Chopper Webshell Process Pattern
Detects patterns found in process executions cause by China Chopper like tiny (ASPX) webshells
Sigma rule (View on GitHub)
1title: Chopper Webshell Process Pattern
2id: fa3c117a-bc0d-416e-a31b-0c0e80653efb
3status: test
4description: Detects patterns found in process executions cause by China Chopper like tiny (ASPX) webshells
5references:
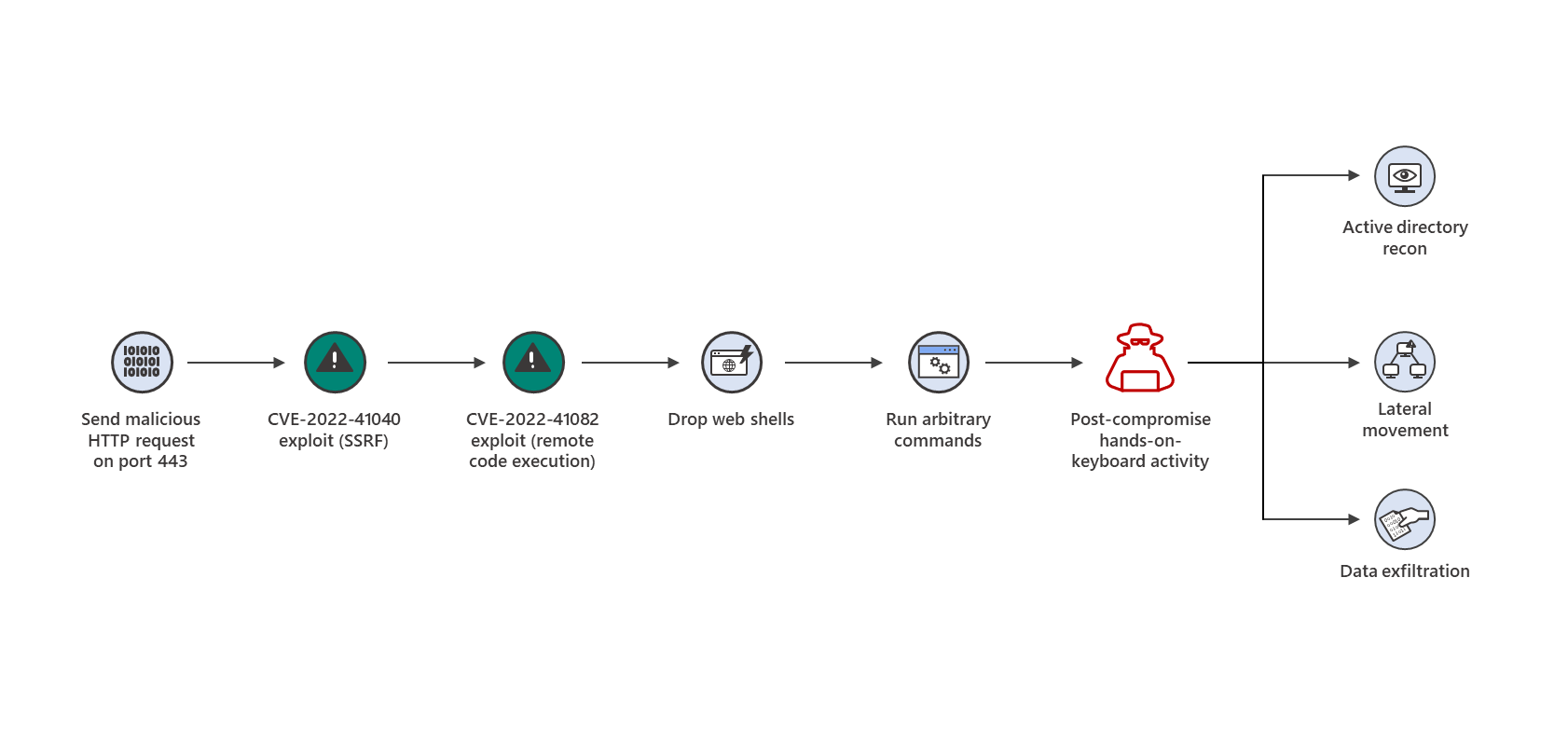
6 - https://www.microsoft.com/security/blog/2022/09/30/analyzing-attacks-using-the-exchange-vulnerabilities-cve-2022-41040-and-cve-2022-41082/
7author: Florian Roth (Nextron Systems), MSTI (query)
8date: 2022-10-01
9tags:
10 - attack.persistence
11 - attack.discovery
12 - attack.t1505.003
13 - attack.t1018
14 - attack.t1033
15 - attack.t1087
16logsource:
17 category: process_creation
18 product: windows
19detection:
20 selection_origin:
21 - Image|endswith: '\w3wp.exe'
22 - ParentImage|endswith: '\w3wp.exe'
23 selection_cmdline:
24 CommandLine|contains:
25 - '&ipconfig&echo'
26 - '&quser&echo'
27 - '&whoami&echo'
28 - '&c:&echo'
29 - '&cd&echo'
30 - '&dir&echo'
31 - '&echo [E]'
32 - '&echo [S]'
33 condition: all of selection_*
34falsepositives:
35 - Unknown
36level: high
References
Related rules
- Webshell Detection With Command Line Keywords
- Webshell Hacking Activity Patterns
- Cisco Discovery
- HackTool - winPEAS Execution
- Whoami.EXE Execution Anomaly