Hiding User Account Via SpecialAccounts Registry Key - CommandLine
Detects changes to the registry key "HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\SpecialAccounts\Userlist" where the value is set to "0" in order to hide user account from being listed on the logon screen.
Sigma rule (View on GitHub)
1title: Hiding User Account Via SpecialAccounts Registry Key - CommandLine
2id: 9ec9fb1b-e059-4489-9642-f270c207923d
3related:
4 - id: f8aebc67-a56d-4ec9-9fbe-7b0e8b7b4efd
5 type: similar
6status: test
7description: |
8 Detects changes to the registry key "HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\SpecialAccounts\Userlist" where the value is set to "0" in order to hide user account from being listed on the logon screen.
9references:
10 - https://thedfirreport.com/2024/01/29/buzzing-on-christmas-eve-trigona-ransomware-in-3-hours/
11 - https://thedfirreport.com/2024/04/01/from-onenote-to-ransomnote-an-ice-cold-intrusion/
12 - https://thedfirreport.com/2024/04/29/from-icedid-to-dagon-locker-ransomware-in-29-days/
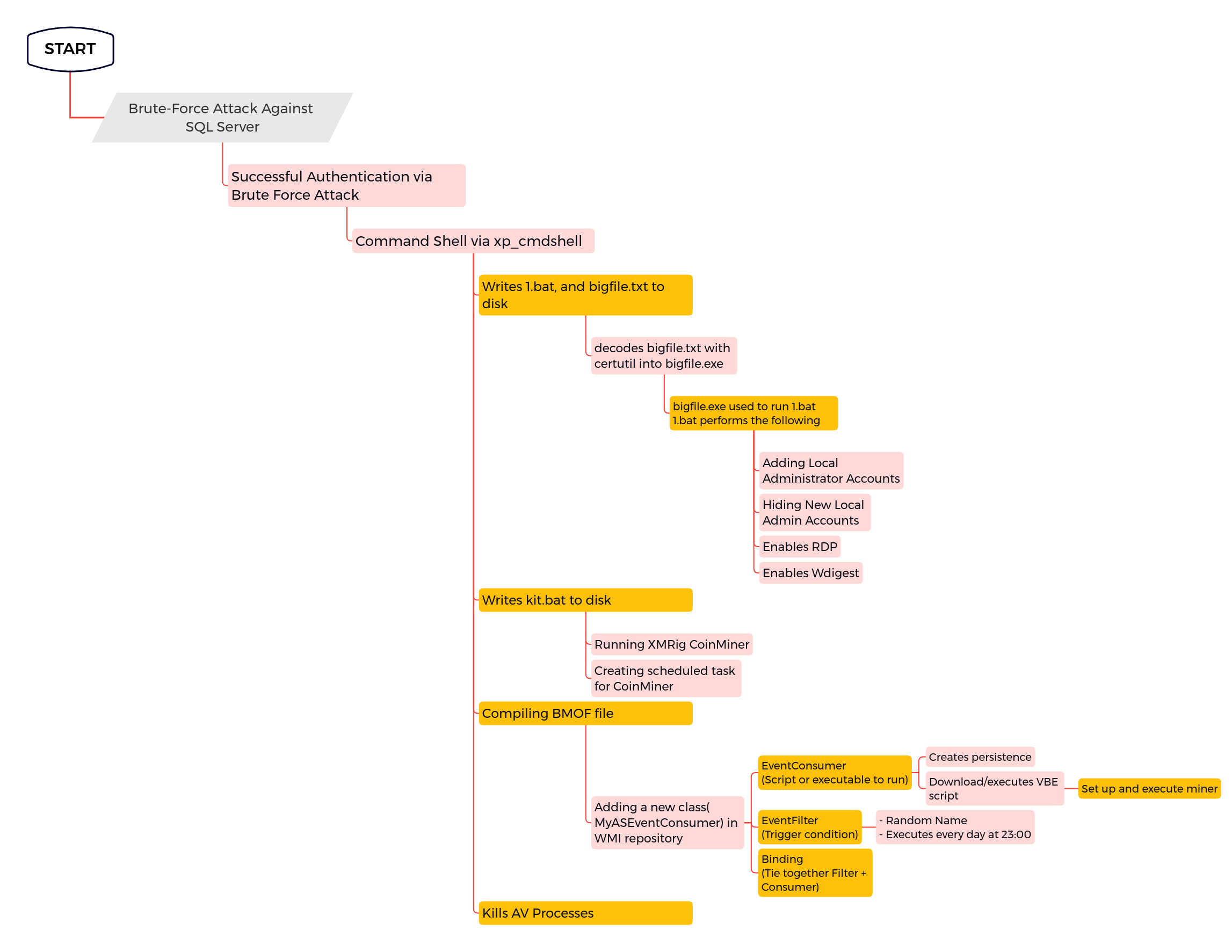
13 - https://thedfirreport.com/2022/07/11/select-xmrig-from-sqlserver/
14author: '@Kostastsale, TheDFIRReport'
15date: 2022-05-14
16modified: 2024-08-23
17tags:
18 - attack.defense-evasion
19 - attack.t1564.002
20logsource:
21 category: process_creation
22 product: windows
23detection:
24 selection:
25 Image|endswith: '\reg.exe'
26 CommandLine|contains|all:
27 - '\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\SpecialAccounts\UserList'
28 - 'add'
29 - '/v'
30 - '/d 0'
31 condition: selection
32falsepositives:
33 - System administrator activities
34level: medium
35regression_tests_path: regression_data/rules/windows/process_creation/proc_creation_win_registry_special_accounts_hide_user/info.yml
References
Related rules
- Hiding User Account Via SpecialAccounts Registry Key
- Potential Suspicious Activity Using SeCEdit
- Hidden User Creation
- Add SafeBoot Keys Via Reg Utility
- Allow RDP Remote Assistance Feature