Execution via GitHub Actions Runner
This rule detects potentially dangerous commands spawned by the GitHub Actions Runner.Worker process on self-hosted runner machines. Adversaries who gain the ability to modify or trigger workflows in a linked GitHub repository can execute arbitrary commands on the runner host. This behavior may indicate malicious or unexpected workflow activity, including code execution, file manipulation, or network exfiltration initiated through a compromised repository or unauthorized workflow.
Elastic rule (View on GitHub)
1[metadata]
2creation_date = "2025/11/26"
3integration = ["endpoint", "windows", "system", "m365_defender", "sentinel_one_cloud_funnel", "crowdstrike", "auditd_manager"]
4maturity = "production"
5updated_date = "2026/03/24"
6
7[rule]
8author = ["Elastic"]
9description = """
10This rule detects potentially dangerous commands spawned by the GitHub Actions Runner.Worker process on self-hosted runner
11machines. Adversaries who gain the ability to modify or trigger workflows in a linked GitHub repository can execute
12arbitrary commands on the runner host. This behavior may indicate malicious or unexpected workflow activity, including
13code execution, file manipulation, or network exfiltration initiated through a compromised repository or unauthorized
14workflow.
15"""
16false_positives = [
17 "Authorized GitHub actions runner with no malicious workflow actions.",
18]
19from = "now-9m"
20index = [
21 "endgame-*",
22 "logs-crowdstrike.fdr*",
23 "logs-endpoint.events.process-*",
24 "logs-m365_defender.event-*",
25 "logs-sentinel_one_cloud_funnel.*",
26 "logs-system.security*",
27 "logs-windows.forwarded*",
28 "logs-windows.sysmon_operational-*",
29 "winlogbeat-*",
30 "auditbeat-*",
31 "logs-auditd_manager.auditd-*"
32]
33language = "eql"
34license = "Elastic License v2"
35name = "Execution via GitHub Actions Runner"
36note = """## Triage and analysis
37
38### Investigating Execution via GitHub Actions Runner
39
40Adversaries who gain the ability to modify or trigger workflows in a linked GitHub repository can execute arbitrary commands on the runner host.
41
42### Possible investigation steps
43
44- Review the execution details like process.command_line and if it's expected or not.
45- Examine associated network and file activities and if there is any ingress tool transfer activity.
46- Verify if there is adjascent any sensitive file access or collection.
47- Correlate with other alerts and investiguate if this activity is related to a supply chain attack.
48
49### False positive analysis
50
51- Authorized github workflow actions.
52
53### Response and remediation
54
55- Immediately isolate the affected system from the network to prevent further unauthorized command execution and potential lateral movement.
56- Terminate any suspicious child processes that were initiated by the Github actions runner.
57- Conduct a thorough review of the affected system's logs and configurations to identify any unauthorized changes or additional indicators of compromise.
58- Restore the system from a known good backup if any unauthorized changes or malicious activities are confirmed.
59- Implement application whitelisting to prevent unauthorized execution.
60- Escalate the incident to the security operations center (SOC) or incident response team for further investigation and to assess the potential impact on the broader network."""
61references = [
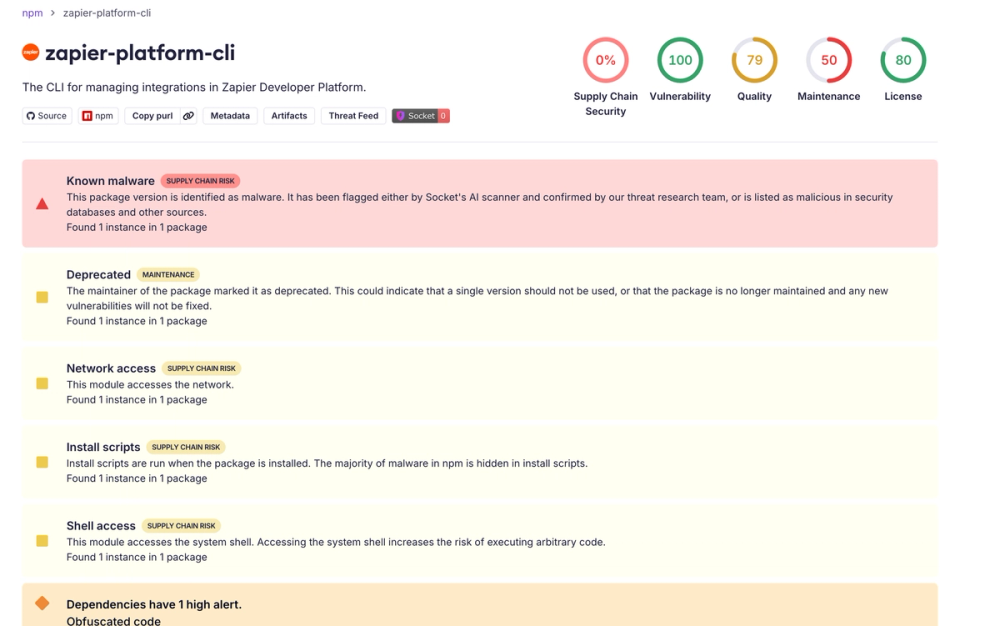
62 "https://www.elastic.co/blog/shai-hulud-worm-npm-supply-chain-compromise",
63 "https://socket.dev/blog/shai-hulud-strikes-again-v2",
64]
65risk_score = 47
66rule_id = "a640ef5b-e1da-4b17-8391-468fdbd1b517"
67severity = "medium"
68tags = [
69 "Domain: Endpoint",
70 "OS: Linux",
71 "OS: Windows",
72 "OS: macOS",
73 "Use Case: Threat Detection",
74 "Tactic: Execution",
75 "Tactic: Initial Access",
76 "Data Source: Elastic Endgame",
77 "Data Source: Elastic Defend",
78 "Data Source: Windows Security Event Logs",
79 "Data Source: Microsoft Defender for Endpoint",
80 "Data Source: Sysmon",
81 "Data Source: SentinelOne",
82 "Data Source: Crowdstrike",
83 "Data Source: Auditd Manager",
84 "Resources: Investigation Guide",
85]
86timestamp_override = "event.ingested"
87type = "eql"
88
89query = '''
90process where event.type == "start" and event.action in ("exec", "exec_event", "start", "ProcessRollup2", "executed", "process_started") and
91 process.parent.name in ("Runner.Worker", "Runner.Worker.exe") and
92 (
93 process.name like ("curl", "curl.exe", "wget", "wget.exe", "powershell.exe", "cmd.exe", "pwsh.exe", "certutil.exe", "rundll32.exe", "bash", "sh", "zsh", "tar", "rm",
94 "sed", "osascript", "chmod", "nohup", "setsid", "dash", "ash", "tcsh", "csh", "ksh", "fish", "python*", "perl*", "ruby*", "lua*", "php*", "node", "node.exe") or
95 process.executable : ("/tmp/*", "/private/tmp/*", "/var/tmp/*", "/dev/shm/*", "/run/*", "/var/run/*", "?:\\Users\\*")
96 )
97'''
98
99
100[[rule.threat]]
101framework = "MITRE ATT&CK"
102
103[[rule.threat.technique]]
104id = "T1059"
105name = "Command and Scripting Interpreter"
106reference = "https://attack.mitre.org/techniques/T1059/"
107
108[[rule.threat.technique.subtechnique]]
109id = "T1059.001"
110name = "PowerShell"
111reference = "https://attack.mitre.org/techniques/T1059/001/"
112
113[[rule.threat.technique.subtechnique]]
114id = "T1059.002"
115name = "AppleScript"
116reference = "https://attack.mitre.org/techniques/T1059/002/"
117
118[[rule.threat.technique.subtechnique]]
119id = "T1059.003"
120name = "Windows Command Shell"
121reference = "https://attack.mitre.org/techniques/T1059/003/"
122
123[[rule.threat.technique.subtechnique]]
124id = "T1059.004"
125name = "Unix Shell"
126reference = "https://attack.mitre.org/techniques/T1059/004/"
127
128[[rule.threat.technique.subtechnique]]
129id = "T1059.006"
130name = "Python"
131reference = "https://attack.mitre.org/techniques/T1059/006/"
132
133[[rule.threat.technique.subtechnique]]
134id = "T1059.007"
135name = "JavaScript"
136reference = "https://attack.mitre.org/techniques/T1059/007/"
137
138[rule.threat.tactic]
139id = "TA0002"
140name = "Execution"
141reference = "https://attack.mitre.org/tactics/TA0002/"
142
143[[rule.threat]]
144framework = "MITRE ATT&CK"
145
146[[rule.threat.technique]]
147id = "T1195"
148name = "Supply Chain Compromise"
149reference = "https://attack.mitre.org/techniques/T1195/"
150
151[[rule.threat.technique.subtechnique]]
152id = "T1195.002"
153name = "Compromise Software Supply Chain"
154reference = "https://attack.mitre.org/techniques/T1195/002/"
155
156[rule.threat.tactic]
157id = "TA0001"
158name = "Initial Access"
159reference = "https://attack.mitre.org/tactics/TA0001/"
160
161[[rule.threat]]
162framework = "MITRE ATT&CK"
163
164[[rule.threat.technique]]
165id = "T1218"
166name = "System Binary Proxy Execution"
167reference = "https://attack.mitre.org/techniques/T1218/"
168
169[[rule.threat.technique.subtechnique]]
170id = "T1218.011"
171name = "Rundll32"
172reference = "https://attack.mitre.org/techniques/T1218/011/"
173
174[rule.threat.tactic]
175id = "TA0005"
176name = "Defense Evasion"
177reference = "https://attack.mitre.org/tactics/TA0005/"
Triage and analysis
Investigating Execution via GitHub Actions Runner
Adversaries who gain the ability to modify or trigger workflows in a linked GitHub repository can execute arbitrary commands on the runner host.
Possible investigation steps
- Review the execution details like process.command_line and if it's expected or not.
- Examine associated network and file activities and if there is any ingress tool transfer activity.
- Verify if there is adjascent any sensitive file access or collection.
- Correlate with other alerts and investiguate if this activity is related to a supply chain attack.
False positive analysis
- Authorized github workflow actions.
Response and remediation
- Immediately isolate the affected system from the network to prevent further unauthorized command execution and potential lateral movement.
- Terminate any suspicious child processes that were initiated by the Github actions runner.
- Conduct a thorough review of the affected system's logs and configurations to identify any unauthorized changes or additional indicators of compromise.
- Restore the system from a known good backup if any unauthorized changes or malicious activities are confirmed.
- Implement application whitelisting to prevent unauthorized execution.
- Escalate the incident to the security operations center (SOC) or incident response team for further investigation and to assess the potential impact on the broader network.
References
Related rules
- Remote GitHub Actions Runner Registration
- Credential Access via TruffleHog Execution
- Kubernetes Direct API Request via Curl or Wget
- Potential Secret Scanning via Gitleaks
- Potential Foxmail Exploitation