Using powershell specific download cradle OneLiner
Detects the execution of a specific OneLiner to download and execute powershell modules in memory.
Sigma rule (View on GitHub)
1title: Using powershell specific download cradle OneLiner
2status: Experimental
3description: Detects the execution of a specific OneLiner to download and execute powershell modules in memory.
4author: \@Kostastsale, \@TheDFIRReport
5references:
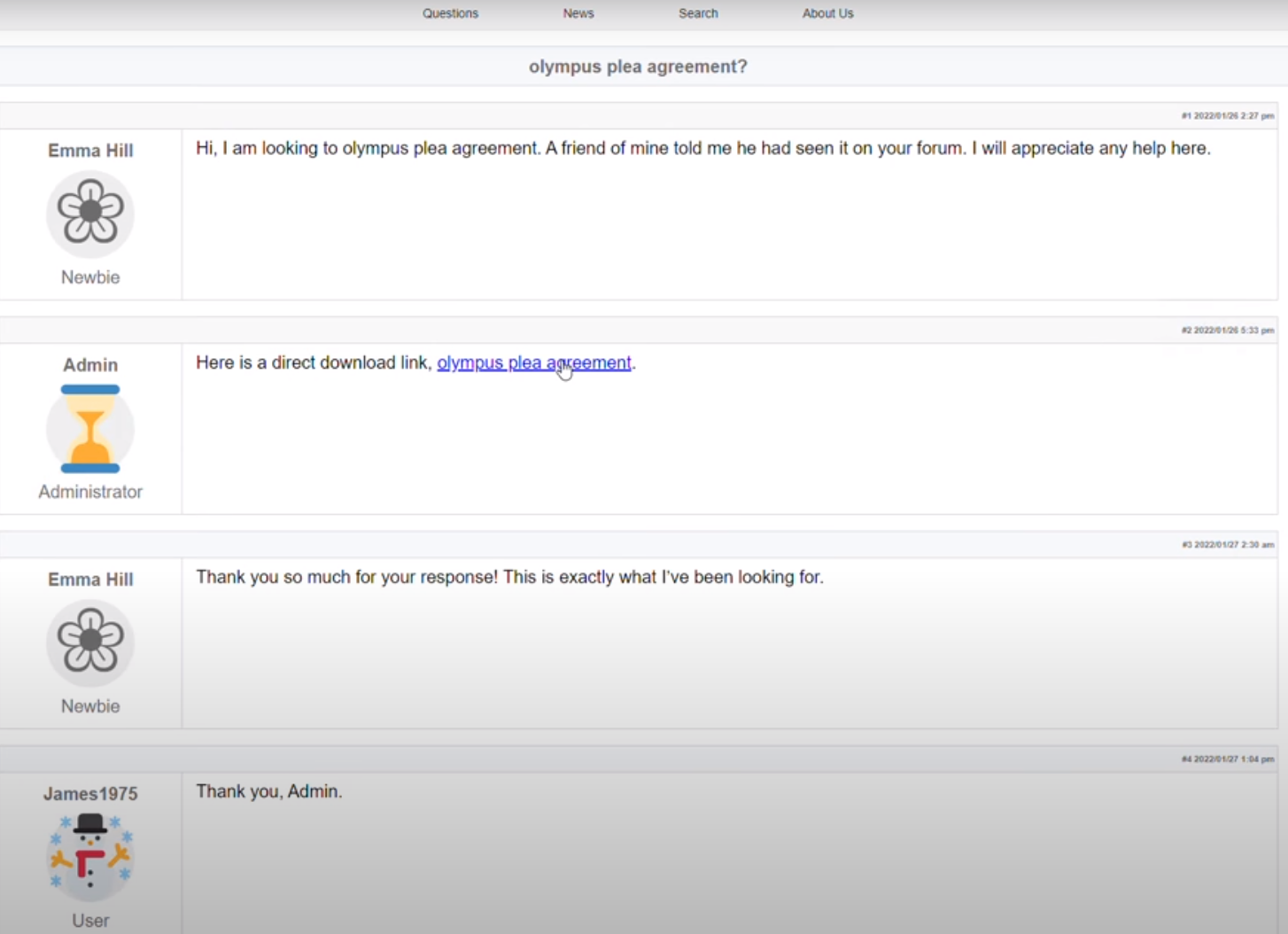
6 - https://thedfirreport.com/2022/05/09/seo-poisoning-a-gootloader-story/
7 - https://gist.github.com/mgeeky/3b11169ab77a7de354f4111aa2f0df38
8date: 2022/05/09
9logsource:
10 product: windows
11 category: process_creation
12detection:
13 selection1:
14 Image|endswith:
15 - '\powershell.exe'
16 CommandLine|contains|all:
17 - 'http://127.0.0.1'
18 - '%{(IRM $_)}'
19 - '.SubString.ToString()[67,72,64]-Join'
20 - 'Import-Module'
21 condition: selection1
22falsepositives:
23 - Uknown
24level: high
25tags:
26 - attack.defense_evasion
27 - attack.t1562.001
28 - attack.execution
29 - T1059.001```
References
Related rules
- Deleting Windows Defender scheduled tasks
- Enabling restricted admin mode
- Raspberry Robin initial execution from external drive
- Raspberry Robin subsequent execution of commands
- ChromeLoader Malware Detection