Lateral Movement via Startup Folder
Identifies suspicious file creations in the startup folder of a remote system. An adversary could abuse this to move laterally by dropping a malicious script or executable that will be executed after a reboot or user logon.
Elastic rule (View on GitHub)
1[metadata]
2creation_date = "2020/10/19"
3integration = ["endpoint", "windows", "m365_defender", "sentinel_one_cloud_funnel"]
4maturity = "production"
5updated_date = "2025/03/20"
6
7[rule]
8author = ["Elastic"]
9description = """
10Identifies suspicious file creations in the startup folder of a remote system. An adversary could abuse this to move
11laterally by dropping a malicious script or executable that will be executed after a reboot or user logon.
12"""
13from = "now-9m"
14index = [
15 "logs-endpoint.events.file-*",
16 "winlogbeat-*",
17 "logs-windows.sysmon_operational-*",
18 "endgame-*",
19 "logs-m365_defender.event-*",
20 "logs-sentinel_one_cloud_funnel.*",
21]
22language = "eql"
23license = "Elastic License v2"
24name = "Lateral Movement via Startup Folder"
25note = """## Triage and analysis
26
27> **Disclaimer**:
28> This investigation guide was created using generative AI technology and has been reviewed to improve its accuracy and relevance. While every effort has been made to ensure its quality, we recommend validating the content and adapting it to suit your specific environment and operational needs.
29
30### Investigating Lateral Movement via Startup Folder
31
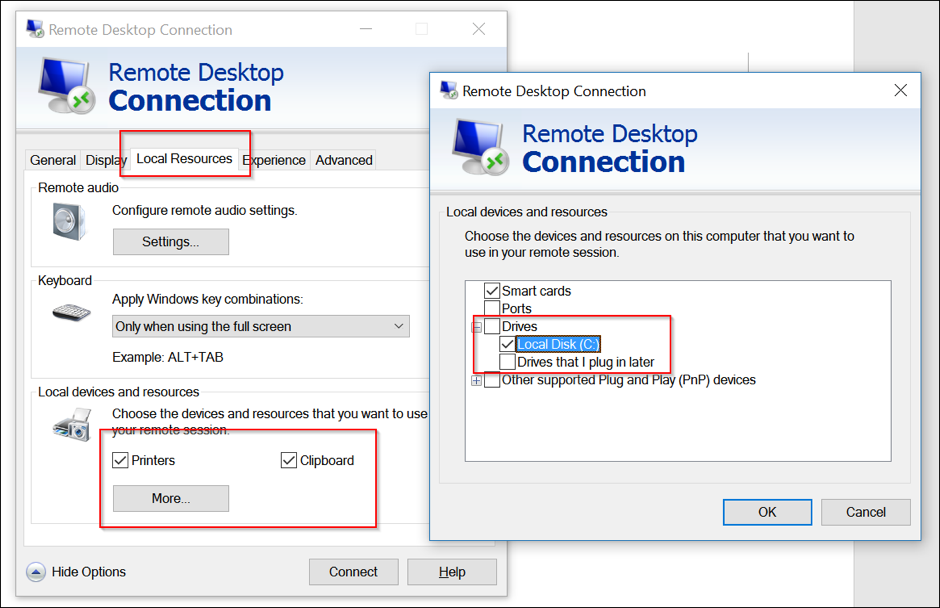
32The Windows Startup folder is a mechanism that allows programs to run automatically upon user logon or system reboot. Adversaries exploit this by placing malicious files in the Startup folder of remote systems, often accessed via RDP or SMB, to ensure persistence and facilitate lateral movement. The detection rule identifies suspicious file activities in these folders, focusing on processes like mstsc.exe, which may indicate unauthorized access and file creation, signaling potential lateral movement attempts.
33
34### Possible investigation steps
35
36- Review the alert details to confirm the file creation or change event in the specified Startup folder paths, focusing on the file path patterns: "?:\\\\Users\\\\*\\\\AppData\\\\Roaming\\\\Microsoft\\\\Windows\\\\Start Menu\\\\Programs\\\\Startup\\\\*" and "?:\\\\ProgramData\\\\Microsoft\\\\Windows\\\\Start Menu\\\\Programs\\\\Startup\\\\*".
37- Check the process information associated with the event, particularly if the process name is "mstsc.exe" or if the process ID is 4, to determine if the activity is linked to remote access via RDP or SMB.
38- Investigate the origin of the remote connection by examining network logs or RDP session logs to identify the source IP address and user account involved in the connection.
39- Analyze the newly created or modified file in the Startup folder for malicious characteristics, such as unusual file names, unexpected file types, or known malware signatures, using antivirus or sandbox analysis tools.
40- Review user account activity and permissions to determine if the account associated with the process has been compromised or is being misused for unauthorized access.
41- Correlate this event with other security alerts or logs from data sources like Sysmon, Microsoft Defender for Endpoint, or SentinelOne to identify any related suspicious activities or patterns indicating lateral movement attempts.
42
43### False positive analysis
44
45- Legitimate software installations or updates may create files in the Startup folder, triggering the rule. Users can manage this by maintaining a list of known software that typically modifies the Startup folder and creating exceptions for these processes.
46- System administrators using remote desktop tools like mstsc.exe for legitimate purposes might inadvertently trigger the rule. To handle this, users can exclude specific administrator accounts or known IP addresses from the detection rule.
47- Automated scripts or system management tools that deploy updates or configurations across multiple systems might cause false positives. Users should identify these tools and add them to an exclusion list to prevent unnecessary alerts.
48- Some enterprise applications may use the Startup folder for legitimate operations, especially during system boot or user logon. Users should document these applications and configure the rule to ignore file changes associated with them.
49
50### Response and remediation
51
52- Immediately isolate the affected system from the network to prevent further lateral movement and potential spread of the threat.
53- Terminate any suspicious processes, particularly those related to mstsc.exe or any unauthorized processes with PID 4, to halt any ongoing malicious activities.
54- Remove any unauthorized files or scripts found in the Startup folder paths specified in the detection query to prevent them from executing on reboot or user logon.
55- Conduct a thorough scan of the affected system using updated antivirus or endpoint detection and response (EDR) tools to identify and remove any additional malicious files or remnants.
56- Review and reset credentials for any accounts that were accessed or potentially compromised during the incident to prevent unauthorized access.
57- Escalate the incident to the security operations center (SOC) or incident response team for further investigation and to determine if additional systems are affected.
58- Implement enhanced monitoring and logging for RDP and SMB activities, focusing on unusual file creation events in Startup folders, to improve detection of similar threats in the future."""
59references = [
60 "https://www.mdsec.co.uk/2017/06/rdpinception/",
61 "https://www.elastic.co/security-labs/hunting-for-lateral-movement-using-event-query-language",
62]
63risk_score = 73
64rule_id = "25224a80-5a4a-4b8a-991e-6ab390465c4f"
65severity = "high"
66tags = [
67 "Domain: Endpoint",
68 "OS: Windows",
69 "Use Case: Threat Detection",
70 "Tactic: Lateral Movement",
71 "Data Source: Elastic Endgame",
72 "Data Source: Elastic Defend",
73 "Data Source: Sysmon",
74 "Data Source: Microsoft Defender for Endpoint",
75 "Data Source: SentinelOne",
76 "Resources: Investigation Guide",
77]
78timestamp_override = "event.ingested"
79type = "eql"
80
81query = '''
82file where host.os.type == "windows" and event.type in ("creation", "change") and
83
84 /* via RDP TSClient mounted share or SMB */
85 (process.name : "mstsc.exe" or process.pid == 4) and
86
87 file.path : ("?:\\Users\\*\\AppData\\Roaming\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\*",
88 "?:\\ProgramData\\Microsoft\\Windows\\Start Menu\\Programs\\Startup\\*")
89'''
90
91
92[[rule.threat]]
93framework = "MITRE ATT&CK"
94[[rule.threat.technique]]
95id = "T1021"
96name = "Remote Services"
97reference = "https://attack.mitre.org/techniques/T1021/"
98[[rule.threat.technique.subtechnique]]
99id = "T1021.001"
100name = "Remote Desktop Protocol"
101reference = "https://attack.mitre.org/techniques/T1021/001/"
102
103
104
105[rule.threat.tactic]
106id = "TA0008"
107name = "Lateral Movement"
108reference = "https://attack.mitre.org/tactics/TA0008/"
109[[rule.threat]]
110framework = "MITRE ATT&CK"
111[[rule.threat.technique]]
112id = "T1547"
113name = "Boot or Logon Autostart Execution"
114reference = "https://attack.mitre.org/techniques/T1547/"
115[[rule.threat.technique.subtechnique]]
116id = "T1547.001"
117name = "Registry Run Keys / Startup Folder"
118reference = "https://attack.mitre.org/techniques/T1547/001/"
119
120
121
122[rule.threat.tactic]
123id = "TA0003"
124name = "Persistence"
125reference = "https://attack.mitre.org/tactics/TA0003/"
Triage and analysis
Disclaimer: This investigation guide was created using generative AI technology and has been reviewed to improve its accuracy and relevance. While every effort has been made to ensure its quality, we recommend validating the content and adapting it to suit your specific environment and operational needs.
Investigating Lateral Movement via Startup Folder
The Windows Startup folder is a mechanism that allows programs to run automatically upon user logon or system reboot. Adversaries exploit this by placing malicious files in the Startup folder of remote systems, often accessed via RDP or SMB, to ensure persistence and facilitate lateral movement. The detection rule identifies suspicious file activities in these folders, focusing on processes like mstsc.exe, which may indicate unauthorized access and file creation, signaling potential lateral movement attempts.
Possible investigation steps
- Review the alert details to confirm the file creation or change event in the specified Startup folder paths, focusing on the file path patterns: "?:\Users\\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\" and "?:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup\*".
- Check the process information associated with the event, particularly if the process name is "mstsc.exe" or if the process ID is 4, to determine if the activity is linked to remote access via RDP or SMB.
- Investigate the origin of the remote connection by examining network logs or RDP session logs to identify the source IP address and user account involved in the connection.
- Analyze the newly created or modified file in the Startup folder for malicious characteristics, such as unusual file names, unexpected file types, or known malware signatures, using antivirus or sandbox analysis tools.
- Review user account activity and permissions to determine if the account associated with the process has been compromised or is being misused for unauthorized access.
- Correlate this event with other security alerts or logs from data sources like Sysmon, Microsoft Defender for Endpoint, or SentinelOne to identify any related suspicious activities or patterns indicating lateral movement attempts.
False positive analysis
- Legitimate software installations or updates may create files in the Startup folder, triggering the rule. Users can manage this by maintaining a list of known software that typically modifies the Startup folder and creating exceptions for these processes.
- System administrators using remote desktop tools like mstsc.exe for legitimate purposes might inadvertently trigger the rule. To handle this, users can exclude specific administrator accounts or known IP addresses from the detection rule.
- Automated scripts or system management tools that deploy updates or configurations across multiple systems might cause false positives. Users should identify these tools and add them to an exclusion list to prevent unnecessary alerts.
- Some enterprise applications may use the Startup folder for legitimate operations, especially during system boot or user logon. Users should document these applications and configure the rule to ignore file changes associated with them.
Response and remediation
- Immediately isolate the affected system from the network to prevent further lateral movement and potential spread of the threat.
- Terminate any suspicious processes, particularly those related to mstsc.exe or any unauthorized processes with PID 4, to halt any ongoing malicious activities.
- Remove any unauthorized files or scripts found in the Startup folder paths specified in the detection query to prevent them from executing on reboot or user logon.
- Conduct a thorough scan of the affected system using updated antivirus or endpoint detection and response (EDR) tools to identify and remove any additional malicious files or remnants.
- Review and reset credentials for any accounts that were accessed or potentially compromised during the incident to prevent unauthorized access.
- Escalate the incident to the security operations center (SOC) or incident response team for further investigation and to determine if additional systems are affected.
- Implement enhanced monitoring and logging for RDP and SMB activities, focusing on unusual file creation events in Startup folders, to improve detection of similar threats in the future.
References
Related rules
- Execution via TSClient Mountpoint
- Microsoft Exchange Server UM Writing Suspicious Files
- Mounting Hidden or WebDav Remote Shares
- Potential Remote Desktop Tunneling Detected
- Potential WSUS Abuse for Lateral Movement