Kerberos Pre-authentication Disabled for User
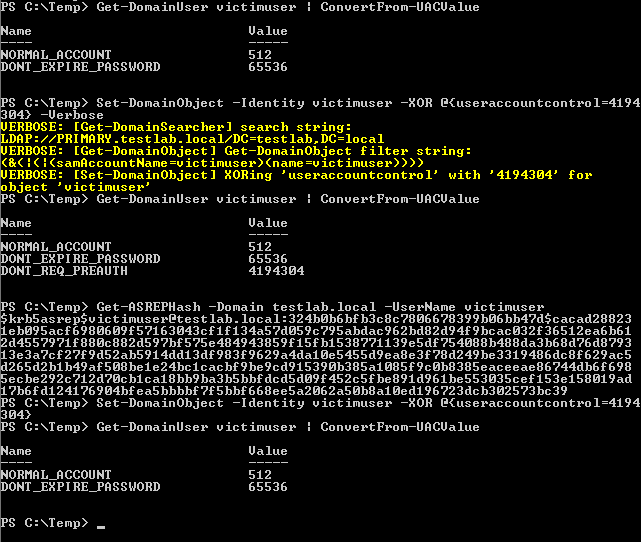
Identifies the modification of an account's Kerberos pre-authentication options. An adversary with GenericWrite/GenericAll rights over the account can maliciously modify these settings to perform offline password cracking attacks such as AS-REP roasting.
Elastic rule (View on GitHub)
1[metadata]
2creation_date = "2022/01/24"
3integration = ["system", "windows"]
4maturity = "production"
5updated_date = "2025/03/20"
6
7[rule]
8author = ["Elastic"]
9description = """
10Identifies the modification of an account's Kerberos pre-authentication options. An adversary with
11GenericWrite/GenericAll rights over the account can maliciously modify these settings to perform offline password
12cracking attacks such as AS-REP roasting.
13"""
14from = "now-9m"
15index = ["logs-system.security*", "logs-windows.forwarded*", "winlogbeat-*"]
16language = "eql"
17license = "Elastic License v2"
18name = "Kerberos Pre-authentication Disabled for User"
19note = """## Triage and analysis
20
21### Investigating Kerberos Pre-authentication Disabled for User
22
23Kerberos pre-authentication is an account protection against offline password cracking. When enabled, a user requesting access to a resource initiates communication with the Domain Controller (DC) by sending an Authentication Server Request (AS-REQ) message with a timestamp that is encrypted with the hash of their password. If and only if the DC is able to successfully decrypt the timestamp with the hash of the user’s password, it will then send an Authentication Server Response (AS-REP) message that contains the Ticket Granting Ticket (TGT) to the user. Part of the AS-REP message is signed with the user’s password. Microsoft's security monitoring [recommendations](https://docs.microsoft.com/en-us/windows/security/threat-protection/auditing/event-4738) state that `'Don't Require Preauth' – Enabled` should not be enabled for user accounts because it weakens security for the account’s Kerberos authentication.
24
25AS-REP roasting is an attack against Kerberos for user accounts that do not require pre-authentication, which means that if the target user has pre-authentication disabled, an attacker can request authentication data for it and get a TGT that can be brute-forced offline, similarly to Kerberoasting.
26
27#### Possible investigation steps
28
29- Identify the user account that performed the action and whether it should perform this kind of action.
30- Contact the account owner and confirm whether they are aware of this activity.
31- Determine if the target account is sensitive or privileged.
32- Inspect the account activities for suspicious or abnormal behaviors in the alert timeframe.
33
34### False positive analysis
35
36- Disabling pre-authentication is a bad security practice and should not be allowed in the domain. The security team should map and monitor any potential benign true positives (B-TPs), especially if the target account is privileged.
37
38### Response and remediation
39
40- Initiate the incident response process based on the outcome of the triage.
41- Reset the target account's password if there is any risk of TGTs having been retrieved.
42- Re-enable the preauthentication option or disable the target account.
43- Review the privileges assigned to the involved users to ensure that the least privilege principle is being followed.
44- Investigate credential exposure on systems compromised or used by the attacker to ensure all compromised accounts are identified. Reset passwords for these accounts and other potentially compromised credentials, such as email, business systems, and web services.
45- Using the incident response data, update logging and audit policies to improve the mean time to detect (MTTD) and the mean time to respond (MTTR).
46"""
47references = [
48 "https://harmj0y.medium.com/roasting-as-reps-e6179a65216b",
49 "https://docs.microsoft.com/en-us/windows/security/threat-protection/auditing/event-4738",
50 "https://github.com/atc-project/atomic-threat-coverage/blob/master/Atomic_Threat_Coverage/Logging_Policies/LP_0026_windows_audit_user_account_management.md",
51]
52risk_score = 47
53rule_id = "e514d8cd-ed15-4011-84e2-d15147e059f1"
54setup = """## Setup
55
56The 'Audit User Account Management' logging policy must be configured for (Success, Failure).
57Steps to implement the logging policy with Advanced Audit Configuration:
Computer Configuration > Policies > Windows Settings > Security Settings > Advanced Audit Policies Configuration > Audit Policies > Account Management > Audit User Account Management (Success,Failure)
1"""
2severity = "medium"
3tags = [
4 "Domain: Endpoint",
5 "OS: Windows",
6 "Use Case: Threat Detection",
7 "Tactic: Credential Access",
8 "Tactic: Defense Evasion",
9 "Tactic: Privilege Escalation",
10 "Resources: Investigation Guide",
11 "Use Case: Active Directory Monitoring",
12 "Data Source: Active Directory",
13 "Data Source: Windows Security Event Logs",
14]
15timestamp_override = "event.ingested"
16type = "eql"
17
18query = '''
19any where host.os.type == "windows" and event.code == "4738" and
20 winlog.event_data.NewUACList == "USER_DONT_REQUIRE_PREAUTH"
21'''
22
23
24[[rule.threat]]
25framework = "MITRE ATT&CK"
26[[rule.threat.technique]]
27id = "T1558"
28name = "Steal or Forge Kerberos Tickets"
29reference = "https://attack.mitre.org/techniques/T1558/"
30[[rule.threat.technique.subtechnique]]
31id = "T1558.004"
32name = "AS-REP Roasting"
33reference = "https://attack.mitre.org/techniques/T1558/004/"
34
35
36
37[rule.threat.tactic]
38id = "TA0006"
39name = "Credential Access"
40reference = "https://attack.mitre.org/tactics/TA0006/"
41[[rule.threat]]
42framework = "MITRE ATT&CK"
43[[rule.threat.technique]]
44id = "T1562"
45name = "Impair Defenses"
46reference = "https://attack.mitre.org/techniques/T1562/"
47
48
49[rule.threat.tactic]
50id = "TA0005"
51name = "Defense Evasion"
52reference = "https://attack.mitre.org/tactics/TA0005/"
53[[rule.threat]]
54framework = "MITRE ATT&CK"
55[[rule.threat.technique]]
56id = "T1078"
57name = "Valid Accounts"
58reference = "https://attack.mitre.org/techniques/T1078/"
59[[rule.threat.technique.subtechnique]]
60id = "T1078.002"
61name = "Domain Accounts"
62reference = "https://attack.mitre.org/techniques/T1078/002/"
63
64
65
66[rule.threat.tactic]
67id = "TA0004"
68name = "Privilege Escalation"
69reference = "https://attack.mitre.org/tactics/TA0004/"
Triage and analysis
Investigating Kerberos Pre-authentication Disabled for User
Kerberos pre-authentication is an account protection against offline password cracking. When enabled, a user requesting access to a resource initiates communication with the Domain Controller (DC) by sending an Authentication Server Request (AS-REQ) message with a timestamp that is encrypted with the hash of their password. If and only if the DC is able to successfully decrypt the timestamp with the hash of the user’s password, it will then send an Authentication Server Response (AS-REP) message that contains the Ticket Granting Ticket (TGT) to the user. Part of the AS-REP message is signed with the user’s password. Microsoft's security monitoring recommendations state that 'Don't Require Preauth' – Enabled should not be enabled for user accounts because it weakens security for the account’s Kerberos authentication.
AS-REP roasting is an attack against Kerberos for user accounts that do not require pre-authentication, which means that if the target user has pre-authentication disabled, an attacker can request authentication data for it and get a TGT that can be brute-forced offline, similarly to Kerberoasting.
Possible investigation steps
- Identify the user account that performed the action and whether it should perform this kind of action.
- Contact the account owner and confirm whether they are aware of this activity.
- Determine if the target account is sensitive or privileged.
- Inspect the account activities for suspicious or abnormal behaviors in the alert timeframe.
False positive analysis
- Disabling pre-authentication is a bad security practice and should not be allowed in the domain. The security team should map and monitor any potential benign true positives (B-TPs), especially if the target account is privileged.
Response and remediation
- Initiate the incident response process based on the outcome of the triage.
- Reset the target account's password if there is any risk of TGTs having been retrieved.
- Re-enable the preauthentication option or disable the target account.
- Review the privileges assigned to the involved users to ensure that the least privilege principle is being followed.
- Investigate credential exposure on systems compromised or used by the attacker to ensure all compromised accounts are identified. Reset passwords for these accounts and other potentially compromised credentials, such as email, business systems, and web services.
- Using the incident response data, update logging and audit policies to improve the mean time to detect (MTTD) and the mean time to respond (MTTR).
References
Related rules
- Creation of a DNS-Named Record
- Group Policy Abuse for Privilege Addition
- Potential ADIDNS Poisoning via Wildcard Record Creation
- Potential WPAD Spoofing via DNS Record Creation
- Scheduled Task Execution at Scale via GPO