Loaded Module Enumeration Via Tasklist.EXE
Detects the enumeration of a specific DLL or EXE being used by a binary via "tasklist.exe". This is often used by attackers in order to find the specific process identifier (PID) that is using the DLL in question. In order to dump the process memory or perform other nefarious actions.
Sigma rule (View on GitHub)
1title: Loaded Module Enumeration Via Tasklist.EXE
2id: 34275eb8-fa19-436b-b959-3d9ecd53fa1f
3status: test
4description: |
5 Detects the enumeration of a specific DLL or EXE being used by a binary via "tasklist.exe".
6 This is often used by attackers in order to find the specific process identifier (PID) that is using the DLL in question.
7 In order to dump the process memory or perform other nefarious actions.
8references:
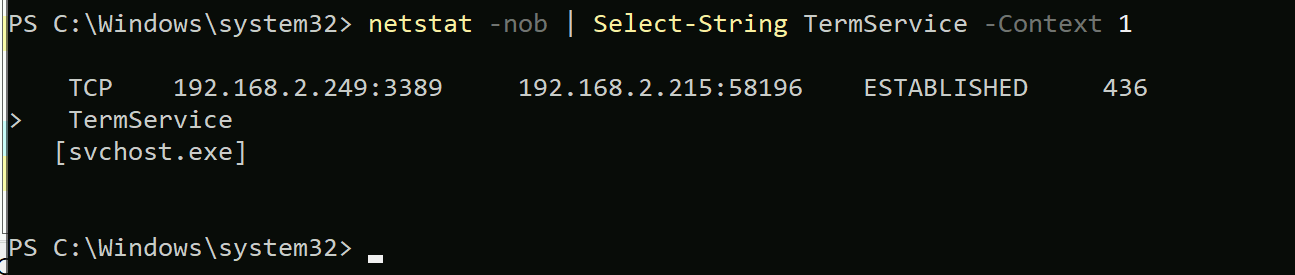
9 - https://www.n00py.io/2021/05/dumping-plaintext-rdp-credentials-from-svchost-exe/
10 - https://pentestlab.blog/tag/svchost/
11author: Swachchhanda Shrawan Poudel
12date: 2024-02-12
13modified: 2024-03-13
14tags:
15 - attack.t1003
16 - attack.credential-access
17logsource:
18 product: windows
19 category: process_creation
20detection:
21 selection_img:
22 - Image|endswith: '\tasklist.exe'
23 - OriginalFileName: 'tasklist.exe'
24 selection_flags:
25 CommandLine|contains|windash: '-m'
26 selection_module:
27 # Note: add other interesting modules or binaries
28 CommandLine|contains: 'rdpcorets.dll'
29 condition: all of selection_*
30falsepositives:
31 - Unknown
32level: medium
References
Related rules
- Hacktool Execution - Imphash
- Interesting Service Enumeration Via Sc.EXE
- Live Memory Dump Using Powershell
- Potentially Suspicious ODBC Driver Registered
- Rare Subscription-level Operations In Azure