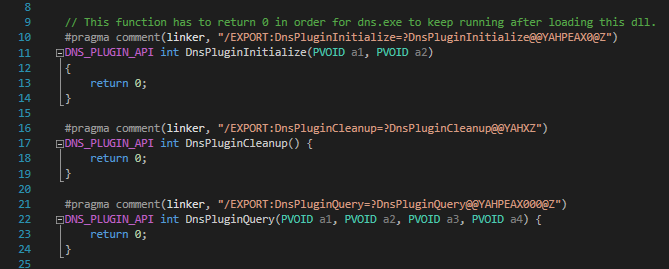
New DNS ServerLevelPluginDll Installed Via Dnscmd.EXE
Detects the installation of a DNS plugin DLL via ServerLevelPluginDll parameter in registry, which can be used to execute code in context of the DNS server (restart required)
Sigma rule (View on GitHub)
1title: New DNS ServerLevelPluginDll Installed Via Dnscmd.EXE
2id: f63b56ee-3f79-4b8a-97fb-5c48007e8573
3related:
4 - id: e61e8a88-59a9-451c-874e-70fcc9740d67
5 type: derived
6 - id: cbe51394-cd93-4473-b555-edf0144952d9
7 type: derived
8status: test
9description: Detects the installation of a DNS plugin DLL via ServerLevelPluginDll parameter in registry, which can be used to execute code in context of the DNS server (restart required)
10references:
11 - https://medium.com/@esnesenon/feature-not-bug-dnsadmin-to-dc-compromise-in-one-line-a0f779b8dc83
12 - https://blog.3or.de/hunting-dns-server-level-plugin-dll-injection.html
13author: Florian Roth (Nextron Systems)
14date: 2017-05-08
15modified: 2023-02-05
16tags:
17 - attack.privilege-escalation
18 - attack.persistence
19 - attack.defense-evasion
20 - attack.t1574.001
21 - attack.t1112
22logsource:
23 category: process_creation
24 product: windows
25detection:
26 selection:
27 Image|endswith: '\dnscmd.exe'
28 CommandLine|contains|all:
29 - '/config'
30 - '/serverlevelplugindll'
31 condition: selection
32falsepositives:
33 - Unknown
34level: high
References
Related rules
- DHCP Callout DLL Installation
- New DNS ServerLevelPluginDll Installed
- APT27 - Emissary Panda Activity
- Aruba Network Service Potential DLL Sideloading
- DHCP Server Error Failed Loading the CallOut DLL