Mustang Panda Dropper
Detects specific process parameters as used by Mustang Panda droppers
Sigma rule (View on GitHub)
1title: Mustang Panda Dropper
2id: 2d87d610-d760-45ee-a7e6-7a6f2a65de00
3status: test
4description: Detects specific process parameters as used by Mustang Panda droppers
5references:
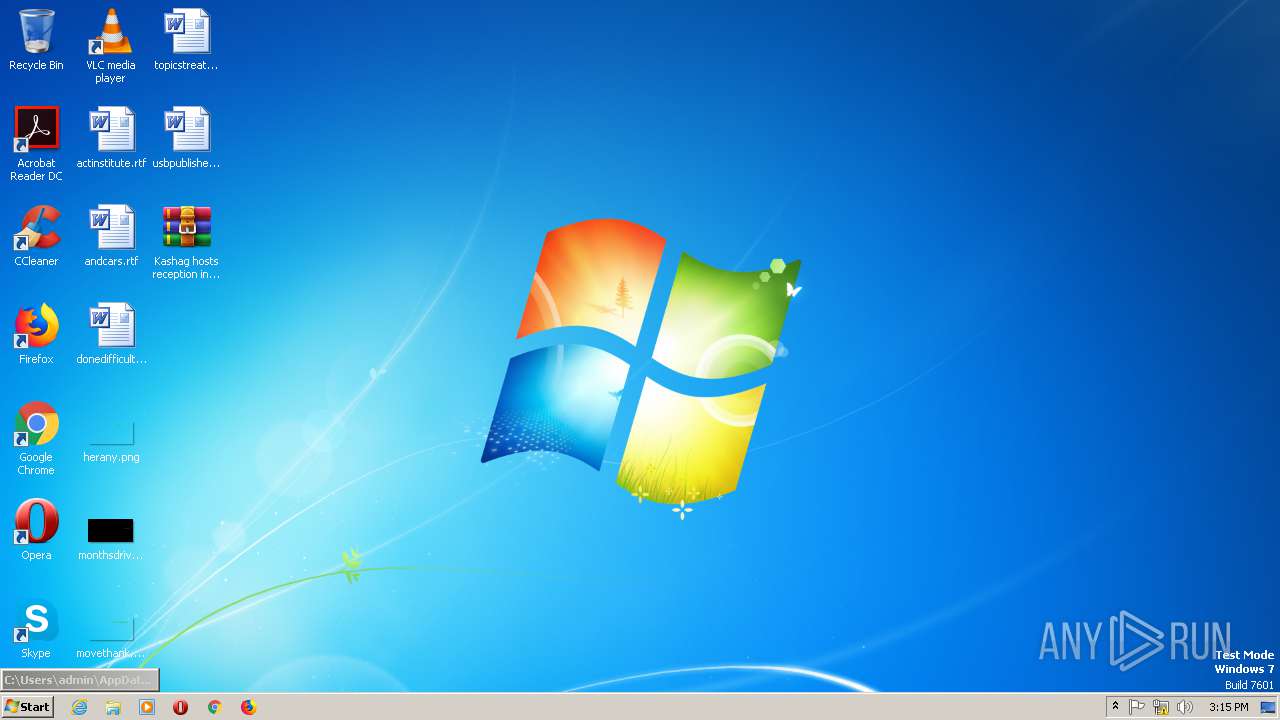
6 - https://app.any.run/tasks/7ca5661d-a67b-43ec-98c1-dd7a8103c256/
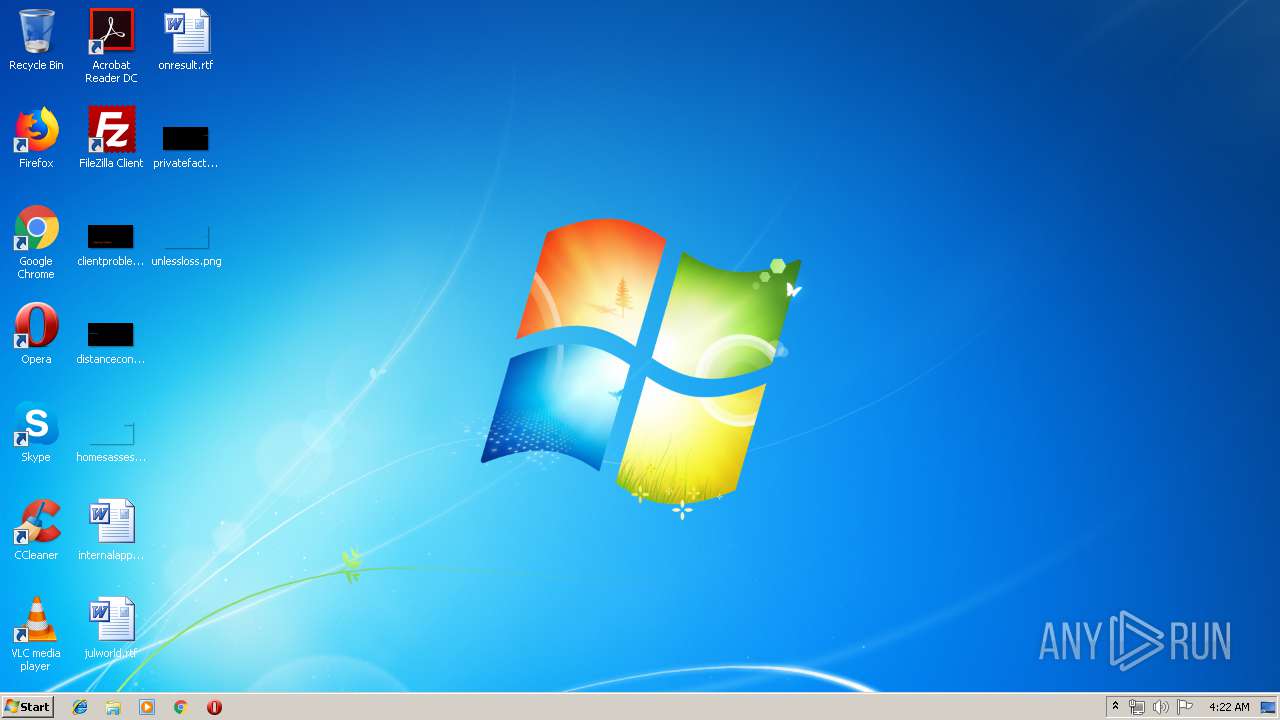
7 - https://app.any.run/tasks/b12cccf3-1c22-4e28-9d3e-c7a6062f3914/
8 - https://www.anomali.com/blog/china-based-apt-mustang-panda-targets-minority-groups-public-and-private-sector-organizations
9author: Florian Roth (Nextron Systems), oscd.community
10date: 2019-10-30
11modified: 2021-11-27
12tags:
13 - attack.t1587.001
14 - attack.resource-development
15 - detection.emerging-threats
16logsource:
17 category: process_creation
18 product: windows
19detection:
20 selection_cli:
21 - CommandLine|contains:
22 - 'Temp\wtask.exe /create'
23 - '%windir:~-3,1%%PUBLIC:~-9,1%'
24 - '/tn "Security Script '
25 - '%windir:~-1,1%'
26 - CommandLine|contains|all:
27 - '/E:vbscript'
28 - 'C:\Users\'
29 - '.txt'
30 - '/F'
31 selection_img:
32 Image|endswith: 'Temp\winwsh.exe'
33 condition: 1 of selection_*
34falsepositives:
35 - Unlikely
36level: high
References
Related rules
- FoggyWeb Backdoor DLL Loading
- PUA - CsExec Execution
- ProxyLogon MSExchange OabVirtualDirectory
- Suspicious Word Cab File Write CVE-2021-40444
- VHD Image Download Via Browser