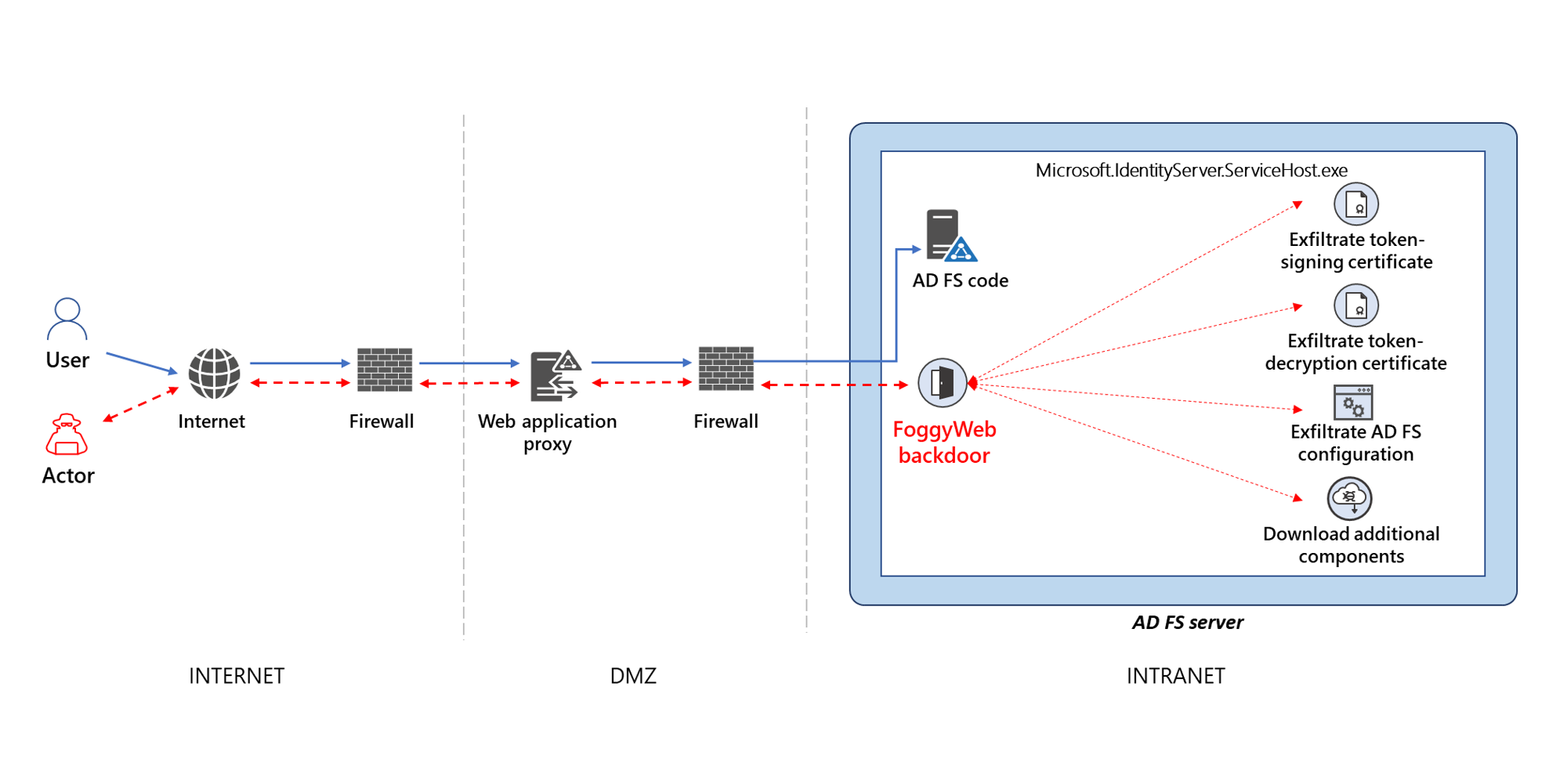
FoggyWeb Backdoor DLL Loading
Detects DLL hijacking technique used by NOBELIUM in their FoggyWeb backdoor. Which loads a malicious version of the expected "version.dll" dll
Sigma rule (View on GitHub)
1title: FoggyWeb Backdoor DLL Loading
2id: 640dc51c-7713-4faa-8a0e-e7c0d9d4654c
3status: test
4description: Detects DLL hijacking technique used by NOBELIUM in their FoggyWeb backdoor. Which loads a malicious version of the expected "version.dll" dll
5references:
6 - https://www.microsoft.com/security/blog/2021/09/27/foggyweb-targeted-nobelium-malware-leads-to-persistent-backdoor/
7author: Florian Roth (Nextron Systems)
8date: 2021-09-27
9modified: 2022-12-09
10tags:
11 - attack.resource-development
12 - attack.t1587
13 - detection.emerging-threats
14logsource:
15 category: image_load
16 product: windows
17detection:
18 selection:
19 ImageLoaded: 'C:\Windows\ADFS\version.dll'
20 condition: selection
21falsepositives:
22 - Unlikely
23level: critical
References
Related rules
- Suspicious Word Cab File Write CVE-2021-40444
- HackTool - PurpleSharp Execution
- Mustang Panda Dropper
- ADSelfService Exploitation
- APT PRIVATELOG Image Load Pattern