RDP Sensitive Settings Changed
Detects tampering of RDP Terminal Service/Server sensitive settings. Such as allowing unauthorized users access to a system via the 'fAllowUnsolicited' or enabling RDP via 'fDenyTSConnections', etc.
Below is a list of registry keys/values that are monitored by this rule:
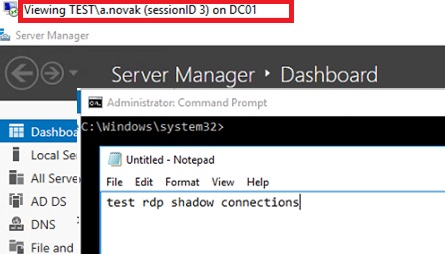
- Shadow: Used to enable Remote Desktop shadowing, which allows an administrator to view or control a user's session.
- DisableRemoteDesktopAntiAlias: Disables anti-aliasing for remote desktop sessions.
- DisableSecuritySettings: Disables certain security settings for Remote Desktop connections.
- fAllowUnsolicited: Allows unsolicited remote assistance offers.
- fAllowUnsolicitedFullControl: Allows unsolicited remote assistance offers with full control.
- InitialProgram: Specifies a program to run automatically when a user logs on to a remote computer.
- ServiceDll: Used in RDP hijacking techniques to specify a custom DLL to be loaded by the Terminal Services service.
- SecurityLayer: Specifies the security layer used for RDP connections.
Sigma rule (View on GitHub)
1title: RDP Sensitive Settings Changed
2id: 3f6b7b62-61aa-45db-96bd-9c31b36b653c
3related:
4 - id: 171b67e1-74b4-460e-8d55-b331f3e32d67
5 type: obsolete
6 - id: 41904ebe-d56c-4904-b9ad-7a77bdf154b3
7 type: obsolete
8 - id: a2863fbc-d5cb-48d5-83fb-d976d4b1743b
9 type: similar
10status: test
11description: |
12 Detects tampering of RDP Terminal Service/Server sensitive settings.
13 Such as allowing unauthorized users access to a system via the 'fAllowUnsolicited' or enabling RDP via 'fDenyTSConnections', etc.
14
15 Below is a list of registry keys/values that are monitored by this rule:
16
17 - Shadow: Used to enable Remote Desktop shadowing, which allows an administrator to view or control a user's session.
18 - DisableRemoteDesktopAntiAlias: Disables anti-aliasing for remote desktop sessions.
19 - DisableSecuritySettings: Disables certain security settings for Remote Desktop connections.
20 - fAllowUnsolicited: Allows unsolicited remote assistance offers.
21 - fAllowUnsolicitedFullControl: Allows unsolicited remote assistance offers with full control.
22 - InitialProgram: Specifies a program to run automatically when a user logs on to a remote computer.
23 - ServiceDll: Used in RDP hijacking techniques to specify a custom DLL to be loaded by the Terminal Services service.
24 - SecurityLayer: Specifies the security layer used for RDP connections.
25references:
26 - http://etutorials.org/Microsoft+Products/microsoft+windows+server+2003+terminal+services/Chapter+6+Registry/Registry+Keys+for+Terminal+Services/ # Contains description for most of the keys mentioned here (check it out if you want more information)
27 - http://woshub.com/rds-shadow-how-to-connect-to-a-user-session-in-windows-server-2012-r2/ # Related to the Shadow RPD technique
28 - https://admx.help/HKLM/SOFTWARE/Policies/Microsoft/Windows%20NT/Terminal%20Services # Contains description for most of the keys mentioned here (check it out if you want more information)
29 - https://bazaar.abuse.ch/sample/6f3aa9362d72e806490a8abce245331030d1ab5ac77e400dd475748236a6cc81/
30 - https://blog.sekoia.io/darkgate-internals/
31 - https://blog.talosintelligence.com/understanding-the-phobos-affiliate-structure/
32 - https://github.com/redcanaryco/atomic-red-team/blob/02c7d02fe1f1feb0fc7944550408ea8224273994/atomics/T1112/T1112.md#atomic-test-63---disable-remote-desktop-anti-alias-setting-through-registry
33 - https://github.com/redcanaryco/atomic-red-team/blob/02c7d02fe1f1feb0fc7944550408ea8224273994/atomics/T1112/T1112.md#atomic-test-64---disable-remote-desktop-security-settings-through-registry
34 - https://github.com/redcanaryco/atomic-red-team/blob/dd526047b8c399c312fee47d1e6fb531164da54d/atomics/T1112/T1112.yaml#L790
35 - https://learn.microsoft.com/en-us/windows-hardware/customize/desktop/unattend/microsoft-windows-terminalservices-rdp-winstationextensions-securitylayer
36 - https://threathunterplaybook.com/hunts/windows/190407-RegModEnableRDPConnections/notebook.html
37 - https://twitter.com/SagieSec/status/1469001618863624194?t=HRf0eA0W1YYzkTSHb-Ky1A&s=03 # Related to the Shadow RPD technique
38 - https://web.archive.org/web/20200929062532/https://blog.menasec.net/2019/02/threat-hunting-rdp-hijacking-via.html # Related to RDP hijacking via the "ServiceDll" key
39 - https://www.trendmicro.com/en_us/research/25/i/unmasking-the-gentlemen-ransomware.html
40author: Samir Bousseaden, David ANDRE, Roberto Rodriguez @Cyb3rWard0g, Nasreddine Bencherchali
41date: 2022-08-06
42modified: 2025-11-22
43tags:
44 - attack.defense-evasion
45 - attack.persistence
46 - attack.t1112
47logsource:
48 category: registry_set
49 product: windows
50detection:
51 selection_shadow:
52 TargetObject|contains:
53 - '\Control\Terminal Server\'
54 - '\Windows NT\Terminal Services\'
55 TargetObject|endswith: '\Shadow'
56 Details:
57 - 'DWORD (0x00000001)' # Full Control with user’s permission
58 - 'DWORD (0x00000002)' # Full Control without user’s permission
59 - 'DWORD (0x00000003)' # View Session with user’s permission
60 - 'DWORD (0x00000004)' # View Session without user’s permission
61 selection_terminal_services_key:
62 TargetObject|contains:
63 - '\Control\Terminal Server\'
64 - '\Windows NT\Terminal Services\'
65 TargetObject|endswith:
66 - '\DisableRemoteDesktopAntiAlias' # Disable anti-aliasing for remote desktop (DarkGate malware)
67 - '\DisableSecuritySettings' # Disable security settings, allowing access to programs/entire desktop (DarkGate malware)
68 - '\fAllowUnsolicited' # Allow unsolicited remote assistance offers
69 - '\fAllowUnsolicitedFullControl'
70 Details: 'DWORD (0x00000001)'
71 selection_tamper_only:
72 # Any changes to these keys should be suspicious and looked at
73 TargetObject|contains:
74 - '\Control\Terminal Server\InitialProgram' # This value can be set to specify a program to run automatically when a user logs on to a remote computer.
75 - '\Control\Terminal Server\WinStations\RDP-Tcp\InitialProgram' # This value can be set to specify a program to run automatically when a user logs on to a remote computer.
76 - '\services\TermService\Parameters\ServiceDll' # RDP hijacking
77 - '\Terminal Server\WinStations\RDP-Tcp\SecurityLayer'
78 - '\Windows NT\Terminal Services\InitialProgram' # This value can be set to specify a program to run automatically when a user logs on to a remote computer.
79 filter_main_securitylayer_tls:
80 TargetObject|endswith: '\SecurityLayer'
81 Details: 'DWORD (0x00000002)' # TLS Enabled
82 condition: (selection_shadow or selection_terminal_services_key or selection_tamper_only) and not 1 of filter_main_*
83falsepositives:
84 - Some of the keys mentioned here could be modified by an administrator while setting group policy (it should be investigated either way)
85level: high
References
Related rules
- Potential Tampering With RDP Related Registry Keys Via Reg.EXE
- Registry Modification Attempt Via VBScript
- Registry Modification Attempt Via VBScript - PowerShell
- Registry Tampering by Potentially Suspicious Processes
- RDP Sensitive Settings Changed to Zero