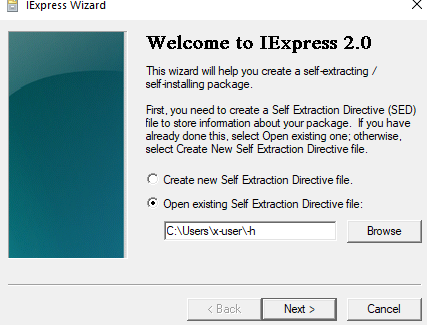
Potentially Suspicious Self Extraction Directive File Created
Detects the creation of a binary file with the ".sed" extension. The ".sed" extension stand for Self Extraction Directive files. These files are used by the "iexpress.exe" utility in order to create self extracting packages. Attackers were seen abusing this utility and creating PE files with embedded ".sed" entries. Usually ".sed" files are simple ini files and not PE binaries.
Sigma rule (View on GitHub)
1title: Potentially Suspicious Self Extraction Directive File Created
2id: ab90dab8-c7da-4010-9193-563528cfa347
3related:
4 - id: 760e75d8-c3b5-409b-a9bf-6130b4c4603f
5 type: derived
6status: experimental
7description: |
8 Detects the creation of a binary file with the ".sed" extension. The ".sed" extension stand for Self Extraction Directive files.
9 These files are used by the "iexpress.exe" utility in order to create self extracting packages.
10 Attackers were seen abusing this utility and creating PE files with embedded ".sed" entries.
11 Usually ".sed" files are simple ini files and not PE binaries.
12references:
13 - https://strontic.github.io/xcyclopedia/library/iexpress.exe-D594B2A33EFAFD0EABF09E3FDC05FCEA.html
14 - https://en.wikipedia.org/wiki/IExpress
15 - https://www.virustotal.com/gui/file/602f4ae507fa8de57ada079adff25a6c2a899bd25cd092d0af7e62cdb619c93c/behavior
16author: Joseliyo Sanchez, @Joseliyo_Jstnk
17date: 2024/02/05
18tags:
19 - attack.defense_evasion
20 - attack.t1218
21logsource:
22 product: windows
23 category: file_executable_detected
24detection:
25 selection:
26 TargetFilename|endswith: '.sed'
27 condition: selection
28falsepositives:
29 - Unknown
30level: medium
References
Related rules
- Execute Files with Msdeploy.exe
- MSI Installation From Web
- Potentially Suspicious Child Process Of DiskShadow.EXE
- Self Extraction Directive File Created In Potentially Suspicious Location
- Import LDAP Data Interchange Format File Via Ldifde.EXE