MSSQL XPCmdshell Suspicious Execution
Detects when the MSSQL "xp_cmdshell" stored procedure is used to execute commands
Sigma rule (View on GitHub)
1title: MSSQL XPCmdshell Suspicious Execution
2id: 7f103213-a04e-4d59-8261-213dddf22314
3status: test
4description: Detects when the MSSQL "xp_cmdshell" stored procedure is used to execute commands
5references:
6 - https://www.netspi.com/blog/technical/network-penetration-testing/sql-server-persistence-part-1-startup-stored-procedures/
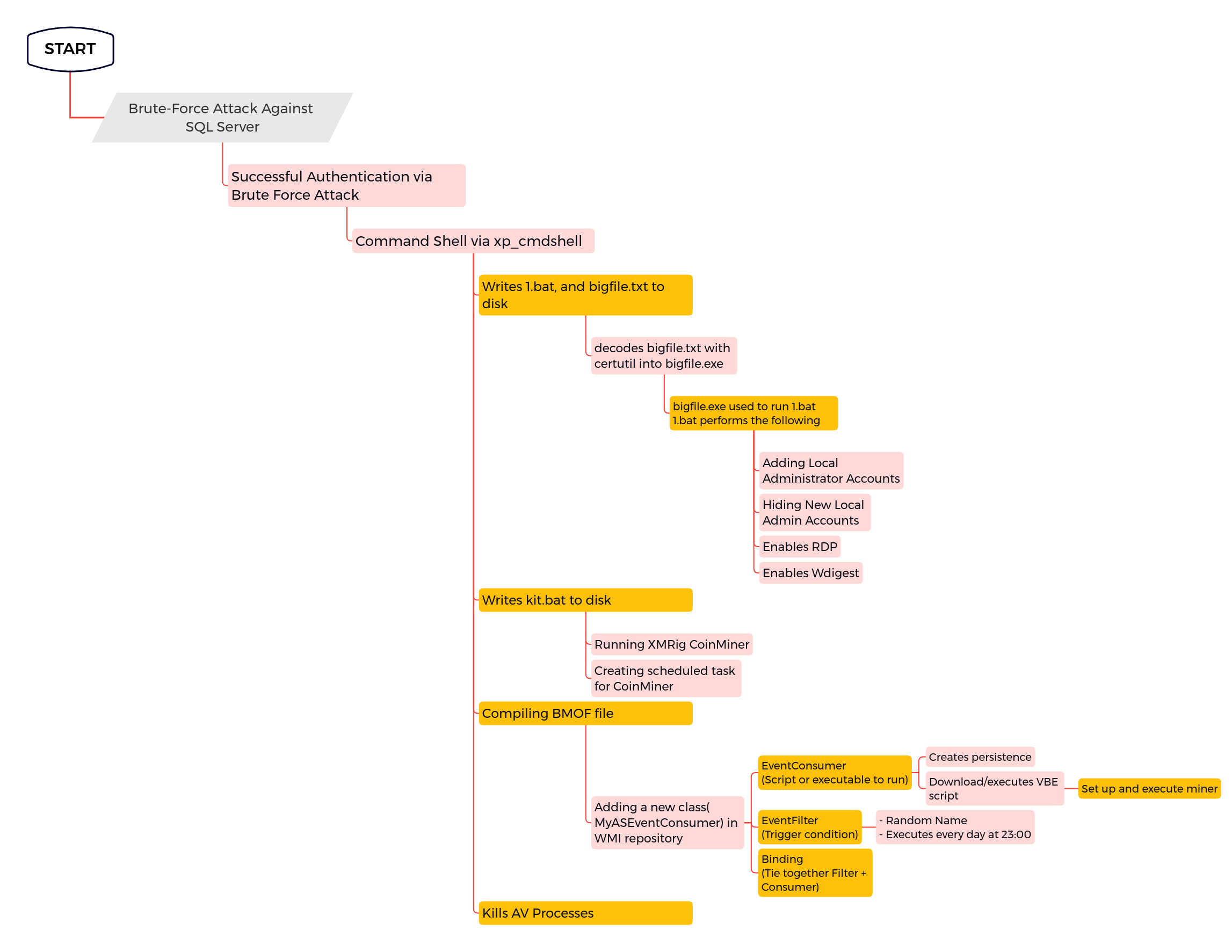
7 - https://thedfirreport.com/2022/07/11/select-xmrig-from-sqlserver/
8author: Nasreddine Bencherchali (Nextron Systems)
9date: 2022-07-12
10modified: 2024-06-26
11tags:
12 - attack.execution
13logsource:
14 product: windows
15 service: application
16 definition: 'Requirements: MSSQL audit policy to monitor for "xp_cmdshell" must be enabled in order to receive this event in the application log (Follow this tutorial https://dba.stackexchange.com/questions/103183/is-there-any-way-to-monitor-execution-of-xp-cmdshell-in-sql-server-2012)'
17 # warning: The 'data' field used in the detection section is the container for the event data as a whole. You may have to adapt the rule for your backend accordingly
18detection:
19 selection:
20 Provider_Name|contains: 'MSSQL' # Note: We use contains to account for other third party providers - See https://github.com/SigmaHQ/sigma/issues/4876
21 EventID: 33205
22 Data|contains|all:
23 # You can modify this to include specific commands
24 - 'object_name:xp_cmdshell'
25 - 'statement:EXEC'
26 condition: selection
27falsepositives:
28 - Unknown
29level: high
References
Related rules
- AWS EC2 Startup Shell Script Change
- Abusable DLL Potential Sideloading From Suspicious Location
- Add Windows Capability Via PowerShell Cmdlet
- Add Windows Capability Via PowerShell Script
- Adwind RAT / JRAT