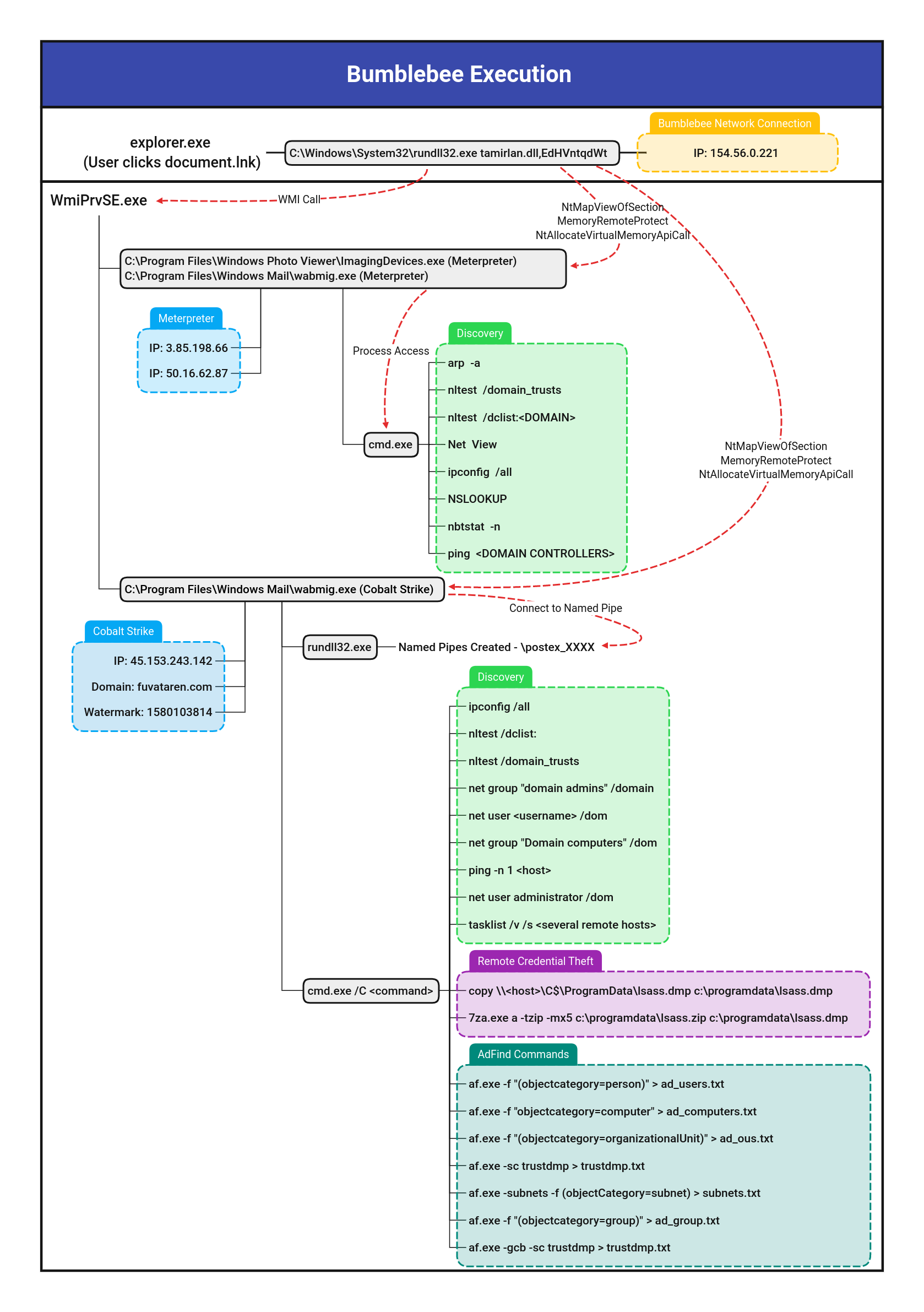
Rundll32 Spawned Via Explorer.EXE
Detects execution of "rundll32.exe" with a parent process of Explorer.exe. This has been observed by variants of Raspberry Robin, as first reported by Red Canary.
Sigma rule (View on GitHub)
1title: Rundll32 Spawned Via Explorer.EXE
2id: 1723e720-616d-4ddc-ab02-f7e3685a4713
3status: test
4description: Detects execution of "rundll32.exe" with a parent process of Explorer.exe. This has been observed by variants of Raspberry Robin, as first reported by Red Canary.
5references:
6 - https://redcanary.com/blog/raspberry-robin/
7 - https://thedfirreport.com/2022/09/26/bumblebee-round-two/
8author: CD_ROM_
9date: 2022-05-21
10modified: 2023-08-31
11tags:
12 - attack.defense-evasion
13logsource:
14 category: process_creation
15 product: windows
16detection:
17 selection_parent:
18 ParentImage|endswith: '\explorer.exe'
19 selection_img:
20 - Image|endswith: '\rundll32.exe'
21 - OriginalFileName: 'RUNDLL32.EXE'
22 filter_main_generic:
23 - CommandLine|contains: ' C:\Windows\System32\' # The space at the start is required
24 - CommandLine|endswith: ' -localserver 22d8c27b-47a1-48d1-ad08-7da7abd79617' # Windows 10 volume control
25 condition: all of selection_* and not 1 of filter_main_*
26falsepositives:
27 - Unknown
28level: medium
References
Related rules
- AD Object WriteDAC Access
- AMSI Bypass Pattern Assembly GetType
- APT PRIVATELOG Image Load Pattern
- APT29 2018 Phishing Campaign CommandLine Indicators
- APT29 2018 Phishing Campaign File Indicators