Azure Kubernetes Service Account Modified or Deleted
Identifies when a service account is modified or deleted.
Sigma rule (View on GitHub)
1title: Azure Kubernetes Service Account Modified or Deleted
2id: 12d027c3-b48c-4d9d-8bb6-a732200034b2
3status: test
4description: Identifies when a service account is modified or deleted.
5references:
6 - https://learn.microsoft.com/en-us/azure/role-based-access-control/resource-provider-operations#microsoftkubernetes
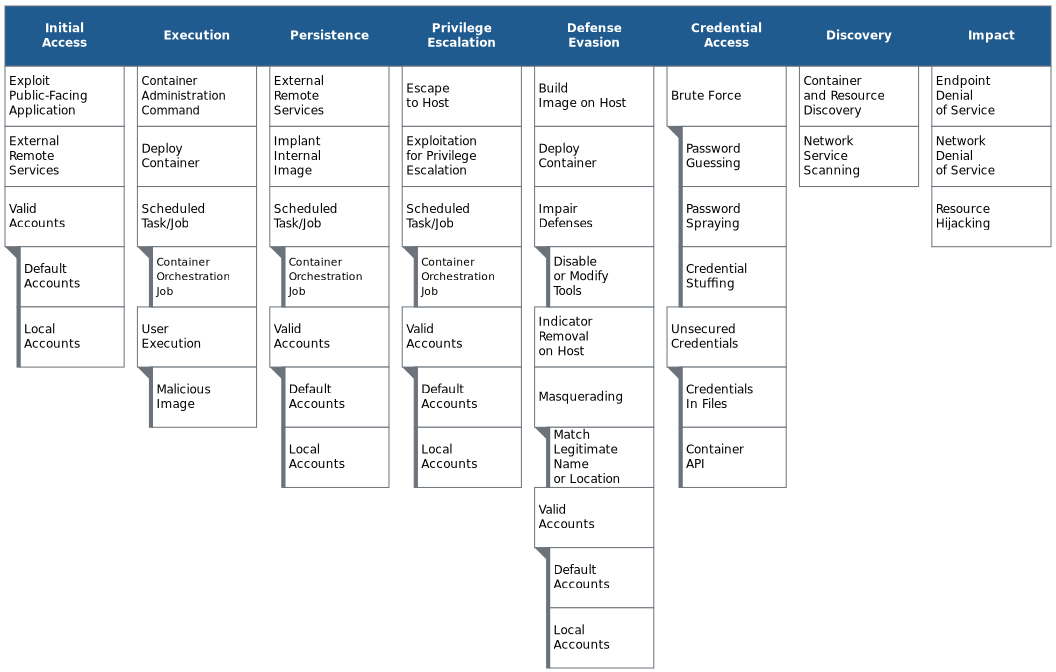
7 - https://www.microsoft.com/security/blog/2021/03/23/secure-containerized-environments-with-updated-threat-matrix-for-kubernetes/
8 - https://www.microsoft.com/security/blog/2020/04/02/attack-matrix-kubernetes/
9 - https://medium.com/mitre-engenuity/att-ck-for-containers-now-available-4c2359654bf1
10author: Austin Songer @austinsonger
11date: 2021-08-07
12modified: 2022-08-23
13tags:
14 - attack.impact
15 - attack.t1531
16 - attack.t1485
17 - attack.t1496
18 - attack.t1489
19logsource:
20 product: azure
21 service: activitylogs
22detection:
23 selection:
24 operationName:
25 - MICROSOFT.KUBERNETES/CONNECTEDCLUSTERS/SERVICEACCOUNTS/WRITE
26 - MICROSOFT.KUBERNETES/CONNECTEDCLUSTERS/SERVICEACCOUNTS/DELETE
27 - MICROSOFT.KUBERNETES/CONNECTEDCLUSTERS/SERVICEACCOUNTS/IMPERSONATE/ACTION
28 condition: selection
29falsepositives:
30 - Service account being modified or deleted may be performed by a system administrator. Verify whether the user identity, user agent, and/or hostname should be making changes in your environment.
31 - Service account modified or deleted from unfamiliar users should be investigated. If known behavior is causing false positives, it can be exempted from the rule.
32level: medium
References
Related rules
- Azure Container Registry Created or Deleted
- Azure Kubernetes Cluster Created or Deleted
- Azure Kubernetes Network Policy Change
- Azure Kubernetes RoleBinding/ClusterRoleBinding Modified and Deleted
- Azure Kubernetes Secret or Config Object Access