Load Of RstrtMgr.DLL By An Uncommon Process
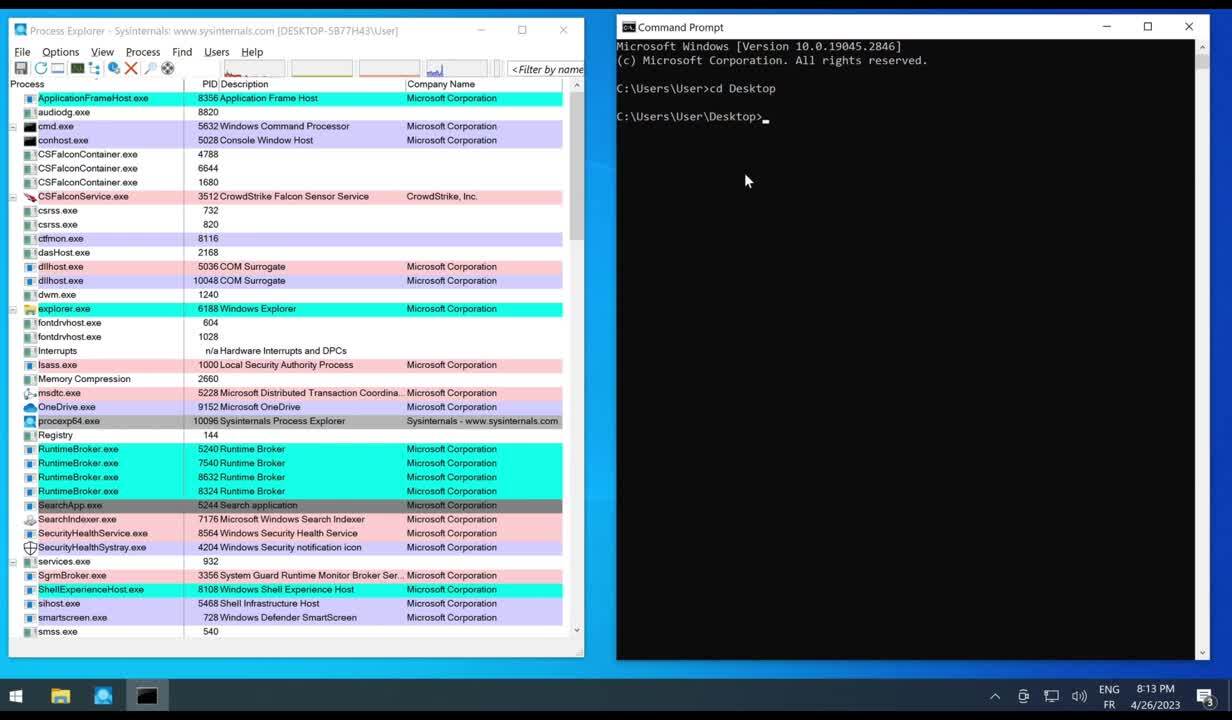
Detects the load of RstrtMgr DLL (Restart Manager) by an uncommon process. This library has been used during ransomware campaigns to kill processes that would prevent file encryption by locking them (e.g. Conti ransomware, Cactus ransomware). It has also recently been seen used by the BiBi wiper for Windows. It could also be used for anti-analysis purposes by shut downing specific processes.
Sigma rule (View on GitHub)
1title: Load Of RstrtMgr.DLL By An Uncommon Process
2id: 3669afd2-9891-4534-a626-e5cf03810a61
3related:
4 - id: b48492dc-c5ef-4572-8dff-32bc241c15c8
5 type: derived
6status: test
7description: |
8 Detects the load of RstrtMgr DLL (Restart Manager) by an uncommon process.
9 This library has been used during ransomware campaigns to kill processes that would prevent file encryption by locking them (e.g. Conti ransomware, Cactus ransomware). It has also recently been seen used by the BiBi wiper for Windows.
10 It could also be used for anti-analysis purposes by shut downing specific processes.
11references:
12 - https://www.crowdstrike.com/blog/windows-restart-manager-part-1/
13 - https://www.crowdstrike.com/blog/windows-restart-manager-part-2/
14 - https://web.archive.org/web/20231221193106/https://www.swascan.com/cactus-ransomware-malware-analysis/
15 - https://taiwan.postsen.com/business/88601/Hamas-hackers-use-data-destruction-software-BiBi-which-consumes-a-lot-of-processor-resources-to-wipe-Windows-computer-data--iThome.html
16author: Luc Génaux
17date: 2023-11-28
18modified: 2025-12-08
19tags:
20 - attack.impact
21 - attack.defense-evasion
22 - attack.t1486
23 - attack.t1562.001
24logsource:
25 category: image_load
26 product: windows
27detection:
28 selection:
29 - ImageLoaded|endswith: '\RstrtMgr.dll'
30 - OriginalFileName: 'RstrtMgr.dll'
31 filter_main_generic:
32 Image|startswith:
33 - C:\$WINDOWS.~BT\'
34 - C:\$WinREAgent\'
35 - C:\Program Files (x86)\'
36 - C:\Program Files\'
37 - C:\ProgramData\'
38 - C:\Windows\explorer.exe'
39 - C:\Windows\SoftwareDistribution\'
40 - C:\Windows\SysNative\'
41 - C:\Windows\System32\'
42 - C:\Windows\SysWOW64\'
43 - C:\Windows\WinSxS\'
44 - C:\WUDownloadCache\'
45 filter_main_user_software_installations:
46 Image|startswith: C:\Users\'
47 Image|contains|all:
48 - '\AppData\Local\Temp\is-'
49 - '.tmp\'
50 Image|endswith: '.tmp'
51 filter_main_admin_software_installations:
52 Image|startswith: C:\Windows\Temp\'
53 filter_optional_onedrive:
54 Image|startswith: 'C:\Users\'
55 Image|endswith: '\AppData\Local\Microsoft\OneDrive\OneDriveStandaloneUpdater.exe'
56 condition: selection and not 1 of filter_main_* and not 1 of filter_optional_*
57falsepositives:
58 - Other legitimate Windows processes not currently listed
59 - Processes related to software installation
60level: low
References
Related rules
- Load Of RstrtMgr.DLL By A Suspicious Process
- WannaCry Ransomware Activity
- Suspicious Windows Service Tampering
- IISReset Used to Stop IIS Services
- ASLR Disabled Via Sysctl or Direct Syscall - Linux