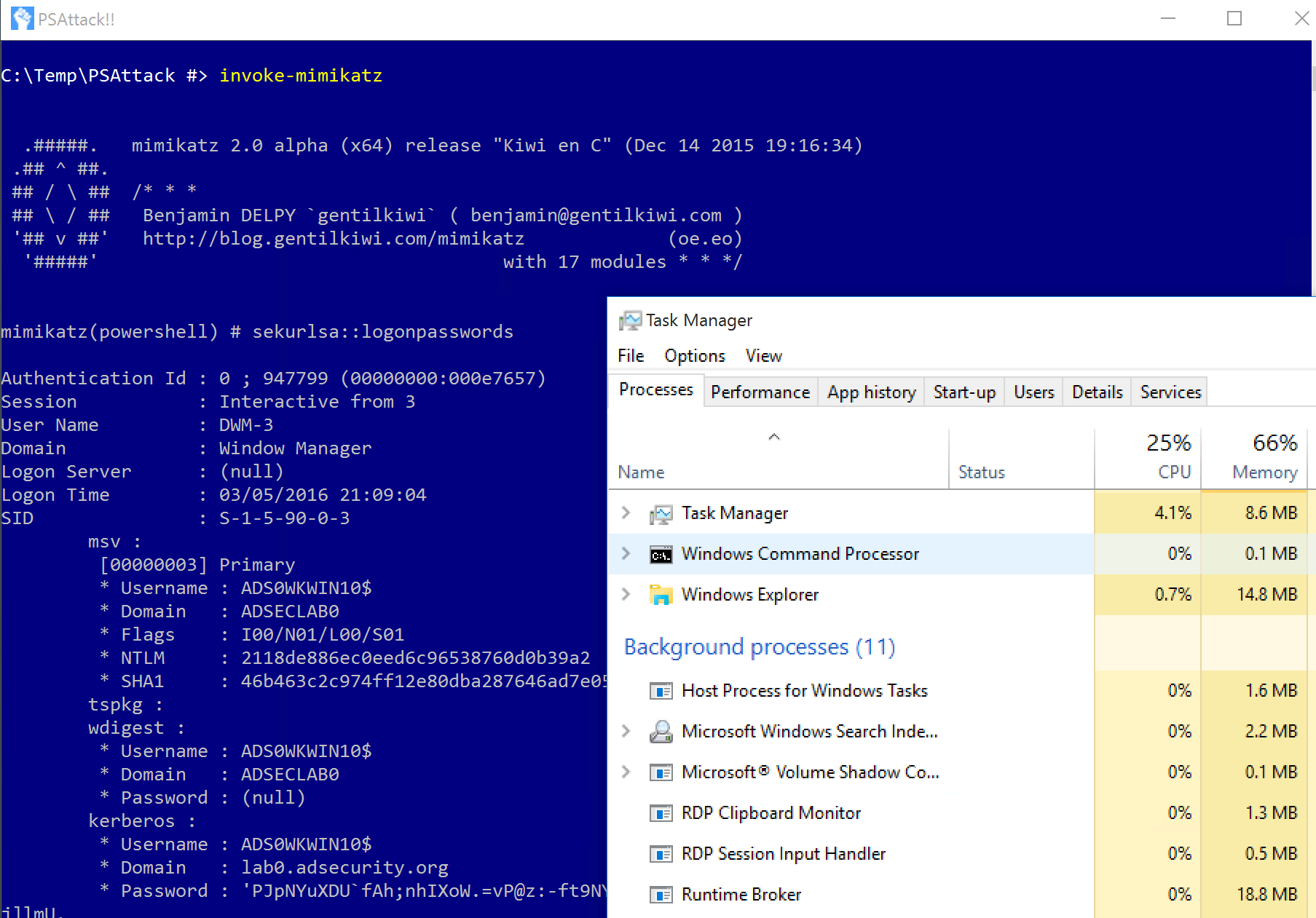
159 - 'Invoke-Mimikatz'
160 - 'Invoke-Mimikittenz'
161 - 'Invoke-MITM6'
162 - 'Invoke-NanoDump'
163 - 'Invoke-NetRipper'
164 - 'Invoke-Nightmare'
165 - 'Invoke-NinjaCopy'
166 - 'Invoke-OfficeScrape'
167 - 'Invoke-OxidResolver'
168 - 'Invoke-P0wnedshell'
169 - 'Invoke-Paranoia'
170 - 'Invoke-PortScan'
171 - 'Invoke-PoshRatHttp' # Also Covers Invoke-PoshRatHttps
172 - 'Invoke-PostExfil'
173 - 'Invoke-PowerDump'
174 - 'Invoke-PowerDPAPI'
175 - 'Invoke-PowerShellTCP'
176 - 'Invoke-PowerShellWMI'
177 - 'Invoke-PPLDump'
178 - 'Invoke-PsExec'
179 - 'Invoke-PSInject'
180 - 'Invoke-PsUaCme'
181 - 'Invoke-ReflectivePEInjection'
182 - 'Invoke-ReverseDNSLookup'
183 - 'Invoke-Rubeus'
184 - 'Invoke-RunAs'
185 - 'Invoke-SafetyKatz'
186 - 'Invoke-SauronEye'
187 - 'Invoke-SCShell'
188 - 'Invoke-Seatbelt'
189 - 'Invoke-ServiceAbuse'
190 - 'Invoke-ShadowSpray'
191 - 'Invoke-Sharp' # Covers all "Invoke-Sharp" variants
192 - 'Invoke-Shellcode'
193 - 'Invoke-SMBScanner'
194 - 'Invoke-Snaffler'
195 - 'Invoke-Spoolsample'
196 - 'Invoke-SpraySinglePassword'
197 - 'Invoke-SSHCommand'
198 - 'Invoke-StandIn'
199 - 'Invoke-StickyNotesExtract'
200 - 'Invoke-SystemCommand'
201 - 'Invoke-Tasksbackdoor'
202 - 'Invoke-Tater'
203 - 'Invoke-Thunderfox'
204 - 'Invoke-ThunderStruck'
205 - 'Invoke-TokenManipulation'
206 - 'Invoke-Tokenvator'
207 - 'Invoke-TotalExec'
208 - 'Invoke-UrbanBishop'
209 - 'Invoke-UserHunter'
210 - 'Invoke-VoiceTroll'
211 - 'Invoke-Whisker'
212 - 'Invoke-WinEnum'
213 - 'Invoke-winPEAS'
214 - 'Invoke-WireTap'
215 - 'Invoke-WmiCommand'
216 - 'Invoke-WMIExec'
217 - 'Invoke-WScriptBypassUAC'
218 - 'Invoke-Zerologon'
219 - 'MailRaider'
220 - 'New-ADIDNSNode'
221 - 'New-DNSRecordArray'
222 - 'New-HoneyHash'
223 - 'New-InMemoryModule'
224 - 'New-MachineAccount'
225 - 'New-SOASerialNumberArray'
226 - 'Out-Minidump'
227 - 'Port-Scan'
228 - 'PowerBreach'
229 - 'powercat '
230 - 'PowerUp'
231 - 'PowerView'
232 - 'Remove-ADIDNSNode'
233 - 'Remove-MachineAccount'
234 - 'Remove-Update'
235 - 'Rename-ADIDNSNode'
236 - 'Revoke-ADIDNSPermission'
237 - 'Set-ADIDNSNode' # Covers: Set-ADIDNSNodeAttribute, Set-ADIDNSNodeOwner
238 - 'Set-MacAttribute'
239 - 'Set-MachineAccountAttribute'
240 - 'Set-Wallpaper'
241 - 'Show-TargetScreen'
242 - 'Start-CaptureServer'
243 - 'Start-Dnscat2'
244 - 'Start-WebcamRecorder'
245 - 'Veeam-Get-Creds'
246 - 'VolumeShadowCopyTools'
247 condition: selection
248falsepositives:
249 - Unknown
250level: high
References
Related rules
- Malicious PowerShell Commandlets - PoshModule
- Malicious PowerShell Commandlets - ScriptBlock
- HackTool - Bloodhound/Sharphound Execution
- PUA - AdFind Suspicious Execution
- Renamed AdFind Execution