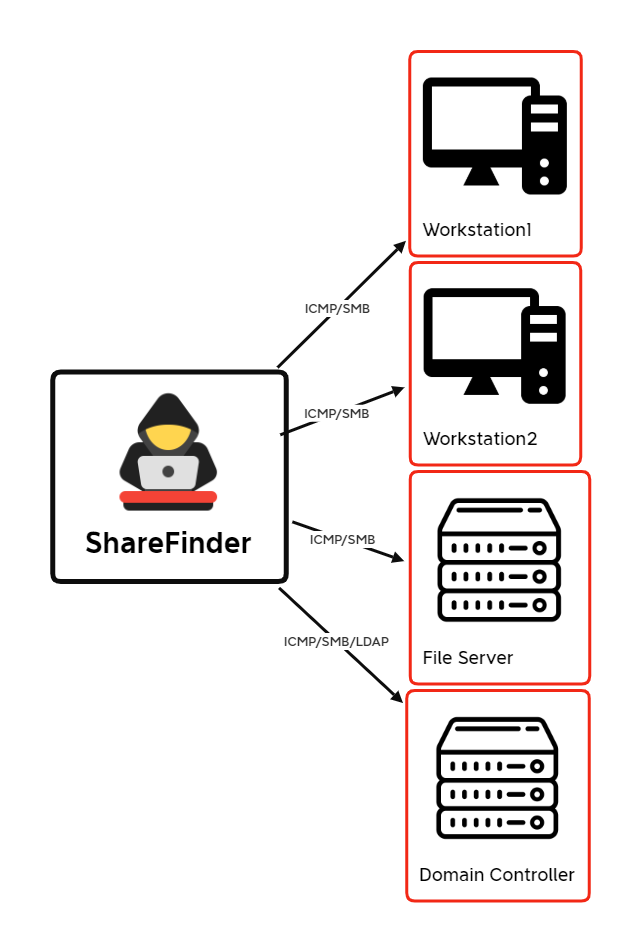
Invoke-ShareFinder Discovery Activity
Use of Invoke-ShareFinder detected via PowerShell logging
Sigma rule (View on GitHub)
1title: Invoke-ShareFinder Discovery Activity
2id: fbedfe8c-3e02-4f3c-b521-4b83d5054fd1
3status: experimental
4description: |
5 Use of Invoke-ShareFinder detected via PowerShell logging
6references:
7 - https://thedfirreport.com/2023/01/23/sharefinder-how-threat-actors-discover-file-shares
8 - https://powersploit.readthedocs.io/en/stable/Recon/README/
9
10author: TheDFIRReport
11date: 2023-01-22
12modified: 2024-02-23
13tags:
14 - attack.discovery
15 - attack.t1135
16logsource:
17 product: windows
18 category: ps_module
19 definition: 'Requirements: PowerShell Module Logging must be enabled'
20detection:
21 selection_4103:
22 Payload|contains: 'Invoke-ShareFinder'
23 condition: selection_4103
24falsepositives:
25 - Unknown
26level: High
References
Related rules
- Invoke-ShareFinder Discovery Activity
- NetScan Share Enumeration Write Access Check
- HackTool - SharpView Execution
- PUA - Advanced IP Scanner Execution
- PUA - Advanced Port Scanner Execution