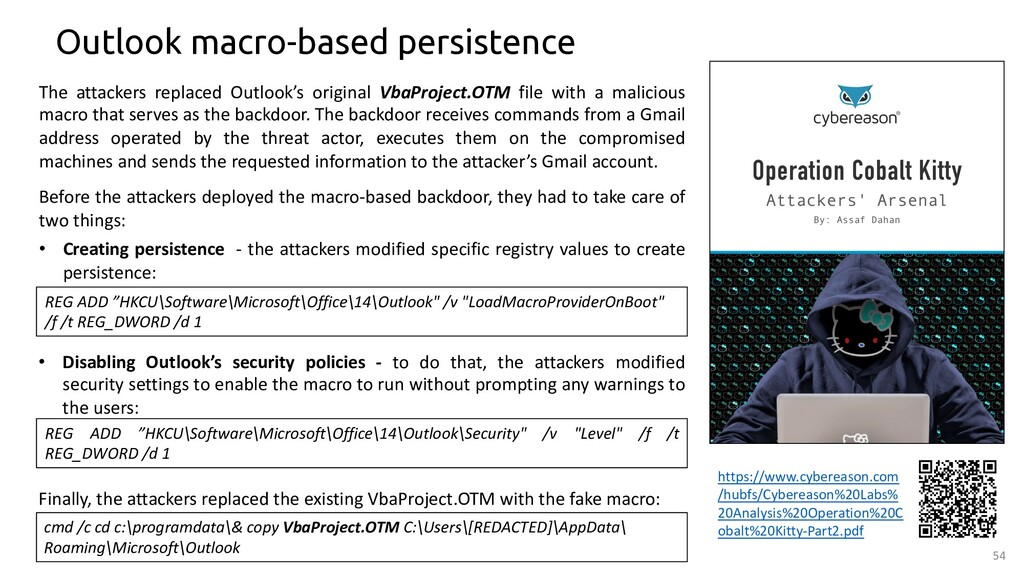
Outlook Macro Execution Without Warning Setting Enabled
Detects the modification of Outlook security setting to allow unprompted execution of macros.
Sigma rule (View on GitHub)
1title: Outlook Macro Execution Without Warning Setting Enabled
2id: e3b50fa5-3c3f-444e-937b-0a99d33731cd
3status: test
4description: Detects the modification of Outlook security setting to allow unprompted execution of macros.
5references:
6 - https://www.mdsec.co.uk/2020/11/a-fresh-outlook-on-mail-based-persistence/
7 - https://speakerdeck.com/heirhabarov/hunting-for-persistence-via-microsoft-exchange-server-or-outlook?slide=53
8author: '@ScoubiMtl'
9date: 2021-04-05
10modified: 2023-08-17
11tags:
12 - attack.privilege-escalation
13 - attack.persistence
14 - attack.command-and-control
15 - attack.t1137
16 - attack.t1008
17 - attack.t1546
18logsource:
19 category: registry_set
20 product: windows
21detection:
22 selection:
23 TargetObject|endswith: '\Outlook\Security\Level'
24 Details|contains: '0x00000001' # Enable all Macros
25 condition: selection
26falsepositives:
27 - Unlikely
28level: high
References
Related rules
- New Outlook Macro Created
- Potential Persistence Via Outlook LoadMacroProviderOnBoot Setting
- Suspicious Outlook Macro Created
- COM Hijack via Sdclt
- Control Panel Items