Execution via GitHub Actions Runner
This rule detects potentially dangerous commands spawned by the GitHub Actions Runner.Worker process or by shell interpreters launched via a runner entrypoint script on self-hosted runner machines. Adversaries who gain the ability to modify or trigger workflows in a linked GitHub repository can execute arbitrary commands on the runner host. This behavior may indicate malicious or unexpected workflow activity, including code execution, reconnaissance, credential harvesting, or network exfiltration initiated through a compromised repository or unauthorized workflow.
Elastic rule (View on GitHub)
1[metadata]
2creation_date = "2025/11/26"
3integration = ["endpoint", "windows", "system", "m365_defender", "sentinel_one_cloud_funnel", "crowdstrike", "auditd_manager"]
4maturity = "production"
5updated_date = "2026/04/22"
6
7
8[rule]
9author = ["Elastic"]
10description = """
11This rule detects potentially dangerous commands spawned by the GitHub Actions Runner.Worker process or by shell
12interpreters launched via a runner entrypoint script on self-hosted runner machines. Adversaries who gain the ability
13to modify or trigger workflows in a linked GitHub repository can execute arbitrary commands on the runner host. This
14behavior may indicate malicious or unexpected workflow activity, including code execution, reconnaissance, credential
15harvesting, or network exfiltration initiated through a compromised repository or unauthorized workflow.
16"""
17false_positives = [
18 "Authorized GitHub actions runner with no malicious workflow actions.",
19]
20from = "now-9m"
21index = [
22 "endgame-*",
23 "logs-crowdstrike.fdr*",
24 "logs-endpoint.events.process-*",
25 "logs-m365_defender.event-*",
26 "logs-sentinel_one_cloud_funnel.*",
27 "logs-system.security*",
28 "logs-windows.forwarded*",
29 "logs-windows.sysmon_operational-*",
30 "winlogbeat-*",
31 "auditbeat-*",
32 "logs-auditd_manager.auditd-*"
33]
34language = "eql"
35license = "Elastic License v2"
36name = "Execution via GitHub Actions Runner"
37note = """## Triage and analysis
38
39### Investigating Execution via GitHub Actions Runner
40
41Adversaries who gain the ability to modify or trigger workflows in a linked GitHub repository can execute arbitrary
42commands on the runner host. This rule covers two parent process paths:
43- **Direct execution**: process spawned directly by `Runner.Worker` / `Runner.Worker.exe`.
44- **Entrypoint script execution**: process spawned by a shell (`sh`, `bash`, `zsh`) whose command line references
45 a runner `entrypoint.sh` script, a common pattern when the runner bootstraps workflow steps via a shell script.
46
47### Possible investigation steps
48
49- Review `process.command_line` and `process.parent.command_line` to determine whether the activity matches a known,
50 authorized workflow step.
51- For `grep`, `find`, `pgrep`, `printenv`, and `env` hits, assess whether the command targets sensitive paths, environment
52 variables (e.g. secrets, tokens), or process listings inconsistent with the declared workflow.
53- For `openssl` and `base64` hits, inspect arguments for encoding/decoding operations that may indicate credential
54 harvesting, data staging, or a C2 channel.
55- For `tr` and `cat` hits, assess whether they are chained with other suspicious commands (e.g. `cat /etc/passwd | base64`,
56 `cat ~/.ssh/id_rsa`) to read and encode sensitive files for exfiltration.
57- For `nc`, `ncat`, `netcat`, and `socat` hits, check arguments for reverse shell patterns or port-forwarding to
58 attacker-controlled infrastructure.
59- For `wg` and `wg-quick` hits, inspect arguments for tunnel configuration that may establish a covert egress channel.
60- For `ssh` hits, review arguments for reverse tunnel flags (`-R`) or connections to unexpected remote hosts.
61- For `kubectl` and `helm` hits, assess whether commands target sensitive namespaces, extract secrets, or deploy
62 workloads inconsistent with the declared workflow.
63- For `vault` hits, inspect arguments for secret reads (`vault kv get`) or token operations that may indicate
64 credential harvesting from a HashiCorp Vault instance.
65- For `gh` hits, review arguments for repository cloning, secret access (`gh secret`), or actions that escalate
66 access via the runner's GitHub token.
67- For `nmap` hits, assess whether the command performs host or port discovery against internal network ranges,
68 indicating lateral movement preparation.
69- Examine associated network activity for unexpected outbound connections, especially following `curl`, `wget`, or
70 `openssl s_client` invocations.
71- Verify whether the triggering workflow run was initiated by an authorized actor and matches the repository's
72 expected workflow definitions.
73- Correlate with file-write and file-access events to identify any sensitive file staging or collection activity.
74- Correlate with other alerts to determine if this activity is part of a broader supply chain or CI/CD compromise.
75
76### False positive analysis
77
78- Authorized GitHub workflow actions that legitimately use discovery utilities (`find`, `grep`, `env`, `nmap`), data
79 manipulation tools (`cat`, `tr`), encoding tools (`openssl`, `base64`), remote access tools (`ssh`), or
80 infrastructure CLIs (`kubectl`, `helm`, `vault`, `gh`) as part of their build, test, or deploy steps may trigger
81 this rule. Validate against known workflow definitions and consider adding workflow-specific exclusions if the
82 volume is high.
83
84### Response and remediation
85
86- Immediately isolate the affected system from the network to prevent further unauthorized command execution and potential lateral movement.
87- Terminate any suspicious child processes that were initiated by the Github actions runner.
88- Conduct a thorough review of the affected system's logs and configurations to identify any unauthorized changes or additional indicators of compromise.
89- Restore the system from a known good backup if any unauthorized changes or malicious activities are confirmed.
90- Implement application whitelisting to prevent unauthorized execution.
91- Escalate the incident to the security operations center (SOC) or incident response team for further investigation and to assess the potential impact on the broader network."""
92references = [
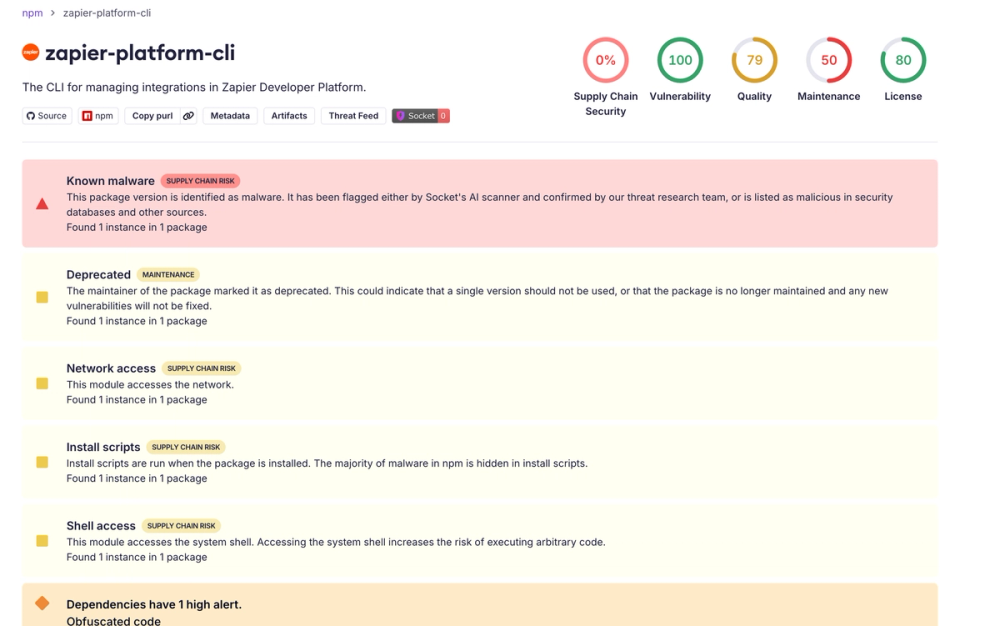
93 "https://www.elastic.co/blog/shai-hulud-worm-npm-supply-chain-compromise",
94 "https://socket.dev/blog/shai-hulud-strikes-again-v2",
95]
96risk_score = 47
97rule_id = "a640ef5b-e1da-4b17-8391-468fdbd1b517"
98severity = "medium"
99tags = [
100 "Domain: Endpoint",
101 "OS: Linux",
102 "OS: Windows",
103 "OS: macOS",
104 "Use Case: Threat Detection",
105 "Tactic: Execution",
106 "Tactic: Initial Access",
107 "Data Source: Elastic Endgame",
108 "Data Source: Elastic Defend",
109 "Data Source: Windows Security Event Logs",
110 "Data Source: Microsoft Defender XDR",
111 "Data Source: Sysmon",
112 "Data Source: SentinelOne",
113 "Data Source: Crowdstrike",
114 "Data Source: Auditd Manager",
115 "Resources: Investigation Guide",
116]
117timestamp_override = "event.ingested"
118type = "eql"
119
120query = '''
121process where event.type == "start" and event.action in ("exec", "exec_event", "start", "ProcessRollup2", "executed", "process_started") and
122 (
123 /* Direct child of the GitHub Actions Runner.Worker process */
124 process.parent.name in ("Runner.Worker", "Runner.Worker.exe") or
125
126 /* Child of a shell interpreter launched via a runner entrypoint script
127 (e.g. /home/runner/runners/<ver>/run/entrypoint.sh or similar paths) */
128 (
129 process.parent.name in ("sh", "bash", "zsh") and
130 process.parent.command_line like "*runner*entrypoint.sh"
131 )
132 ) and
133 (
134 process.name : (
135 /* Network / download utilities */
136 "curl", "curl.exe", "wget", "wget.exe",
137 /* Windows scripting & LOLBins */
138 "powershell.exe", "cmd.exe", "pwsh.exe", "certutil.exe", "rundll32.exe",
139 /* Unix shells */
140 "bash", "sh", "zsh", "dash", "ash", "tcsh", "csh", "ksh", "fish", "mksh", "busybox", "pwsh",
141 /* File / archive manipulation */
142 "tar", "gzip", "rm", "sed", "chmod",
143 /* macOS-specific */
144 "osascript",
145 /* Process persistence helpers */
146 "nohup", "setsid",
147 /* Scripting runtimes */
148 "python*", "perl*", "ruby*", "lua*", "php*", "node", "nodejs", "node.exe",
149 /* Discovery & reconnaissance */
150 "pgrep", "grep", "find", "printenv", "env", "nmap",
151 /* Crypto / encoding (potential exfiltration or C2 channel) */
152 "openssl", "base64", "basez", "base64plain", "base64url", "base64mime", "base64pem", "basenc", "base32", "base16", "xxd",
153 /* Data manipulation / inspection */
154 "tr", "cat",
155 /* Network relay / tunneling */
156 "nc", "ncat", "netcat", "nc.traditional", "nc.openbsd", "socat", "wg", "wg-quick",
157 /* Remote access */
158 "ssh", "ssh.exe", "ftp", "tftp", "scp", "sftp",
159 /* Kubernetes / infrastructure */
160 "kubectl", "helm", "docker", "ctr", "crictl",
161 /* Secret management */
162 "vault",
163 /* GitHub CLI */
164 "gh",
165 /* AWS CLI */
166 "aws",
167 /*Azure CLI */
168 "az",
169 /*GCP CLI */
170 "gcloud",
171 /* Google Workspace CLI */
172 "gws"
173 ) or
174 process.executable : ("/tmp/*", "/private/tmp/*", "/var/tmp/*", "/dev/shm/*", "/run/*", "/var/run/*", "?:\\Users\\*")
175 )
176'''
177
178
179[[rule.threat]]
180framework = "MITRE ATT&CK"
181
182[[rule.threat.technique]]
183id = "T1059"
184name = "Command and Scripting Interpreter"
185reference = "https://attack.mitre.org/techniques/T1059/"
186
187[[rule.threat.technique.subtechnique]]
188id = "T1059.001"
189name = "PowerShell"
190reference = "https://attack.mitre.org/techniques/T1059/001/"
191
192[[rule.threat.technique.subtechnique]]
193id = "T1059.002"
194name = "AppleScript"
195reference = "https://attack.mitre.org/techniques/T1059/002/"
196
197[[rule.threat.technique.subtechnique]]
198id = "T1059.003"
199name = "Windows Command Shell"
200reference = "https://attack.mitre.org/techniques/T1059/003/"
201
202[[rule.threat.technique.subtechnique]]
203id = "T1059.004"
204name = "Unix Shell"
205reference = "https://attack.mitre.org/techniques/T1059/004/"
206
207[[rule.threat.technique.subtechnique]]
208id = "T1059.006"
209name = "Python"
210reference = "https://attack.mitre.org/techniques/T1059/006/"
211
212[[rule.threat.technique.subtechnique]]
213id = "T1059.007"
214name = "JavaScript"
215reference = "https://attack.mitre.org/techniques/T1059/007/"
216
217[rule.threat.tactic]
218id = "TA0002"
219name = "Execution"
220reference = "https://attack.mitre.org/tactics/TA0002/"
221
222[[rule.threat]]
223framework = "MITRE ATT&CK"
224
225[[rule.threat.technique]]
226id = "T1195"
227name = "Supply Chain Compromise"
228reference = "https://attack.mitre.org/techniques/T1195/"
229
230[[rule.threat.technique.subtechnique]]
231id = "T1195.002"
232name = "Compromise Software Supply Chain"
233reference = "https://attack.mitre.org/techniques/T1195/002/"
234
235[rule.threat.tactic]
236id = "TA0001"
237name = "Initial Access"
238reference = "https://attack.mitre.org/tactics/TA0001/"
239
240[[rule.threat]]
241framework = "MITRE ATT&CK"
242
243[[rule.threat.technique]]
244id = "T1218"
245name = "System Binary Proxy Execution"
246reference = "https://attack.mitre.org/techniques/T1218/"
247
248[[rule.threat.technique.subtechnique]]
249id = "T1218.011"
250name = "Rundll32"
251reference = "https://attack.mitre.org/techniques/T1218/011/"
252
253[rule.threat.tactic]
254id = "TA0005"
255name = "Defense Evasion"
256reference = "https://attack.mitre.org/tactics/TA0005/"
Triage and analysis
Investigating Execution via GitHub Actions Runner
Adversaries who gain the ability to modify or trigger workflows in a linked GitHub repository can execute arbitrary commands on the runner host. This rule covers two parent process paths:
- Direct execution: process spawned directly by
Runner.Worker/Runner.Worker.exe. - Entrypoint script execution: process spawned by a shell (
sh,bash,zsh) whose command line references a runnerentrypoint.shscript, a common pattern when the runner bootstraps workflow steps via a shell script.
Possible investigation steps
- Review
process.command_lineandprocess.parent.command_lineto determine whether the activity matches a known, authorized workflow step. - For
grep,find,pgrep,printenv, andenvhits, assess whether the command targets sensitive paths, environment variables (e.g. secrets, tokens), or process listings inconsistent with the declared workflow. - For
opensslandbase64hits, inspect arguments for encoding/decoding operations that may indicate credential harvesting, data staging, or a C2 channel. - For
trandcathits, assess whether they are chained with other suspicious commands (e.g.cat /etc/passwd | base64,cat ~/.ssh/id_rsa) to read and encode sensitive files for exfiltration. - For
nc,ncat,netcat, andsocathits, check arguments for reverse shell patterns or port-forwarding to attacker-controlled infrastructure. - For
wgandwg-quickhits, inspect arguments for tunnel configuration that may establish a covert egress channel. - For
sshhits, review arguments for reverse tunnel flags (-R) or connections to unexpected remote hosts. - For
kubectlandhelmhits, assess whether commands target sensitive namespaces, extract secrets, or deploy workloads inconsistent with the declared workflow. - For
vaulthits, inspect arguments for secret reads (vault kv get) or token operations that may indicate credential harvesting from a HashiCorp Vault instance. - For
ghhits, review arguments for repository cloning, secret access (gh secret), or actions that escalate access via the runner's GitHub token. - For
nmaphits, assess whether the command performs host or port discovery against internal network ranges, indicating lateral movement preparation. - Examine associated network activity for unexpected outbound connections, especially following
curl,wget, oropenssl s_clientinvocations. - Verify whether the triggering workflow run was initiated by an authorized actor and matches the repository's expected workflow definitions.
- Correlate with file-write and file-access events to identify any sensitive file staging or collection activity.
- Correlate with other alerts to determine if this activity is part of a broader supply chain or CI/CD compromise.
False positive analysis
- Authorized GitHub workflow actions that legitimately use discovery utilities (
find,grep,env,nmap), data manipulation tools (cat,tr), encoding tools (openssl,base64), remote access tools (ssh), or infrastructure CLIs (kubectl,helm,vault,gh) as part of their build, test, or deploy steps may trigger this rule. Validate against known workflow definitions and consider adding workflow-specific exclusions if the volume is high.
Response and remediation
- Immediately isolate the affected system from the network to prevent further unauthorized command execution and potential lateral movement.
- Terminate any suspicious child processes that were initiated by the Github actions runner.
- Conduct a thorough review of the affected system's logs and configurations to identify any unauthorized changes or additional indicators of compromise.
- Restore the system from a known good backup if any unauthorized changes or malicious activities are confirmed.
- Implement application whitelisting to prevent unauthorized execution.
- Escalate the incident to the security operations center (SOC) or incident response team for further investigation and to assess the potential impact on the broader network.
References
Related rules
- Remote GitHub Actions Runner Registration
- Credential Access via TruffleHog Execution
- Potential Secret Scanning via Gitleaks
- Kubernetes Direct API Request via Curl or Wget
- Potential Traffic Tunneling using QEMU