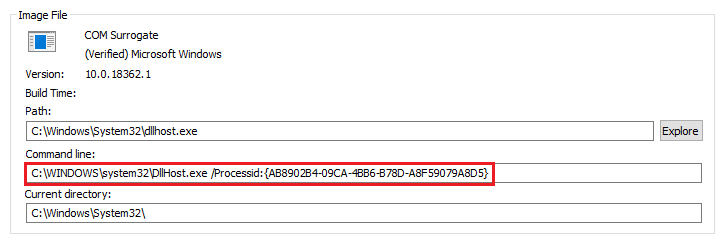
Dllhost.EXE Initiated Network Connection To Non-Local IP Address
Detects dllhost initiating a network connection to a non-local IP address. Aside from Microsoft own IP range that needs to be excluded. Network communication from Dllhost will depend entirely on the hosted DLL. An initial baseline is recommended before deployment.
Sigma rule (View on GitHub)
1title: Dllhost.EXE Initiated Network Connection To Non-Local IP Address
2id: cfed2f44-16df-4bf3-833a-79405198b277
3status: test
4description: |
5 Detects dllhost initiating a network connection to a non-local IP address.
6 Aside from Microsoft own IP range that needs to be excluded. Network communication from Dllhost will depend entirely on the hosted DLL.
7 An initial baseline is recommended before deployment.
8references:
9 - https://redcanary.com/blog/child-processes/
10 - https://nasbench.medium.com/what-is-the-dllhost-exe-process-actually-running-ef9fe4c19c08
11author: bartblaze
12date: 2020/07/13
13modified: 2024/03/12
14tags:
15 - attack.defense_evasion
16 - attack.t1218
17 - attack.execution
18 - attack.t1559.001
19logsource:
20 category: network_connection
21 product: windows
22detection:
23 selection:
24 Image|endswith: '\dllhost.exe'
25 Initiated: 'true'
26 filter_main_local_ranges:
27 DestinationIp|cidr:
28 - '::1/128' # IPv6 loopback
29 - '10.0.0.0/8'
30 - '127.0.0.0/8'
31 - '172.16.0.0/12'
32 - '192.168.0.0/16'
33 - '169.254.0.0/16'
34 - 'fc00::/7' # IPv6 private addresses
35 - 'fe80::/10' # IPv6 link-local addresses
36 filter_main_msrange:
37 DestinationIp|cidr:
38 - '20.184.0.0/13' # Microsoft Corporation
39 - '20.192.0.0/10' # Microsoft Corporation
40 - '23.72.0.0/13' # Akamai International B.V.
41 - '51.10.0.0/15' # Microsoft Corporation
42 - '51.103.0.0/16' # Microsoft Corporation
43 - '51.104.0.0/15' # Microsoft Corporation
44 - '52.224.0.0/11' # Microsoft Corporation
45 - '204.79.197.0/24' # Microsoft Corporation'
46 condition: selection and not 1 of filter_main_*
47falsepositives:
48 - Communication to other corporate systems that use IP addresses from public address spaces
49level: medium
References
Related rules
- Microsoft Sync Center Suspicious Network Connections
- Network Connection Initiated By Regsvr32.EXE
- Potential Compromised 3CXDesktopApp Execution
- Potential Compromised 3CXDesktopApp Update Activity
- Binary Proxy Execution Via Dotnet-Trace.EXE