Suspicious Utility Launched via ProxyChains
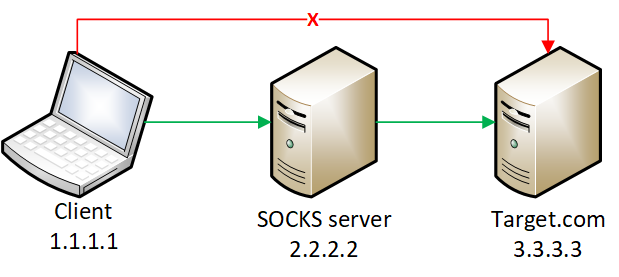
This rule monitors for the execution of suspicious linux tools through ProxyChains. ProxyChains is a command-line tool that enables the routing of network connections through intermediary proxies, enhancing anonymity and enabling access to restricted resources. Attackers can exploit the ProxyChains utility to hide their true source IP address, evade detection, and perform malicious activities through a chain of proxy servers, potentially masking their identity and intentions.
Elastic rule (View on GitHub)
1[metadata]
2creation_date = "2023/08/23"
3integration = ["endpoint", "auditd_manager", "crowdstrike", "sentinel_one_cloud_funnel"]
4maturity = "production"
5updated_date = "2026/03/24"
6
7[transform]
8[[transform.osquery]]
9label = "Osquery - Retrieve Listening Ports"
10query = "SELECT pid, address, port, socket, protocol, path FROM listening_ports"
11
12[[transform.osquery]]
13label = "Osquery - Retrieve Open Sockets"
14query = "SELECT pid, family, remote_address, remote_port, socket, state FROM process_open_sockets"
15
16[[transform.osquery]]
17label = "Osquery - Retrieve Information for a Specific User"
18query = "SELECT * FROM users WHERE username = {{user.name}}"
19
20[[transform.osquery]]
21label = "Osquery - Investigate the Account Authentication Status"
22query = "SELECT * FROM logged_in_users WHERE user = {{user.name}}"
23
24[[transform.osquery]]
25label = "Osquery - Retrieve Running Processes by User"
26query = "SELECT pid, username, name FROM processes p JOIN users u ON u.uid = p.uid ORDER BY username"
27
28[[transform.osquery]]
29label = "Osquery - Retrieve Process Info"
30query = "SELECT name, cmdline, parent, path, uid FROM processes"
31
32[rule]
33author = ["Elastic"]
34description = """
35This rule monitors for the execution of suspicious linux tools through ProxyChains. ProxyChains is a command-line tool
36that enables the routing of network connections through intermediary proxies, enhancing anonymity and enabling access to
37restricted resources. Attackers can exploit the ProxyChains utility to hide their true source IP address, evade
38detection, and perform malicious activities through a chain of proxy servers, potentially masking their identity and
39intentions.
40"""
41from = "now-9m"
42index = [
43 "auditbeat-*",
44 "endgame-*",
45 "logs-auditd_manager.auditd-*",
46 "logs-crowdstrike.fdr*",
47 "logs-endpoint.events.process*",
48 "logs-sentinel_one_cloud_funnel.*",
49]
50language = "eql"
51license = "Elastic License v2"
52name = "Suspicious Utility Launched via ProxyChains"
53note = """## Triage and analysis
54
55### Investigating Suspicious Utility Launched via ProxyChains
56
57Attackers can leverage `proxychains` to obfuscate their origin and bypass network defenses by routing their malicious traffic through multiple intermediary servers.
58
59This rule looks for a list of suspicious processes spawned through `proxychains` by analyzing process command line arguments.
60
61> **Note**:
62> This investigation guide uses the [Osquery Markdown Plugin](https://www.elastic.co/guide/en/security/current/invest-guide-run-osquery.html) introduced in Elastic Stack version 8.5.0. Older Elastic Stack versions will display unrendered Markdown in this guide.
63> This investigation guide uses [placeholder fields](https://www.elastic.co/guide/en/security/current/osquery-placeholder-fields.html) to dynamically pass alert data into Osquery queries. Placeholder fields were introduced in Elastic Stack version 8.7.0. If you're using Elastic Stack version 8.6.0 or earlier, you'll need to manually adjust this investigation guide's queries to ensure they properly run.
64
65#### Possible investigation steps
66
67- Identify any signs of suspicious network activity or anomalies that may indicate network obfuscation. This could include unexpected traffic patterns or unusual network behavior.
68 - Investigate listening ports and open sockets to look for potential protocol tunneling, reverse shells, or data exfiltration.
69 - $osquery_0
70 - $osquery_1
71- Identify the user account that performed the action, analyze it, and check whether it should perform this kind of action.
72 - $osquery_2
73- Investigate whether the user is currently logged in and active.
74 - $osquery_3
75- Investigate the script execution chain (parent process tree) for unknown processes. Examine their executable files for prevalence and whether they are located in expected locations.
76 - $osquery_4
77 - $osquery_5
78- Investigate other alerts associated with the user/host during the past 48 hours.
79 - If scripts or executables were dropped, retrieve the files and determine if they are malicious:
80 - Use a private sandboxed malware analysis system to perform analysis.
81 - Observe and collect information about the following activities:
82 - Attempts to contact external domains and addresses.
83 - Check if the domain is newly registered or unexpected.
84 - Check the reputation of the domain or IP address.
85 - File access, modification, and creation activities.
86
87### Related rules
88
89- ProxyChains Activity - 4b868f1f-15ff-4ba3-8c11-d5a7a6356d37
90- Potential Protocol Tunneling via Chisel Client - 3f12325a-4cc6-410b-8d4c-9fbbeb744cfd
91- Potential Protocol Tunneling via Chisel Server - ac8805f6-1e08-406c-962e-3937057fa86f
92- Potential Linux Tunneling and/or Port Forwarding - 6ee947e9-de7e-4281-a55d-09289bdf947e
93- Potential Protocol Tunneling via EarthWorm - 9f1c4ca3-44b5-481d-ba42-32dc215a2769
94
95### False positive analysis
96
97- If this activity is related to new benign software installation activity, consider adding exceptions — preferably with a combination of user and command line conditions.
98- If this activity is related to a system administrator or developer who uses this utility for benign purposes, consider adding exceptions for specific user accounts or hosts.
99- Try to understand the context of the execution by thinking about the user, machine, or business purpose. A small number of endpoints, such as servers with unique software, might appear unusual but satisfy a specific business need.
100
101### Response and remediation
102
103- Initiate the incident response process based on the outcome of the triage.
104- Isolate the involved host to prevent further post-compromise behavior.
105- If the triage identified malware, search the environment for additional compromised hosts.
106 - Implement temporary network rules, procedures, and segmentation to contain the malware.
107 - Stop suspicious processes.
108 - Immediately block the identified indicators of compromise (IoCs).
109 - Inspect the affected systems for additional malware backdoors, such as reverse shells, reverse proxies, or droppers, that attackers could use to reinfect the system.
110- Remove and block malicious artifacts identified during triage.
111- Investigate credential exposure on systems compromised or used by the attacker to ensure all compromised accounts are identified. Reset passwords for these accounts and other potentially compromised credentials, such as email, business systems, and web services.
112- Run a full antimalware scan. This may reveal additional artifacts left in the system, persistence mechanisms, and malware components.
113- Determine the initial vector abused by the attacker and take action to prevent reinfection through the same vector.
114- Leverage the incident response data and logging to improve the mean time to detect (MTTD) and the mean time to respond (MTTR).
115"""
116references = ["https://blog.bitsadmin.com/living-off-the-foreign-land-windows-as-offensive-platform"]
117risk_score = 47
118rule_id = "6ace94ba-f02c-4d55-9f53-87d99b6f9af4"
119setup = """## Setup
120
121This rule requires data coming in from Elastic Defend.
122
123### Elastic Defend Integration Setup
124Elastic Defend is integrated into the Elastic Agent using Fleet. Upon configuration, the integration allows the Elastic Agent to monitor events on your host and send data to the Elastic Security app.
125
126#### Prerequisite Requirements:
127- Fleet is required for Elastic Defend.
128- To configure Fleet Server refer to the [documentation](https://www.elastic.co/guide/en/fleet/current/fleet-server.html).
129
130#### The following steps should be executed in order to add the Elastic Defend integration on a Linux System:
131- Go to the Kibana home page and click "Add integrations".
132- In the query bar, search for "Elastic Defend" and select the integration to see more details about it.
133- Click "Add Elastic Defend".
134- Configure the integration name and optionally add a description.
135- Select the type of environment you want to protect, either "Traditional Endpoints" or "Cloud Workloads".
136- Select a configuration preset. Each preset comes with different default settings for Elastic Agent, you can further customize these later by configuring the Elastic Defend integration policy. [Helper guide](https://www.elastic.co/guide/en/security/current/configure-endpoint-integration-policy.html).
137- We suggest selecting "Complete EDR (Endpoint Detection and Response)" as a configuration setting, that provides "All events; all preventions"
138- Enter a name for the agent policy in "New agent policy name". If other agent policies already exist, you can click the "Existing hosts" tab and select an existing policy instead.
139For more details on Elastic Agent configuration settings, refer to the [helper guide](https://www.elastic.co/guide/en/fleet/8.10/agent-policy.html).
140- Click "Save and Continue".
141- To complete the integration, select "Add Elastic Agent to your hosts" and continue to the next section to install the Elastic Agent on your hosts.
142For more details on Elastic Defend refer to the [helper guide](https://www.elastic.co/guide/en/security/current/install-endpoint.html).
143"""
144severity = "medium"
145tags = [
146 "Domain: Endpoint",
147 "OS: Linux",
148 "Use Case: Threat Detection",
149 "Tactic: Command and Control",
150 "Data Source: Elastic Defend",
151 "Data Source: Elastic Endgame",
152 "Data Source: Auditd Manager",
153 "Data Source: Crowdstrike",
154 "Data Source: SentinelOne",
155 "Resources: Investigation Guide",
156]
157timestamp_override = "event.ingested"
158type = "eql"
159query = '''
160process where host.os.type == "linux" and event.type == "start" and
161event.action in ("exec", "exec_event", "start", "ProcessRollup2", "executed", "process_started") and
162process.name == "proxychains" and process.args : (
163 "ssh", "sshd", "sshuttle", "socat", "iodine", "iodined", "dnscat", "hans", "hans-ubuntu", "ptunnel-ng",
164 "ssf", "3proxy", "ngrok", "gost", "pivotnacci", "chisel*", "nmap", "ping", "python*", "php*", "perl", "ruby",
165 "lua*", "openssl", "nc", "netcat", "ncat", "telnet", "awk", "java", "telnet", "ftp", "curl", "wget"
166)
167'''
168
169[[rule.threat]]
170framework = "MITRE ATT&CK"
171
172[[rule.threat.technique]]
173id = "T1090"
174name = "Proxy"
175reference = "https://attack.mitre.org/techniques/T1090/"
176
177[[rule.threat.technique.subtechnique]]
178id = "T1090.003"
179name = "Multi-hop Proxy"
180reference = "https://attack.mitre.org/techniques/T1090/003/"
181
182[[rule.threat.technique]]
183id = "T1572"
184name = "Protocol Tunneling"
185reference = "https://attack.mitre.org/techniques/T1572/"
186
187[rule.threat.tactic]
188id = "TA0011"
189name = "Command and Control"
190reference = "https://attack.mitre.org/tactics/TA0011/"
Triage and analysis
Investigating Suspicious Utility Launched via ProxyChains
Attackers can leverage proxychains to obfuscate their origin and bypass network defenses by routing their malicious traffic through multiple intermediary servers.
This rule looks for a list of suspicious processes spawned through proxychains by analyzing process command line arguments.
Note: This investigation guide uses the Osquery Markdown Plugin introduced in Elastic Stack version 8.5.0. Older Elastic Stack versions will display unrendered Markdown in this guide. This investigation guide uses placeholder fields to dynamically pass alert data into Osquery queries. Placeholder fields were introduced in Elastic Stack version 8.7.0. If you're using Elastic Stack version 8.6.0 or earlier, you'll need to manually adjust this investigation guide's queries to ensure they properly run.
Possible investigation steps
- Identify any signs of suspicious network activity or anomalies that may indicate network obfuscation. This could include unexpected traffic patterns or unusual network behavior.
- Investigate listening ports and open sockets to look for potential protocol tunneling, reverse shells, or data exfiltration.
- $osquery_0
- $osquery_1
- Investigate listening ports and open sockets to look for potential protocol tunneling, reverse shells, or data exfiltration.
- Identify the user account that performed the action, analyze it, and check whether it should perform this kind of action.
- $osquery_2
- Investigate whether the user is currently logged in and active.
- $osquery_3
- Investigate the script execution chain (parent process tree) for unknown processes. Examine their executable files for prevalence and whether they are located in expected locations.
- $osquery_4
- $osquery_5
- Investigate other alerts associated with the user/host during the past 48 hours.
- If scripts or executables were dropped, retrieve the files and determine if they are malicious:
- Use a private sandboxed malware analysis system to perform analysis.
- Observe and collect information about the following activities:
- Attempts to contact external domains and addresses.
- Check if the domain is newly registered or unexpected.
- Check the reputation of the domain or IP address.
- File access, modification, and creation activities.
- Attempts to contact external domains and addresses.
- Observe and collect information about the following activities:
- Use a private sandboxed malware analysis system to perform analysis.
- If scripts or executables were dropped, retrieve the files and determine if they are malicious:
Related rules
- ProxyChains Activity - 4b868f1f-15ff-4ba3-8c11-d5a7a6356d37
- Potential Protocol Tunneling via Chisel Client - 3f12325a-4cc6-410b-8d4c-9fbbeb744cfd
- Potential Protocol Tunneling via Chisel Server - ac8805f6-1e08-406c-962e-3937057fa86f
- Potential Linux Tunneling and/or Port Forwarding - 6ee947e9-de7e-4281-a55d-09289bdf947e
- Potential Protocol Tunneling via EarthWorm - 9f1c4ca3-44b5-481d-ba42-32dc215a2769
False positive analysis
- If this activity is related to new benign software installation activity, consider adding exceptions — preferably with a combination of user and command line conditions.
- If this activity is related to a system administrator or developer who uses this utility for benign purposes, consider adding exceptions for specific user accounts or hosts.
- Try to understand the context of the execution by thinking about the user, machine, or business purpose. A small number of endpoints, such as servers with unique software, might appear unusual but satisfy a specific business need.
Response and remediation
- Initiate the incident response process based on the outcome of the triage.
- Isolate the involved host to prevent further post-compromise behavior.
- If the triage identified malware, search the environment for additional compromised hosts.
- Implement temporary network rules, procedures, and segmentation to contain the malware.
- Stop suspicious processes.
- Immediately block the identified indicators of compromise (IoCs).
- Inspect the affected systems for additional malware backdoors, such as reverse shells, reverse proxies, or droppers, that attackers could use to reinfect the system.
- Remove and block malicious artifacts identified during triage.
- Investigate credential exposure on systems compromised or used by the attacker to ensure all compromised accounts are identified. Reset passwords for these accounts and other potentially compromised credentials, such as email, business systems, and web services.
- Run a full antimalware scan. This may reveal additional artifacts left in the system, persistence mechanisms, and malware components.
- Determine the initial vector abused by the attacker and take action to prevent reinfection through the same vector.
- Leverage the incident response data and logging to improve the mean time to detect (MTTD) and the mean time to respond (MTTR).
References
Related rules
- AWS CLI Command with Custom Endpoint URL
- Linux Telegram API Request
- Potential Linux Tunneling and/or Port Forwarding
- Potential Linux Tunneling and/or Port Forwarding via Command Line
- Potential Protocol Tunneling via EarthWorm