Whoami Utility Execution
Detects the execution of whoami, which is often used by attackers after exploitation / privilege escalation
Sigma rule (View on GitHub)
1title: Whoami Utility Execution
2id: e28a5a99-da44-436d-b7a0-2afc20a5f413
3status: test
4description: Detects the execution of whoami, which is often used by attackers after exploitation / privilege escalation
5references:
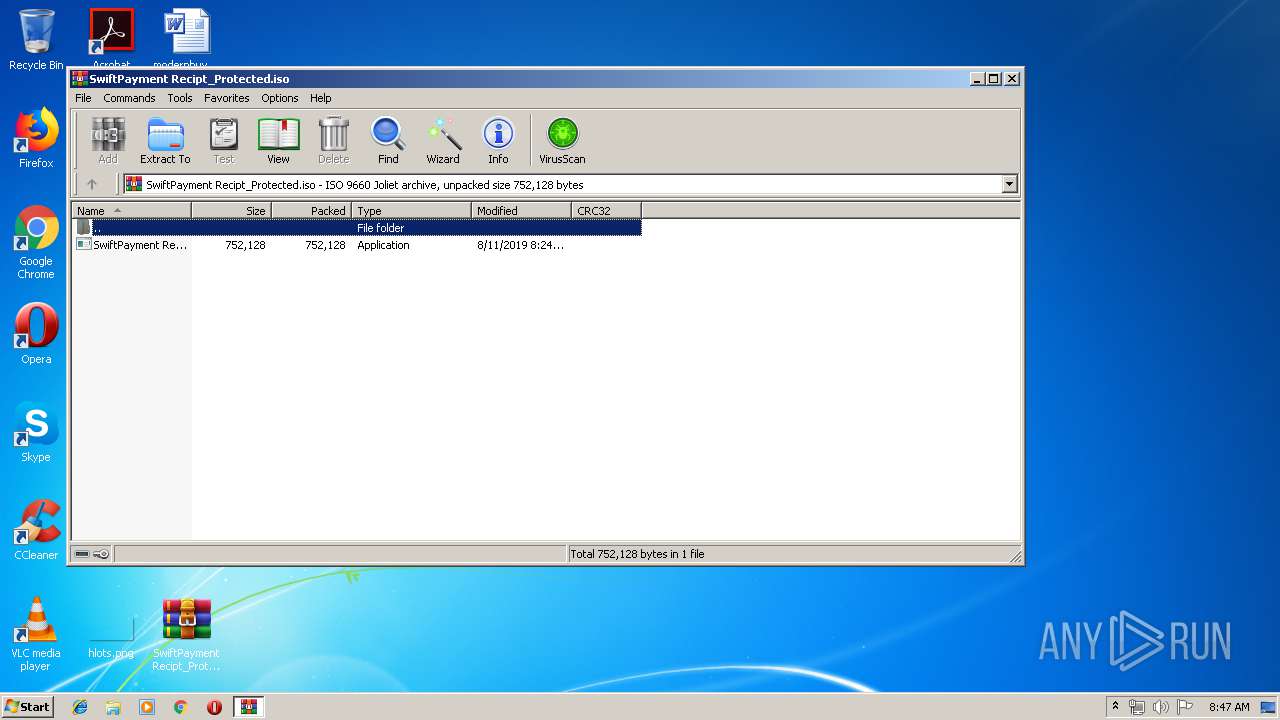
6 - https://brica.de/alerts/alert/public/1247926/agent-tesla-keylogger-delivered-inside-a-power-iso-daa-archive/
7 - https://app.any.run/tasks/7eaba74e-c1ea-400f-9c17-5e30eee89906/
8author: Florian Roth (Nextron Systems)
9date: 2018-08-13
10modified: 2023-11-30
11tags:
12 - attack.discovery
13 - attack.t1033
14 - car.2016-03-001
15logsource:
16 category: process_creation
17 product: windows
18detection:
19 selection:
20 - Image|endswith: '\whoami.exe'
21 - OriginalFileName: 'whoami.exe'
22 condition: selection
23falsepositives:
24 - Admin activity
25 - Scripts and administrative tools used in the monitored environment
26 - Monitoring activity
27level: low
References
Related rules
- HackTool - SharpLdapWhoami Execution
- Renamed Whoami Execution
- WhoAmI as Parameter
- Cisco Discovery
- Computer Discovery And Export Via Get-ADComputer Cmdlet