Attempt to Establish VScode Remote Tunnel
Detects the execution of the VScode portable binary with the tunnel command line option indicating an attempt to establish a remote tunnel session to Github or a remote VScode instance.
Elastic rule (View on GitHub)
1[metadata]
2creation_date = "2024/09/09"
3integration = ["endpoint", "windows", "sentinel_one_cloud_funnel", "m365_defender", "system", "crowdstrike"]
4maturity = "production"
5updated_date = "2026/03/18"
6
7[rule]
8author = ["Elastic"]
9description = """
10Detects the execution of the VScode portable binary with the tunnel command line option indicating an attempt to
11establish a remote tunnel session to Github or a remote VScode instance.
12"""
13from = "now-9m"
14index = [
15 "endgame-*",
16 "logs-crowdstrike.fdr*",
17 "logs-endpoint.events.process-*",
18 "logs-m365_defender.event-*",
19 "logs-sentinel_one_cloud_funnel.*",
20 "logs-system.security*",
21 "logs-windows.sysmon_operational-*",
22 "winlogbeat-*",
23]
24language = "eql"
25license = "Elastic License v2"
26name = "Attempt to Establish VScode Remote Tunnel"
27note = """## Triage and analysis
28
29> **Disclaimer**:
30> This investigation guide was created using generative AI technology and has been reviewed to improve its accuracy and relevance. While every effort has been made to ensure its quality, we recommend validating the content and adapting it to suit your specific environment and operational needs.
31
32### Investigating Attempt to Establish VScode Remote Tunnel
33
34Visual Studio Code (VScode) offers a remote tunnel feature enabling developers to connect to remote environments seamlessly. While beneficial for legitimate remote development, adversaries can exploit this to establish unauthorized access or control over systems. The detection rule identifies suspicious use of VScode's tunnel command, focusing on specific command-line arguments and process behaviors, to flag potential misuse indicative of command and control activities.
35
36### Possible investigation steps
37
38- Review the process details to confirm the presence of the "tunnel" argument in the command line, which indicates an attempt to establish a remote tunnel session.
39- Check the parent process name to ensure it is not "Code.exe" when the process name is "code-tunnel.exe" with the "status" argument, as this is an exception in the rule.
40- Investigate the origin of the process by examining the user account and machine from which the process was initiated to determine if it aligns with expected usage patterns.
41- Analyze network logs to identify any unusual or unauthorized connections to GitHub or remote VScode instances that may suggest malicious activity.
42- Correlate the event with other security alerts or logs from data sources like Elastic Endgame, Sysmon, or Microsoft Defender for Endpoint to gather additional context on the activity.
43- Assess the risk and impact by determining if the system or user account has been involved in previous suspicious activities or if there are any indicators of compromise.
44
45### False positive analysis
46
47- Legitimate remote development activities using VScode's tunnel feature may trigger the rule. Users can create exceptions for known developer machines or specific user accounts frequently using this feature for authorized purposes.
48- Automated scripts or deployment tools that utilize VScode's remote tunnel for legitimate operations might be flagged. Consider excluding these processes by identifying their unique command-line arguments or parent processes.
49- Scheduled tasks or system maintenance activities that involve VScode's remote capabilities could be misidentified as threats. Review and whitelist these tasks by their specific execution times or associated service accounts.
50- Development environments that frequently update or test VScode extensions might inadvertently match the rule's criteria. Exclude these environments by setting up exceptions based on their network segments or IP addresses.
51- Training or demonstration sessions using VScode's remote features for educational purposes can be mistaken for suspicious activity. Implement exclusions for these sessions by tagging them with specific event identifiers or user roles.
52
53### Response and remediation
54
55- Immediately isolate the affected system from the network to prevent further unauthorized access or data exfiltration.
56- Terminate any suspicious VScode processes identified by the detection rule to halt potential command and control activities.
57- Conduct a thorough review of system logs and process histories to identify any additional indicators of compromise or lateral movement attempts.
58- Reset credentials and access tokens associated with the affected system and any connected services to mitigate unauthorized access.
59- Restore the system from a known good backup if any unauthorized changes or malware are detected.
60- Implement network segmentation to limit the ability of similar threats to spread across the environment.
61- Escalate the incident to the security operations center (SOC) or incident response team for further investigation and to determine if additional systems are affected."""
62references = [
63 "https://badoption.eu/blog/2023/01/31/code_c2.html",
64 "https://code.visualstudio.com/docs/remote/tunnels",
65]
66risk_score = 47
67rule_id = "0b96dfd8-5b8c-4485-9a1c-69ff7839786a"
68severity = "medium"
69tags = [
70 "Domain: Endpoint",
71 "OS: Windows",
72 "Use Case: Threat Detection",
73 "Tactic: Command and Control",
74 "Data Source: Elastic Endgame",
75 "Data Source: Elastic Defend",
76 "Data Source: Sysmon",
77 "Data Source: SentinelOne",
78 "Data Source: Microsoft Defender for Endpoint",
79 "Data Source: Windows Security Event Logs",
80 "Data Source: Crowdstrike",
81 "Resources: Investigation Guide",
82]
83timestamp_override = "event.ingested"
84type = "eql"
85
86query = '''
87process where host.os.type == "windows" and event.type == "start" and
88 process.args : "tunnel" and
89 (process.args : "--accept-server-license-terms" or
90 process.name : "code*.exe" or
91 ?process.code_signature.subject_name : "Microsoft Corporation" or
92 process.executable : ("?:\\ProgramData\\*", "?:\\Users\\Public\\*", "?:\\windows\\debug\\*",
93 "\\Device\\HarddiskVolume*\\Users\\Public\\*", "\\Device\\HarddiskVolume*\\ProgramData\\*", "\\Device\\HarddiskVolume*\\windows\\debug\\*")) and
94 not (process.name == "code-tunnel.exe" and process.args == "status" and process.parent.name == "Code.exe")
95'''
96
97
98[[rule.threat]]
99framework = "MITRE ATT&CK"
100[[rule.threat.technique]]
101id = "T1219"
102name = "Remote Access Tools"
103reference = "https://attack.mitre.org/techniques/T1219/"
104
105
106[rule.threat.tactic]
107id = "TA0011"
108name = "Command and Control"
109reference = "https://attack.mitre.org/tactics/TA0011/"
Triage and analysis
Disclaimer: This investigation guide was created using generative AI technology and has been reviewed to improve its accuracy and relevance. While every effort has been made to ensure its quality, we recommend validating the content and adapting it to suit your specific environment and operational needs.
Investigating Attempt to Establish VScode Remote Tunnel
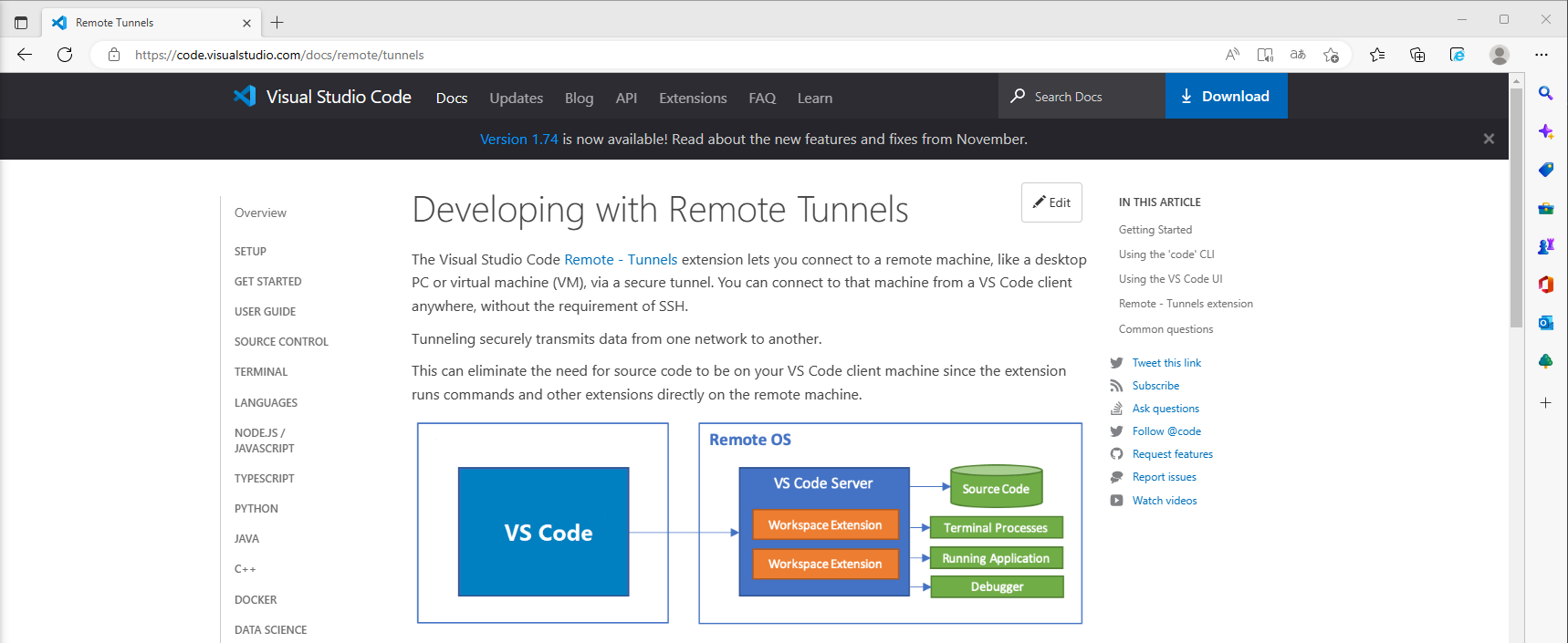
Visual Studio Code (VScode) offers a remote tunnel feature enabling developers to connect to remote environments seamlessly. While beneficial for legitimate remote development, adversaries can exploit this to establish unauthorized access or control over systems. The detection rule identifies suspicious use of VScode's tunnel command, focusing on specific command-line arguments and process behaviors, to flag potential misuse indicative of command and control activities.
Possible investigation steps
- Review the process details to confirm the presence of the "tunnel" argument in the command line, which indicates an attempt to establish a remote tunnel session.
- Check the parent process name to ensure it is not "Code.exe" when the process name is "code-tunnel.exe" with the "status" argument, as this is an exception in the rule.
- Investigate the origin of the process by examining the user account and machine from which the process was initiated to determine if it aligns with expected usage patterns.
- Analyze network logs to identify any unusual or unauthorized connections to GitHub or remote VScode instances that may suggest malicious activity.
- Correlate the event with other security alerts or logs from data sources like Elastic Endgame, Sysmon, or Microsoft Defender for Endpoint to gather additional context on the activity.
- Assess the risk and impact by determining if the system or user account has been involved in previous suspicious activities or if there are any indicators of compromise.
False positive analysis
- Legitimate remote development activities using VScode's tunnel feature may trigger the rule. Users can create exceptions for known developer machines or specific user accounts frequently using this feature for authorized purposes.
- Automated scripts or deployment tools that utilize VScode's remote tunnel for legitimate operations might be flagged. Consider excluding these processes by identifying their unique command-line arguments or parent processes.
- Scheduled tasks or system maintenance activities that involve VScode's remote capabilities could be misidentified as threats. Review and whitelist these tasks by their specific execution times or associated service accounts.
- Development environments that frequently update or test VScode extensions might inadvertently match the rule's criteria. Exclude these environments by setting up exceptions based on their network segments or IP addresses.
- Training or demonstration sessions using VScode's remote features for educational purposes can be mistaken for suspicious activity. Implement exclusions for these sessions by tagging them with specific event identifiers or user roles.
Response and remediation
- Immediately isolate the affected system from the network to prevent further unauthorized access or data exfiltration.
- Terminate any suspicious VScode processes identified by the detection rule to halt potential command and control activities.
- Conduct a thorough review of system logs and process histories to identify any additional indicators of compromise or lateral movement attempts.
- Reset credentials and access tokens associated with the affected system and any connected services to mitigate unauthorized access.
- Restore the system from a known good backup if any unauthorized changes or malware are detected.
- Implement network segmentation to limit the ability of similar threats to spread across the environment.
- Escalate the incident to the security operations center (SOC) or incident response team for further investigation and to determine if additional systems are affected.
References
Related rules
- Potential Protocol Tunneling via Cloudflared
- Potential Protocol Tunneling via Yuze
- Suspicious Shell Execution via Velociraptor
- Potential Traffic Tunneling using QEMU
- Suspicious Execution from INET Cache