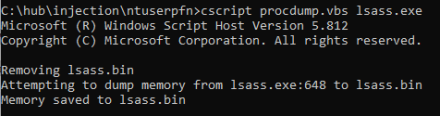
Lsass Memory Dump via Comsvcs DLL
Detects adversaries leveraging the MiniDump export function from comsvcs.dll via rundll32 to perform a memory dump from lsass.
Sigma rule (View on GitHub)
1title: Lsass Memory Dump via Comsvcs DLL
2id: a49fa4d5-11db-418c-8473-1e014a8dd462
3status: test
4description: Detects adversaries leveraging the MiniDump export function from comsvcs.dll via rundll32 to perform a memory dump from lsass.
5references:
6 - https://twitter.com/shantanukhande/status/1229348874298388484
7 - https://modexp.wordpress.com/2019/08/30/minidumpwritedump-via-com-services-dll/
8author: Roberto Rodriguez (Cyb3rWard0g), OTR (Open Threat Research)
9date: 2020-10-20
10modified: 2023-11-29
11tags:
12 - attack.credential-access
13 - attack.t1003.001
14logsource:
15 category: process_access
16 product: windows
17detection:
18 selection:
19 TargetImage|endswith: '\lsass.exe'
20 SourceImage|endswith: '\rundll32.exe'
21 CallTrace|contains: 'comsvcs.dll'
22 condition: selection
23falsepositives:
24 - Unknown
25level: high
References
Related rules
- Credential Dumping Activity By Python Based Tool
- Credential Dumping Attempt Via WerFault
- Credential Dumping Tools Service Execution - Security
- Credential Dumping Tools Service Execution - System
- Dumping Process via Sqldumper.exe