Whoami.EXE Execution Anomaly
Detects the execution of whoami.exe with suspicious parent processes.
Sigma rule (View on GitHub)
1title: Whoami.EXE Execution Anomaly
2id: 8de1cbe8-d6f5-496d-8237-5f44a721c7a0
3status: test
4description: Detects the execution of whoami.exe with suspicious parent processes.
5references:
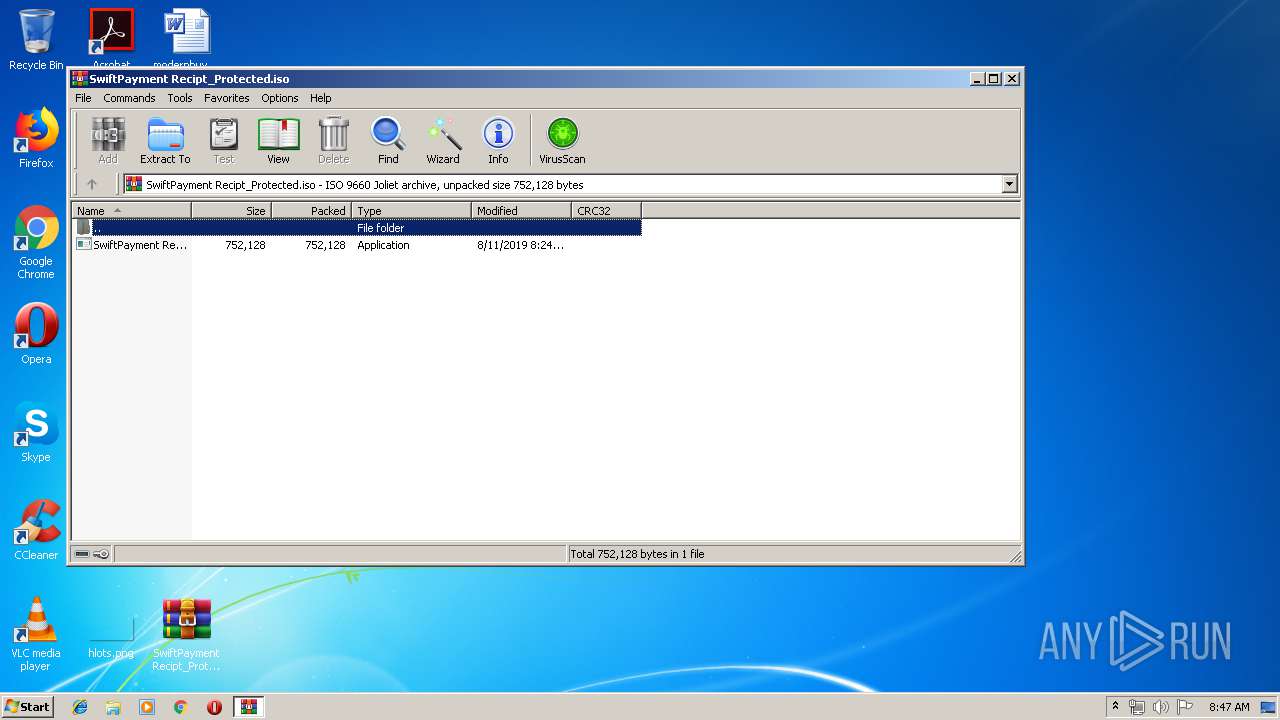
6 - https://brica.de/alerts/alert/public/1247926/agent-tesla-keylogger-delivered-inside-a-power-iso-daa-archive/
7 - https://app.any.run/tasks/7eaba74e-c1ea-400f-9c17-5e30eee89906/
8 - https://www.youtube.com/watch?v=DsJ9ByX84o4&t=6s
9author: Florian Roth (Nextron Systems)
10date: 2021-08-12
11modified: 2025-03-06
12tags:
13 - attack.discovery
14 - attack.t1033
15 - car.2016-03-001
16logsource:
17 category: process_creation
18 product: windows
19detection:
20 selection:
21 - Image|endswith: '\whoami.exe'
22 - OriginalFileName: 'whoami.exe'
23 filter_main_known_parents:
24 # This list can be any legitimate shell or application that you expect whoami to run from
25 ParentImage|endswith:
26 - '\cmd.exe'
27 - '\powershell_ise.exe'
28 - '\powershell.exe'
29 - '\pwsh.exe'
30 filter_optional_ms_monitoring_agent:
31 ParentImage|endswith: ':\Program Files\Microsoft Monitoring Agent\Agent\MonitoringHost.exe'
32 filter_main_parent_null:
33 ParentImage: null
34 filter_main_parent_empty:
35 ParentImage:
36 - ''
37 - '-'
38 condition: selection and not 1 of filter_main_* and not 1 of filter_optional_*
39falsepositives:
40 - Admin activity
41 - Scripts and administrative tools used in the monitored environment
42 - Monitoring activity
43level: medium
References
Related rules
- Whoami.EXE Execution With Output Option
- HackTool - SharpLdapWhoami Execution
- Renamed Whoami Execution
- WhoAmI as Parameter
- Whoami.EXE Execution From Privileged Process