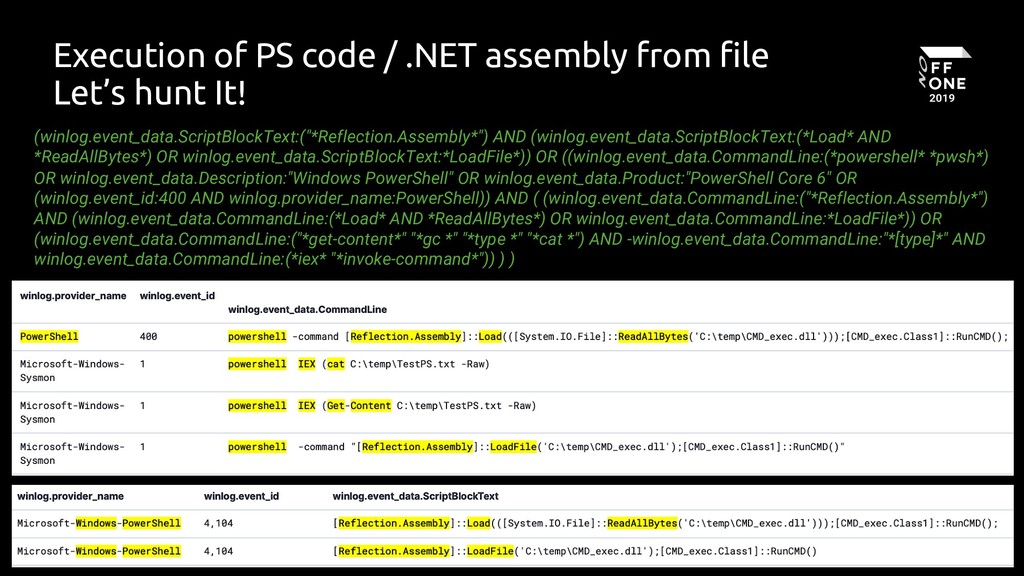
Potential In-Memory Execution Using Reflection.Assembly
Detects usage of "Reflection.Assembly" load functions to dynamically load assemblies in memory
Sigma rule (View on GitHub)
1title: Potential In-Memory Execution Using Reflection.Assembly
2id: ddcd88cb-7f62-4ce5-86f9-1704190feb0a
3status: test
4description: Detects usage of "Reflection.Assembly" load functions to dynamically load assemblies in memory
5references:
6 - https://speakerdeck.com/heirhabarov/hunting-for-powershell-abuse?slide=50
7author: frack113
8date: 2022-12-25
9tags:
10 - attack.defense-evasion
11 - attack.t1620
12logsource:
13 product: windows
14 category: ps_script
15 definition: Script Block Logging must be enable
16detection:
17 selection:
18 ScriptBlockText|contains: '[Reflection.Assembly]::load'
19 condition: selection
20falsepositives:
21 - Legitimate use of the library
22level: medium
References
Related rules
- AD Object WriteDAC Access
- AMSI Bypass Pattern Assembly GetType
- APT PRIVATELOG Image Load Pattern
- APT29 2018 Phishing Campaign CommandLine Indicators
- APT29 2018 Phishing Campaign File Indicators