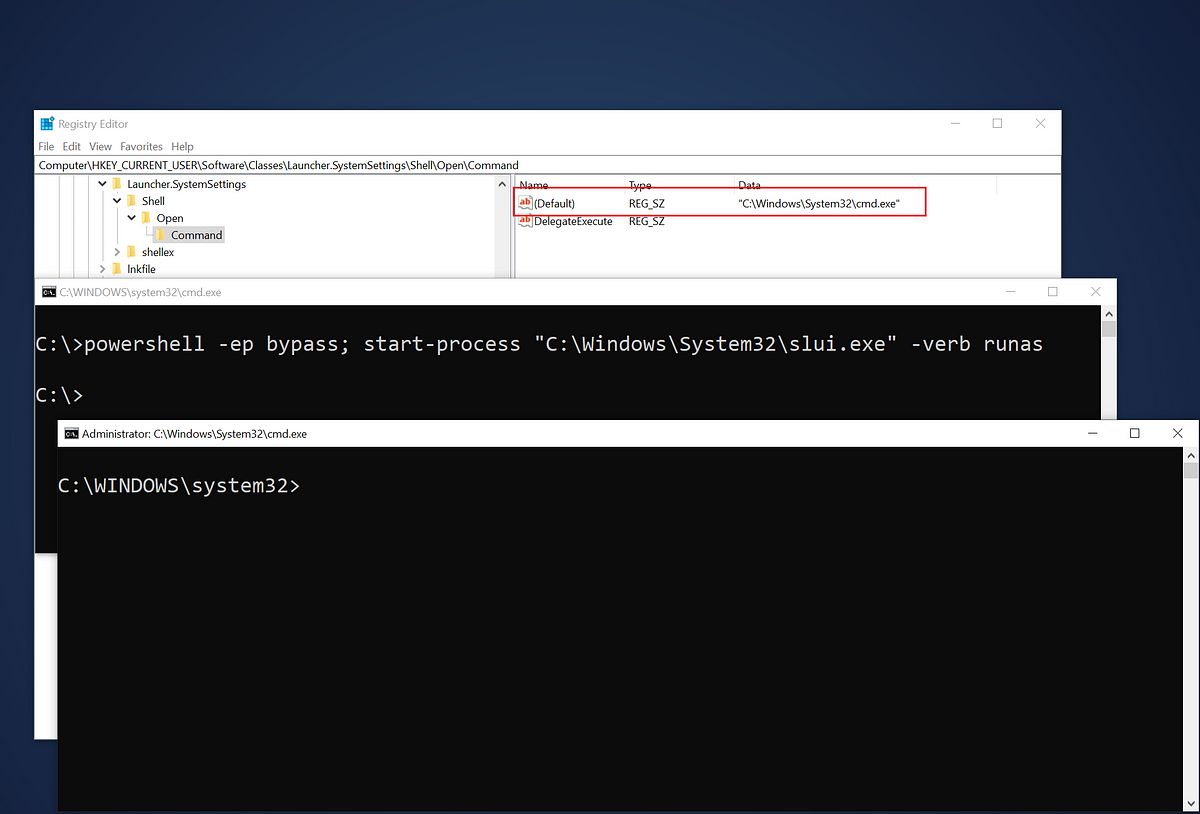
UAC Bypass Using ChangePK and SLUI
Detects an UAC bypass that uses changepk.exe and slui.exe (UACMe 61)
Sigma rule (View on GitHub)
1title: UAC Bypass Using ChangePK and SLUI
2id: 503d581c-7df0-4bbe-b9be-5840c0ecc1fc
3status: test
4description: Detects an UAC bypass that uses changepk.exe and slui.exe (UACMe 61)
5references:
6 - https://mattharr0ey.medium.com/privilege-escalation-uac-bypass-in-changepk-c40b92818d1b
7 - https://github.com/hfiref0x/UACME
8 - https://medium.com/falconforce/falconfriday-detecting-uac-bypasses-0xff16-86c2a9107abf
9author: Christian Burkard (Nextron Systems)
10date: 2021-08-23
11modified: 2024-12-01
12tags:
13 - attack.defense-evasion
14 - attack.privilege-escalation
15 - attack.t1548.002
16logsource:
17 category: process_creation
18 product: windows
19detection:
20 selection:
21 Image|endswith: '\changepk.exe'
22 ParentImage|endswith: '\slui.exe'
23 IntegrityLevel:
24 - 'High'
25 - 'System'
26 - 'S-1-16-16384' # System
27 - 'S-1-16-12288' # High
28 condition: selection
29falsepositives:
30 - Unknown
31level: high
References
Related rules
- CMSTP UAC Bypass via COM Object Access
- Potential UAC Bypass Via Sdclt.EXE
- UAC Bypass Abusing Winsat Path Parsing - Process
- UAC Bypass Tools Using ComputerDefaults
- UAC Bypass Using Consent and Comctl32 - Process