Potential CVE-2021-42287 Exploitation Attempt
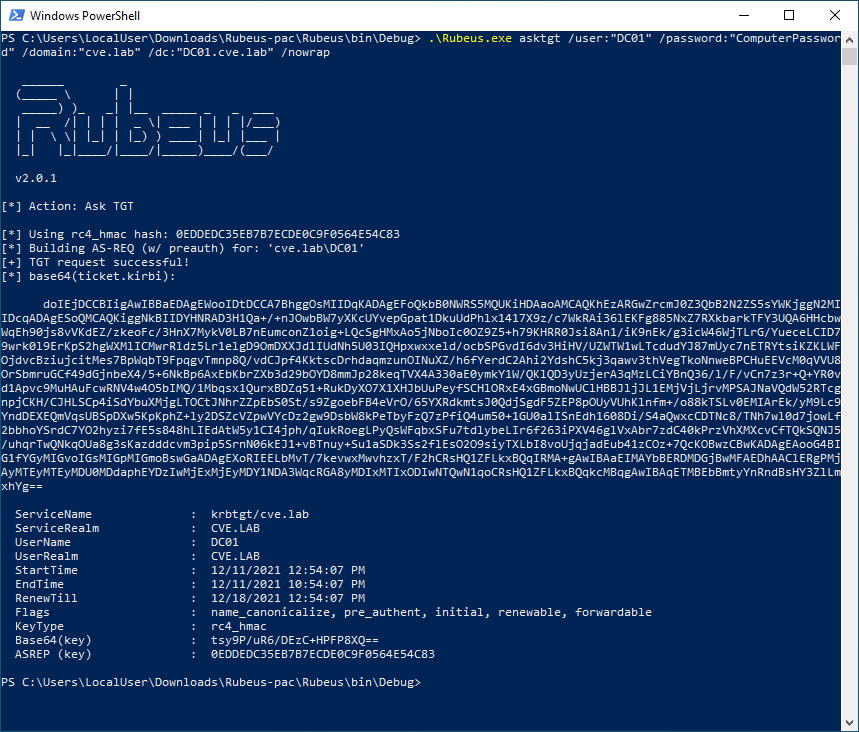
The attacker creates a computer object using those permissions with a password known to her. After that she clears the attribute ServicePrincipalName on the computer object. Because she created the object (CREATOR OWNER), she gets granted additional permissions and can do many changes to the object.
Sigma rule (View on GitHub)
1title: Potential CVE-2021-42287 Exploitation Attempt
2id: e80a0fee-1a62-4419-b31e-0d0db6e6013a
3related:
4 - id: 44bbff3e-4ca3-452d-a49a-6efa4cafa06f
5 type: similar
6status: test
7description: |
8 The attacker creates a computer object using those permissions with a password known to her.
9 After that she clears the attribute ServicePrincipalName on the computer object.
10 Because she created the object (CREATOR OWNER), she gets granted additional permissions and can do many changes to the object.
11references:
12 - https://cloudbrothers.info/en/exploit-kerberos-samaccountname-spoofing/
13author: frack113
14date: 2021-12-15
15modified: 2023-04-14
16tags:
17 - attack.credential-access
18 - attack.t1558.003
19 - detection.emerging-threats
20 - cve.2021-42287
21logsource:
22 product: windows
23 service: system
24detection:
25 selection:
26 Provider_Name: Microsoft-Windows-Directory-Services-SAM # Active Directory
27 EventID:
28 - 16990 # Object class and UserAccountControl validation failure
29 - 16991 # SAM Account Name validation failure
30 condition: selection
31falsepositives:
32 - Unknown
33level: medium
References
Related rules
- Kerberoasting Activity - Initial Query
- APT31 Judgement Panda Activity
- CVE-2021-31979 CVE-2021-33771 Exploits
- CVE-2021-31979 CVE-2021-33771 Exploits by Sourgum
- HackTool - KrbRelayUp Execution