Cloudflared Tunnel Execution
Detects execution of the "cloudflared" tool to connect back to a tunnel. This was seen used by threat actors to maintain persistence and remote access to compromised networks.
Sigma rule (View on GitHub)
1title: Cloudflared Tunnel Execution
2id: 9a019ffc-3580-4c9d-8d87-079f7e8d3fd4
3status: test
4description: Detects execution of the "cloudflared" tool to connect back to a tunnel. This was seen used by threat actors to maintain persistence and remote access to compromised networks.
5references:
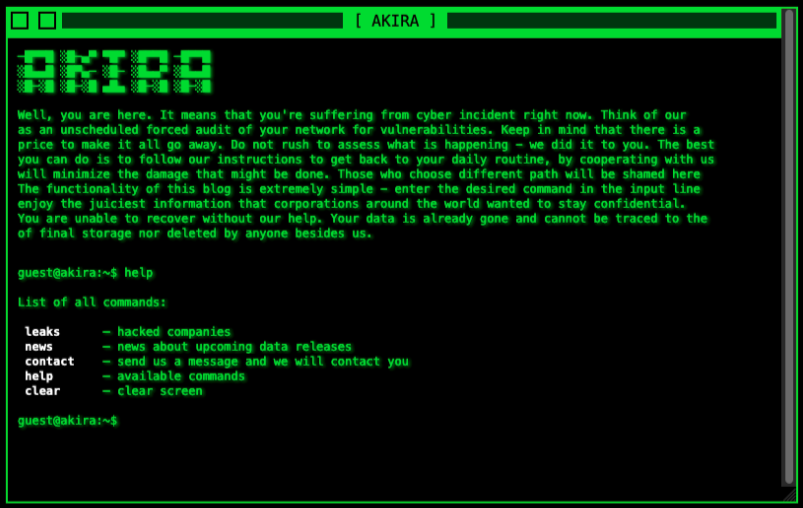
6 - https://blog.reconinfosec.com/emergence-of-akira-ransomware-group
7 - https://github.com/cloudflare/cloudflared
8 - https://developers.cloudflare.com/cloudflare-one/connections/connect-apps
9author: Janantha Marasinghe, Nasreddine Bencherchali (Nextron Systems)
10date: 2023-05-17
11modified: 2023-12-20
12tags:
13 - attack.command-and-control
14 - attack.t1102
15 - attack.t1090
16 - attack.t1572
17logsource:
18 category: process_creation
19 product: windows
20detection:
21 selection:
22 CommandLine|contains|all:
23 - ' tunnel '
24 - ' run '
25 CommandLine|contains:
26 - '-config '
27 - '-credentials-contents '
28 - '-credentials-file '
29 - '-token '
30 condition: selection
31falsepositives:
32 - Legitimate usage of Cloudflared tunnel.
33level: medium
References
Related rules
- Cloudflared Tunnel Connections Cleanup
- Communication To Ngrok Tunneling Service - Linux
- Communication To Ngrok Tunneling Service Initiated
- New Connection Initiated To Potential Dead Drop Resolver Domain
- HackTool - Htran/NATBypass Execution