Suspicious Process Execution in PerfLogs Directory
Detects process execution in PerfLogs folder - a folder used by Windows for log collection - and matching previously-observed naming patterns for ransomware executables.
Sigma rule (View on GitHub)
1title: Suspicious Process Execution in PerfLogs Directory
2id: 82469ee5-ccf3-4669-9be6-31830f7ef3d7
3status: experimental
4description: Detects process execution in PerfLogs folder - a folder used by Windows for log collection - and matching previously-observed naming patterns for ransomware executables.
5references:
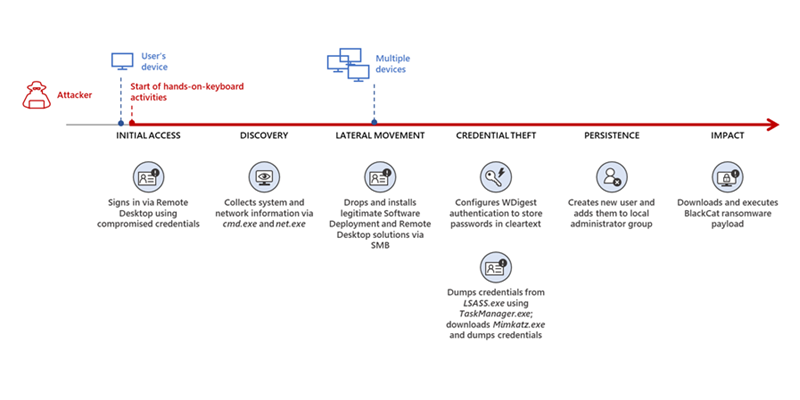
6 - https://www.microsoft.com/en-us/security/blog/2022/06/13/the-many-lives-of-blackcat-ransomware/
7author: Micah Babinski
8date: 2022/12/04
9tags:
10 - attack.defense_evasion
11 - attack.t1564
12logsource:
13 category: process_creation
14 product: windows
15detection:
16 selection1:
17 ParentImage|contains: 'perflogs'
18 selection2:
19 ParentImage|re: '^.*\\[a-z]{3}\.exe'
20 condition: all of selection*
21falsepositives:
22 - Unknown
23level: high```
References
Related rules
- Suspicious Registry Modification of MaxMpxCt Parameters
- Tampering of Windows Defender with Reg
- PowerShell -encodedcommand Switch
- Event Log Manipulation Using Wevtutil
- Malicious QakBot Dropped File Creation (Sysmon)