Suspicious Activity in Shell Commands
Detects suspicious shell commands used in various exploit codes (see references)
Sigma rule (View on GitHub)
1title: Suspicious Activity in Shell Commands
2id: 2aa1440c-9ae9-4d92-84a7-a9e5f5e31695
3status: test
4description: Detects suspicious shell commands used in various exploit codes (see references)
5references:
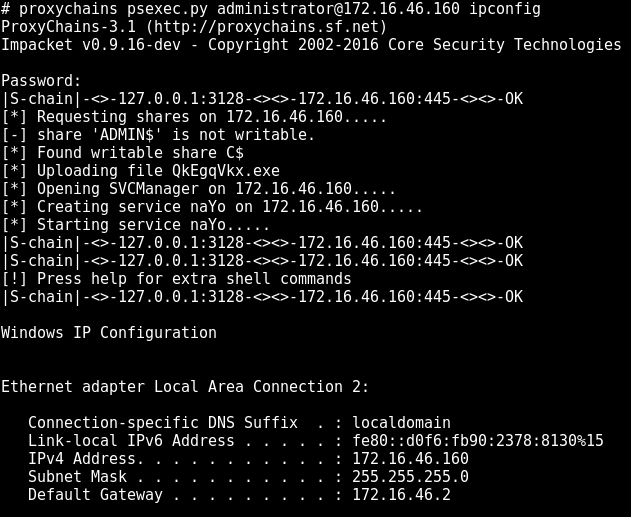
6 - https://web.archive.org/web/20170319121015/http://www.threatgeek.com/2017/03/widespread-exploitation-attempts-using-cve-2017-5638.html
7 - https://github.com/rapid7/metasploit-framework/blob/eb6535009f5fdafa954525687f09294918b5398d/modules/exploits/multi/http/struts_code_exec_exception_delegator.rb
8 - http://pastebin.com/FtygZ1cg
9 - https://artkond.com/2017/03/23/pivoting-guide/
10author: Florian Roth (Nextron Systems)
11date: 2017-08-21
12modified: 2021-11-27
13tags:
14 - attack.execution
15 - attack.t1059.004
16logsource:
17 product: linux
18detection:
19 keywords:
20 # Generic suspicious commands
21 - 'wget * - http* | perl'
22 - 'wget * - http* | sh'
23 - 'wget * - http* | bash'
24 - 'python -m SimpleHTTPServer'
25 - '-m http.server' # Python 3
26 - 'import pty; pty.spawn*'
27 - 'socat exec:*'
28 - 'socat -O /tmp/*'
29 - 'socat tcp-connect*'
30 - '*echo binary >>*'
31 # Malware
32 - '*wget *; chmod +x*'
33 - '*wget *; chmod 777 *'
34 - '*cd /tmp || cd /var/run || cd /mnt*'
35 # Apache Struts in-the-wild exploit codes
36 - '*stop;service iptables stop;*'
37 - '*stop;SuSEfirewall2 stop;*'
38 - 'chmod 777 2020*'
39 - '*>>/etc/rc.local'
40 # Metasploit framework exploit codes
41 - '*base64 -d /tmp/*'
42 - '* | base64 -d *'
43 - '*/chmod u+s *'
44 - '*chmod +s /tmp/*'
45 - '*chmod u+s /tmp/*'
46 - '* /tmp/haxhax*'
47 - '* /tmp/ns_sploit*'
48 - 'nc -l -p *'
49 - 'cp /bin/ksh *'
50 - 'cp /bin/sh *'
51 - '* /tmp/*.b64 *'
52 - '*/tmp/ysocereal.jar*'
53 - '*/tmp/x *'
54 - '*; chmod +x /tmp/*'
55 - '*;chmod +x /tmp/*'
56 condition: keywords
57falsepositives:
58 - Unknown
59level: high
References
Related rules
- AWS EC2 Startup Shell Script Change
- BPFtrace Unsafe Option Usage
- Equation Group Indicators
- Interactive Bash Suspicious Children
- Linux Reverse Shell Indicator