Suspicious Command Line Indicating BlackCat Execution with Get UUID Option
Detects process execution with the --access-token flag accompanied by a child process with a 'get uuid' option.
Sigma rule (View on GitHub)
1title: Suspicious Command Line Indicating BlackCat Execution with Get UUID Option
2id: 76fe5991-2bff-4ae2-adcf-28a95788027f
3status: experimental
4description: Detects process execution with the --access-token flag accompanied by a child process with a 'get uuid' option.
5references:
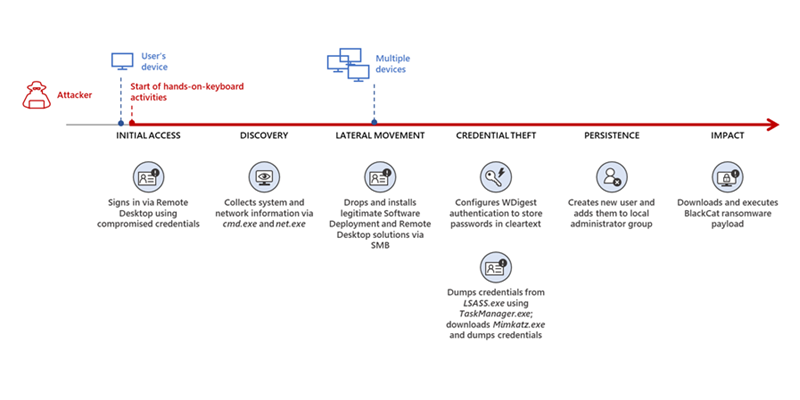
6 - https://www.microsoft.com/en-us/security/blog/2022/06/13/the-many-lives-of-blackcat-ransomware/
7author: Micah Babinski
8date: 2022/12/04
9tags:
10 - attack.execution
11 - attack.t1059
12 - attack.t1204
13logsource:
14 category: process_creation
15 product: windows
16detection:
17 selection:
18 ParentCommandLine|contains: '--access-token'
19 CommandLine|contains: 'get uuid'
20 condition: selection
21falsepositives:
22 - Unknown
23level: high```
References
Related rules
- Suspicious Command Line Indicating BlackCat Execution
- Suspicious Powershell Cmdlets
- Suspicious WMI-Related Powershell Cmdlets
- Wscript.exe Executing Agreement Javascript in AppData Folder
- PowerShell -encodedcommand Switch