Potential QBot Activity
Detects potential QBot activity by looking for process executions used previously by QBot
Sigma rule (View on GitHub)
1title: Potential QBot Activity
2id: 4fcac6eb-0287-4090-8eea-2602e4c20040
3status: stable
4description: Detects potential QBot activity by looking for process executions used previously by QBot
5references:
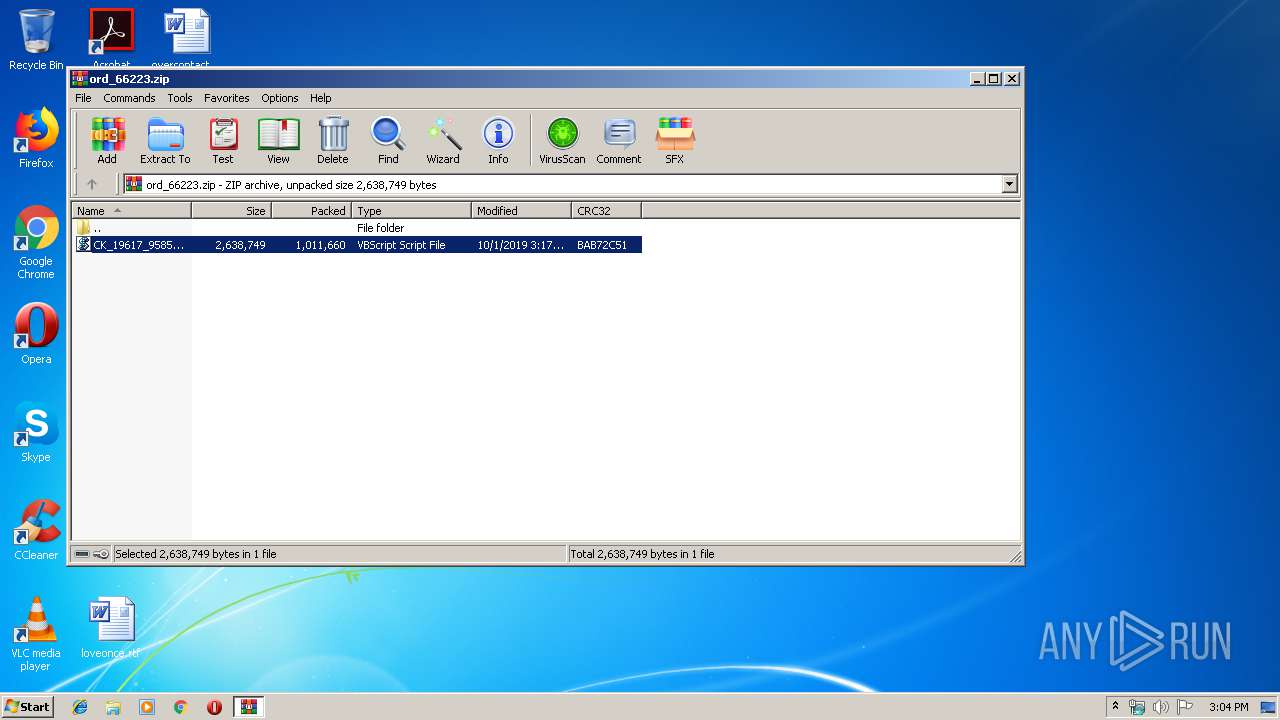
6 - https://twitter.com/killamjr/status/1179034907932315648
7 - https://app.any.run/tasks/2e0647b7-eb86-4f72-904b-d2d0ecac07d1/
8author: Florian Roth (Nextron Systems)
9date: 2019-10-01
10modified: 2023-02-03
11tags:
12 - attack.execution
13 - attack.t1059.005
14 - detection.emerging-threats
15logsource:
16 category: process_creation
17 product: windows
18detection:
19 selection1:
20 ParentImage|endswith: '\WinRAR.exe'
21 Image|endswith: '\wscript.exe'
22 selection2:
23 CommandLine|contains: ' /c ping.exe -n 6 127.0.0.1 & type '
24 selection3:
25 CommandLine|contains|all:
26 - 'regsvr32.exe'
27 - 'C:\ProgramData'
28 - '.tmp'
29 condition: 1 of selection*
30falsepositives:
31 - Unlikely
32level: critical
References
Related rules
- Adwind RAT / JRAT
- Potential APT10 Cloud Hopper Activity
- CVE-2021-1675 Print Spooler Exploitation
- CVE-2021-26858 Exchange Exploitation
- Droppers Exploiting CVE-2017-11882