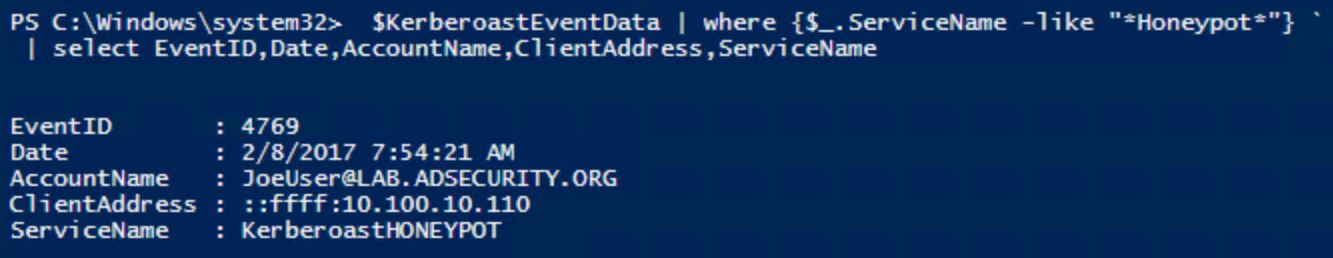
Kerberoasting Activity - Initial Query
This rule will collect the data needed to start looking into possible kerberoasting activity. Further analysis or computation within the query is needed focusing on requests from one specific host/IP towards multiple service names within a time period of 5 seconds. You can then set a threshold for the number of requests and time between the requests to turn this into an alert.
Sigma rule (View on GitHub)
1title: Kerberoasting Activity - Initial Query
2id: d04ae2b8-ad54-4de0-bd87-4bc1da66aa59
3status: test
4description: |
5 This rule will collect the data needed to start looking into possible kerberoasting activity.
6 Further analysis or computation within the query is needed focusing on requests from one specific host/IP towards multiple service names within a time period of 5 seconds.
7 You can then set a threshold for the number of requests and time between the requests to turn this into an alert.
8references:
9 - https://www.trustedsec.com/blog/art_of_kerberoast/
10 - https://adsecurity.org/?p=3513
11author: '@kostastsale'
12date: 2022-01-21
13modified: 2025-10-19
14tags:
15 - attack.credential-access
16 - attack.t1558.003
17logsource:
18 product: windows
19 service: security
20detection:
21 selection:
22 EventID: 4769
23 Status: '0x0' # Translated as status from failure code field. Query only for successes
24 TicketEncryptionType: '0x17' # RC4 ticket encryption type
25 filter_main_krbtgt:
26 ServiceName|endswith:
27 - 'krbtgt' # Ignore requests for the krbtgt service
28 - '$' # Ignore requests from service names that end with $ which are associated with genuine kerberos traffic
29 filter_main_machine_accounts:
30 TargetUserName|contains: '$@' # Ignore requests from machines
31 condition: selection and not 1 of filter_main_*
32falsepositives:
33 - Legacy applications.
34level: medium
References
Related rules
- HackTool - KrbRelayUp Execution
- HackTool - Rubeus Execution
- HackTool - Rubeus Execution - ScriptBlock
- User Couldn't Call a Privileged Service 'LsaRegisterLogonProcess'
- No Suitable Encryption Key Found For Generating Kerberos Ticket