APT27 - Emissary Panda Activity
Detects the execution of DLL side-loading malware used by threat group Emissary Panda aka APT27
Sigma rule (View on GitHub)
1title: APT27 - Emissary Panda Activity
2id: 9aa01d62-7667-4d3b-acb8-8cb5103e2014
3status: test
4description: Detects the execution of DLL side-loading malware used by threat group Emissary Panda aka APT27
5references:
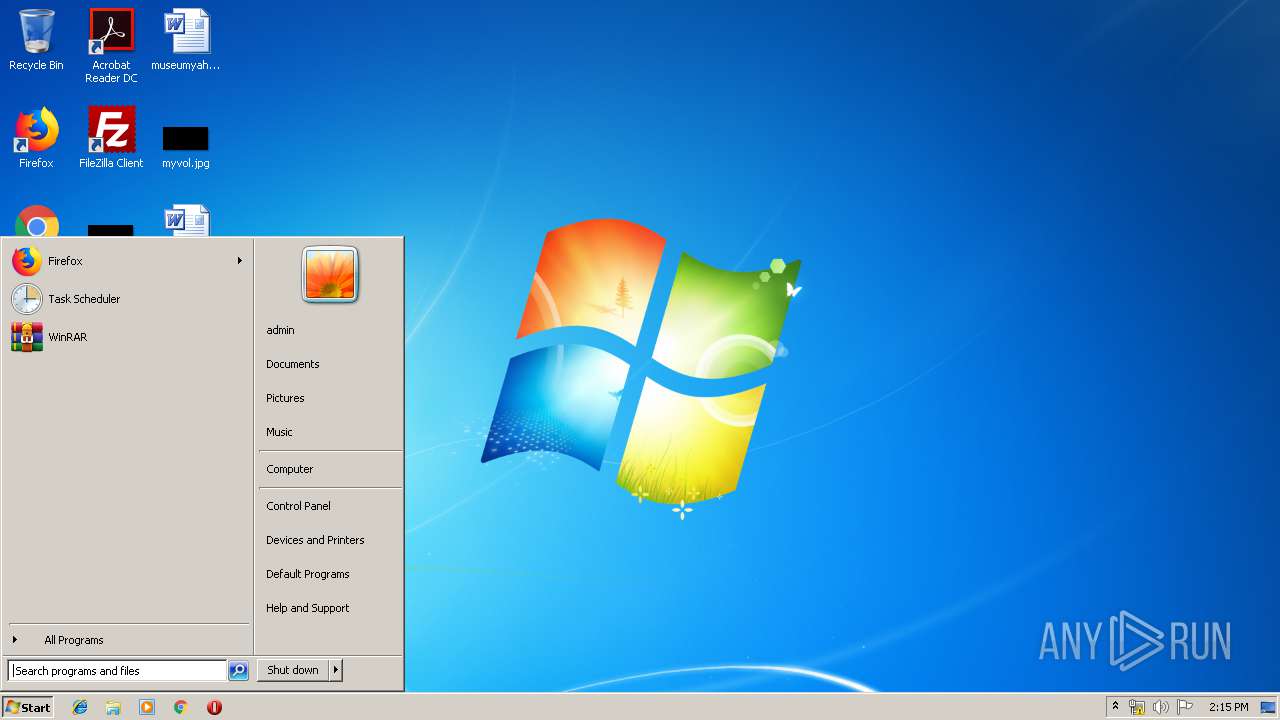
6 - https://app.any.run/tasks/579e7587-f09d-4aae-8b07-472833262965
7 - https://twitter.com/cyb3rops/status/1168863899531132929
8 - https://research.nccgroup.com/2018/05/18/emissary-panda-a-potential-new-malicious-tool/
9author: Florian Roth (Nextron Systems)
10date: 2018-09-03
11modified: 2023-03-09
12tags:
13 - attack.privilege-escalation
14 - attack.persistence
15 - attack.defense-evasion
16 - attack.t1574.001
17 - attack.g0027
18 - detection.emerging-threats
19logsource:
20 category: process_creation
21 product: windows
22detection:
23 selection_sllauncher:
24 ParentImage|endswith: '\sllauncher.exe'
25 Image|endswith: '\svchost.exe'
26 selection_svchost:
27 ParentImage|contains: '\AppData\Roaming\'
28 Image|endswith: '\svchost.exe'
29 CommandLine|contains: '-k'
30 condition: 1 of selection_*
31falsepositives:
32 - Unlikely
33level: critical
References
Related rules
- DLL Names Used By SVR For GraphicalProton Backdoor
- Diamond Sleet APT DLL Sideloading Indicators
- Lazarus APT DLL Sideloading Activity
- Pingback Backdoor Activity
- Pingback Backdoor DLL Loading Activity