Wget Creating Files in Tmp Directory
Detects the use of wget to download content in a temporary directory such as "/tmp" or "/var/tmp"
Sigma rule (View on GitHub)
1title: Wget Creating Files in Tmp Directory
2id: 35a05c60-9012-49b6-a11f-6bab741c9f74
3status: test
4description: Detects the use of wget to download content in a temporary directory such as "/tmp" or "/var/tmp"
5references:
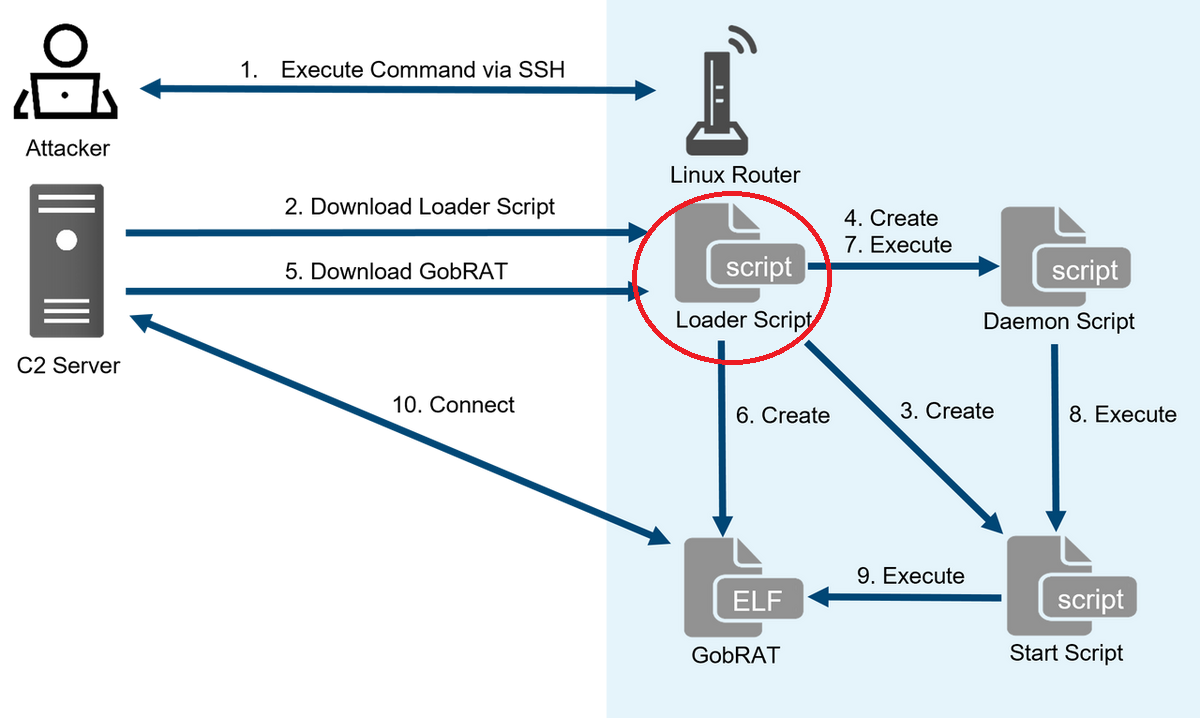
6 - https://blogs.jpcert.or.jp/en/2023/05/gobrat.html
7 - https://jstnk9.github.io/jstnk9/research/GobRAT-Malware/
8 - https://www.virustotal.com/gui/file/60bcd645450e4c846238cf0e7226dc40c84c96eba99f6b2cffcd0ab4a391c8b3/detection
9 - https://www.virustotal.com/gui/file/3e44c807a25a56f4068b5b8186eee5002eed6f26d665a8b791c472ad154585d1/detection
10author: Joseliyo Sanchez, @Joseliyo_Jstnk
11date: 2023-06-02
12tags:
13 - attack.command-and-control
14 - attack.t1105
15logsource:
16 product: linux
17 category: file_event
18detection:
19 selection:
20 Image|endswith: '/wget'
21 TargetFilename|startswith:
22 - '/tmp/'
23 - '/var/tmp/'
24 condition: selection
25falsepositives:
26 - Legitimate downloads of files in the tmp folder.
27level: medium
References
Related rules
- AppX Package Installation Attempts Via AppInstaller.EXE
- Arbitrary File Download Via GfxDownloadWrapper.EXE
- Curl Usage on Linux
- Download File To Potentially Suspicious Directory Via Wget
- Executable from Webdav