Execution Of Script Located In Potentially Suspicious Directory
Detects executions of scripts located in potentially suspicious locations such as "/tmp" via a shell such as "bash", "sh", etc.
Sigma rule (View on GitHub)
1title: Execution Of Script Located In Potentially Suspicious Directory
2id: 30bcce26-51c5-49f2-99c8-7b59e3af36c7
3status: test
4description: Detects executions of scripts located in potentially suspicious locations such as "/tmp" via a shell such as "bash", "sh", etc.
5references:
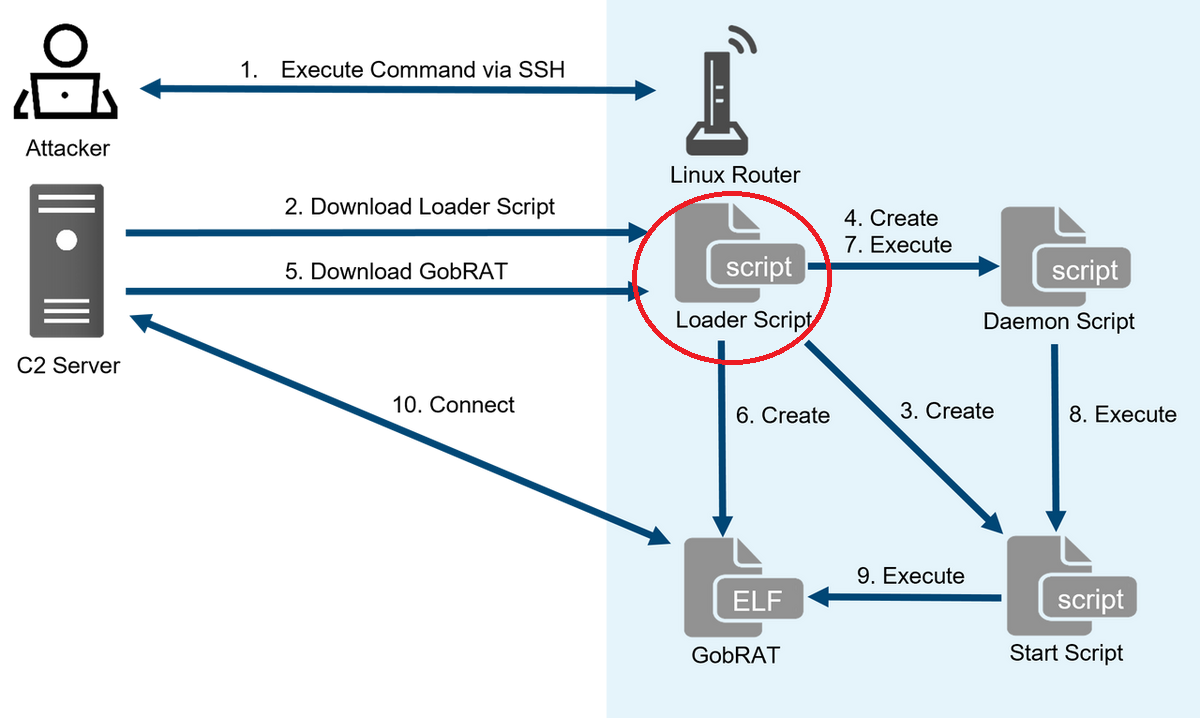
6 - https://blogs.jpcert.or.jp/en/2023/05/gobrat.html
7 - https://jstnk9.github.io/jstnk9/research/GobRAT-Malware/
8 - https://www.virustotal.com/gui/file/60bcd645450e4c846238cf0e7226dc40c84c96eba99f6b2cffcd0ab4a391c8b3/detection
9 - https://www.virustotal.com/gui/file/3e44c807a25a56f4068b5b8186eee5002eed6f26d665a8b791c472ad154585d1/detection
10author: Joseliyo Sanchez, @Joseliyo_Jstnk
11date: 2023/06/02
12tags:
13 - attack.execution
14logsource:
15 product: linux
16 category: process_creation
17detection:
18 selection_img:
19 Image|endswith:
20 - '/bash'
21 - '/csh'
22 - '/dash'
23 - '/fish'
24 - '/ksh'
25 - '/sh'
26 - '/zsh'
27 selection_flag:
28 CommandLine|contains: ' -c '
29 selection_paths:
30 # Note: Add more suspicious paths
31 CommandLine|contains: '/tmp/'
32 condition: all of selection_*
33falsepositives:
34 - Unknown
35level: medium
References
Related rules
- AWS IAM S3Browser LoginProfile Creation
- AWS IAM S3Browser Templated S3 Bucket Policy Creation
- AWS IAM S3Browser User or AccessKey Creation
- Add Windows Capability Via PowerShell Cmdlet
- Add Windows Capability Via PowerShell Script