Creation or Modification of Domain Backup DPAPI private key
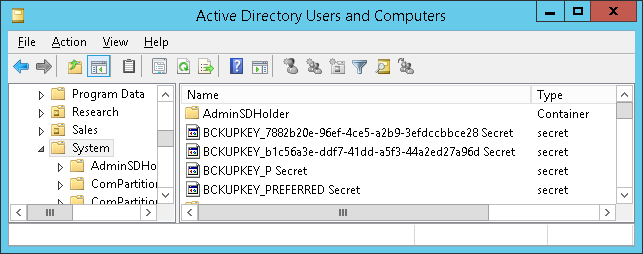
Identifies the creation or modification of Domain Backup private keys. Adversaries may extract the Data Protection API (DPAPI) domain backup key from a Domain Controller (DC) to be able to decrypt any domain user master key file.
Elastic rule (View on GitHub)
1[metadata]
2creation_date = "2020/08/13"
3integration = ["endpoint", "windows", "sentinel_one_cloud_funnel", "m365_defender", "crowdstrike"]
4maturity = "production"
5updated_date = "2025/03/20"
6
7[rule]
8author = ["Elastic"]
9description = """
10Identifies the creation or modification of Domain Backup private keys. Adversaries may extract the Data Protection API
11(DPAPI) domain backup key from a Domain Controller (DC) to be able to decrypt any domain user master key file.
12"""
13from = "now-9m"
14index = [
15 "winlogbeat-*",
16 "logs-endpoint.events.file-*",
17 "logs-windows.sysmon_operational-*",
18 "endgame-*",
19 "logs-sentinel_one_cloud_funnel.*",
20 "logs-m365_defender.event-*",
21 "logs-crowdstrike.fdr*",
22]
23language = "eql"
24license = "Elastic License v2"
25name = "Creation or Modification of Domain Backup DPAPI private key"
26note = """## Triage and analysis
27
28Domain DPAPI Backup keys are stored on domain controllers and can be dumped remotely with tools such as Mimikatz. The resulting .pvk private key can be used to decrypt ANY domain user masterkeys, which then can be used to decrypt any secrets protected by those keys.
29"""
30references = [
31 "https://www.dsinternals.com/en/retrieving-dpapi-backup-keys-from-active-directory/",
32 "https://posts.specterops.io/operational-guidance-for-offensive-user-dpapi-abuse-1fb7fac8b107",
33]
34risk_score = 73
35rule_id = "b83a7e96-2eb3-4edf-8346-427b6858d3bd"
36severity = "high"
37tags = [
38 "Domain: Endpoint",
39 "OS: Windows",
40 "Use Case: Threat Detection",
41 "Tactic: Credential Access",
42 "Data Source: Elastic Endgame",
43 "Data Source: Elastic Defend",
44 "Data Source: Sysmon",
45 "Data Source: SentinelOne",
46 "Data Source: Microsoft Defender for Endpoint",
47 "Data Source: Crowdstrike",
48 "Resources: Investigation Guide",
49]
50timestamp_override = "event.ingested"
51type = "eql"
52
53query = '''
54file where host.os.type == "windows" and event.type != "deletion" and file.name : ("ntds_capi_*.pfx", "ntds_capi_*.pvk")
55'''
56
57
58[[rule.threat]]
59framework = "MITRE ATT&CK"
60[[rule.threat.technique]]
61id = "T1552"
62name = "Unsecured Credentials"
63reference = "https://attack.mitre.org/techniques/T1552/"
64[[rule.threat.technique.subtechnique]]
65id = "T1552.004"
66name = "Private Keys"
67reference = "https://attack.mitre.org/techniques/T1552/004/"
68
69
70[[rule.threat.technique]]
71id = "T1555"
72name = "Credentials from Password Stores"
73reference = "https://attack.mitre.org/techniques/T1555/"
74
75
76[rule.threat.tactic]
77id = "TA0006"
78name = "Credential Access"
79reference = "https://attack.mitre.org/tactics/TA0006/"
Triage and analysis
Domain DPAPI Backup keys are stored on domain controllers and can be dumped remotely with tools such as Mimikatz. The resulting .pvk private key can be used to decrypt ANY domain user masterkeys, which then can be used to decrypt any secrets protected by those keys.
References
Related rules
- Credential Acquisition via Registry Hive Dumping
- Kirbi File Creation
- Microsoft IIS Connection Strings Decryption
- NTDS Dump via Wbadmin
- NTDS or SAM Database File Copied