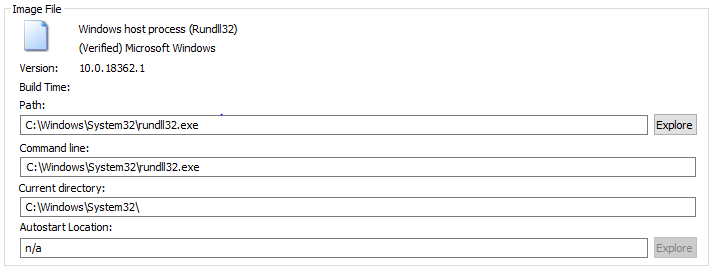
Rundll32 Registered COM Objects
load malicious registered COM objects
Sigma rule (View on GitHub)
1title: Rundll32 Registered COM Objects
2id: f1edd233-30b5-4823-9e6a-c4171b24d316
3status: test
4description: load malicious registered COM objects
5references:
6 - https://nasbench.medium.com/a-deep-dive-into-rundll32-exe-642344b41e90
7 - https://github.com/redcanaryco/atomic-red-team/blob/f339e7da7d05f6057fdfcdd3742bfcf365fee2a9/atomics/T1546.015/T1546.015.md
8author: frack113
9date: 2022-02-13
10modified: 2023-02-09
11tags:
12 - attack.privilege-escalation
13 - attack.persistence
14 - attack.t1546.015
15logsource:
16 category: process_creation
17 product: windows
18detection:
19 selection_img:
20 - Image|endswith: '\rundll32.exe'
21 - OriginalFileName: 'RUNDLL32.EXE'
22 selection_cli:
23 CommandLine|contains:
24 - '-sta '
25 - '-localserver '
26 CommandLine|contains|all:
27 - '{'
28 - '}'
29 condition: all of selection_*
30falsepositives:
31 - Legitimate use
32level: high
References
Related rules
- SOURGUM Actor Behaviours
- Suspicious GetTypeFromCLSID ShellExecute
- Abuse of Service Permissions to Hide Services Via Set-Service
- Abuse of Service Permissions to Hide Services Via Set-Service - PS
- Activity From Anonymous IP Address