Potential Commandline Obfuscation Using Unicode Characters
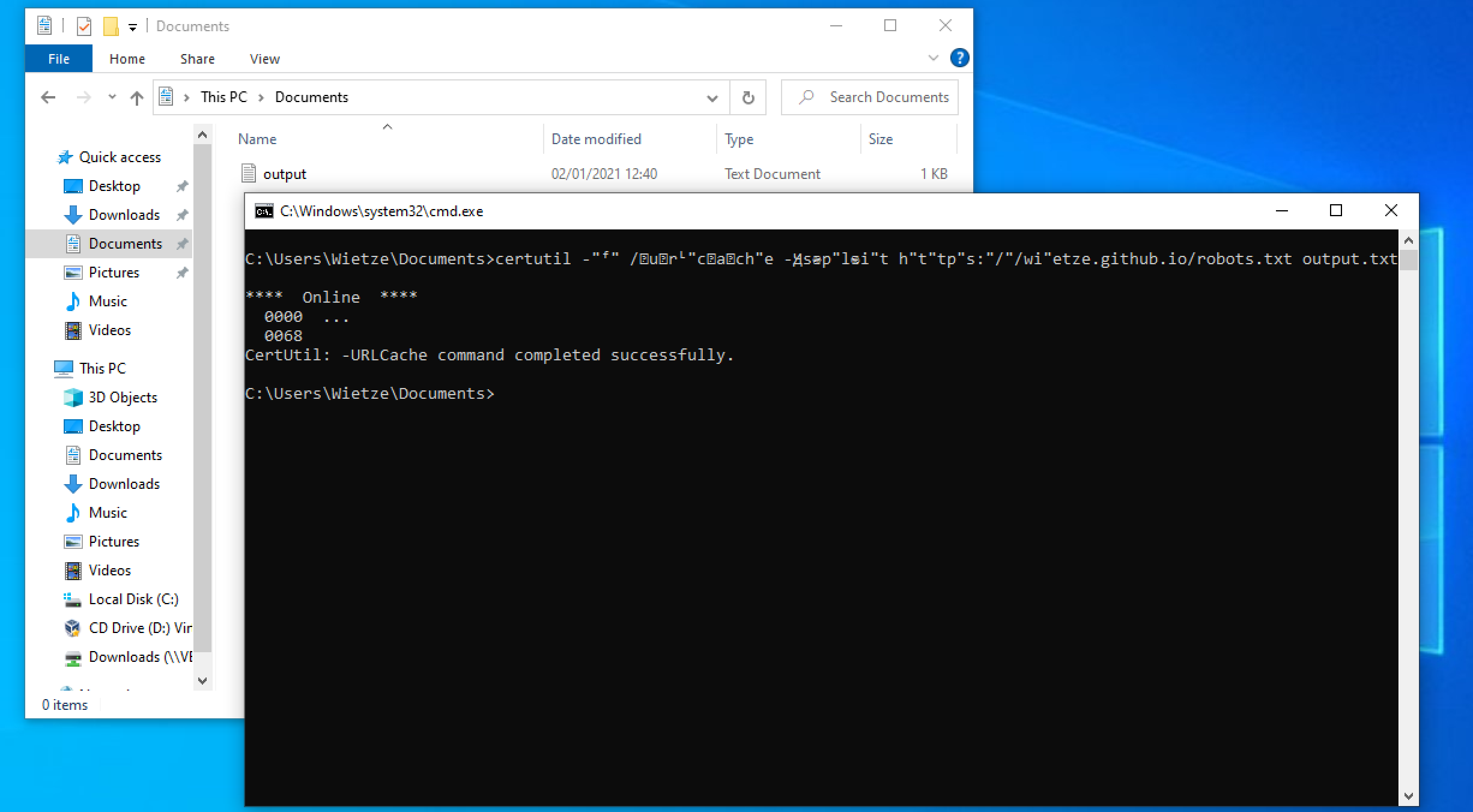
Detects potential commandline obfuscation using unicode characters. Adversaries may attempt to make an executable or file difficult to discover or analyze by encrypting, encoding, or otherwise obfuscating its contents on the system or in transit.
Sigma rule (View on GitHub)
1title: Potential Commandline Obfuscation Using Unicode Characters
2id: e0552b19-5a83-4222-b141-b36184bb8d79
3related:
4 - id: 2c0d2d7b-30d6-4d14-9751-7b9113042ab9
5 type: obsoletes
6status: test
7description: |
8 Detects potential commandline obfuscation using unicode characters.
9 Adversaries may attempt to make an executable or file difficult to discover or analyze by encrypting, encoding, or otherwise obfuscating its contents on the system or in transit.
10references:
11 - https://www.wietzebeukema.nl/blog/windows-command-line-obfuscation
12 - https://github.com/redcanaryco/atomic-red-team/blob/f339e7da7d05f6057fdfcdd3742bfcf365fee2a9/atomics/T1027/T1027.md#atomic-test-6---dlp-evasion-via-sensitive-data-in-vba-macro-over-http
13author: frack113, Florian Roth (Nextron Systems)
14date: 2022/01/15
15modified: 2023/03/03
16tags:
17 - attack.defense_evasion
18 - attack.t1027
19logsource:
20 category: process_creation
21 product: windows
22detection:
23 selection_spacing_modifiers:
24 CommandLine|contains: # spacing modifier letters that get auto-replaced
25 - 'ˣ' # 0x02E3
26 - '˪' # 0x02EA
27 - 'ˢ' # 0x02E2
28 selection_unicode_slashes: # forward slash alternatives
29 CommandLine|contains:
30 - '∕' # 0x22FF
31 - '⁄' # 0x206F
32 selection_unicode_hyphens: # hyphen alternatives
33 CommandLine|contains:
34 - '―' # 0x2015
35 - '—' # 0x2014
36 selection_other:
37 CommandLine|contains:
38 - 'â'
39 - '€'
40 - '£'
41 - '¯'
42 - '®'
43 - 'µ'
44 - '¶'
45 condition: 1 of selection_*
46falsepositives:
47 - Unknown
48level: high
References
Related rules
- Invoke-Obfuscation Obfuscated IEX Invocation
- Ping Hex IP
- Potential PowerShell Obfuscation Via WCHAR
- Suspicious Download Via Certutil.EXE
- Base64 Encoded PowerShell Command Detected