Suspicious Regsvr32 Execution From Remote Share
Detects REGSVR32.exe to execute DLL hosted on remote shares
Sigma rule (View on GitHub)
1title: Suspicious Regsvr32 Execution From Remote Share
2id: 88a87a10-384b-4ad7-8871-2f9bf9259ce5
3status: test
4description: Detects REGSVR32.exe to execute DLL hosted on remote shares
5references:
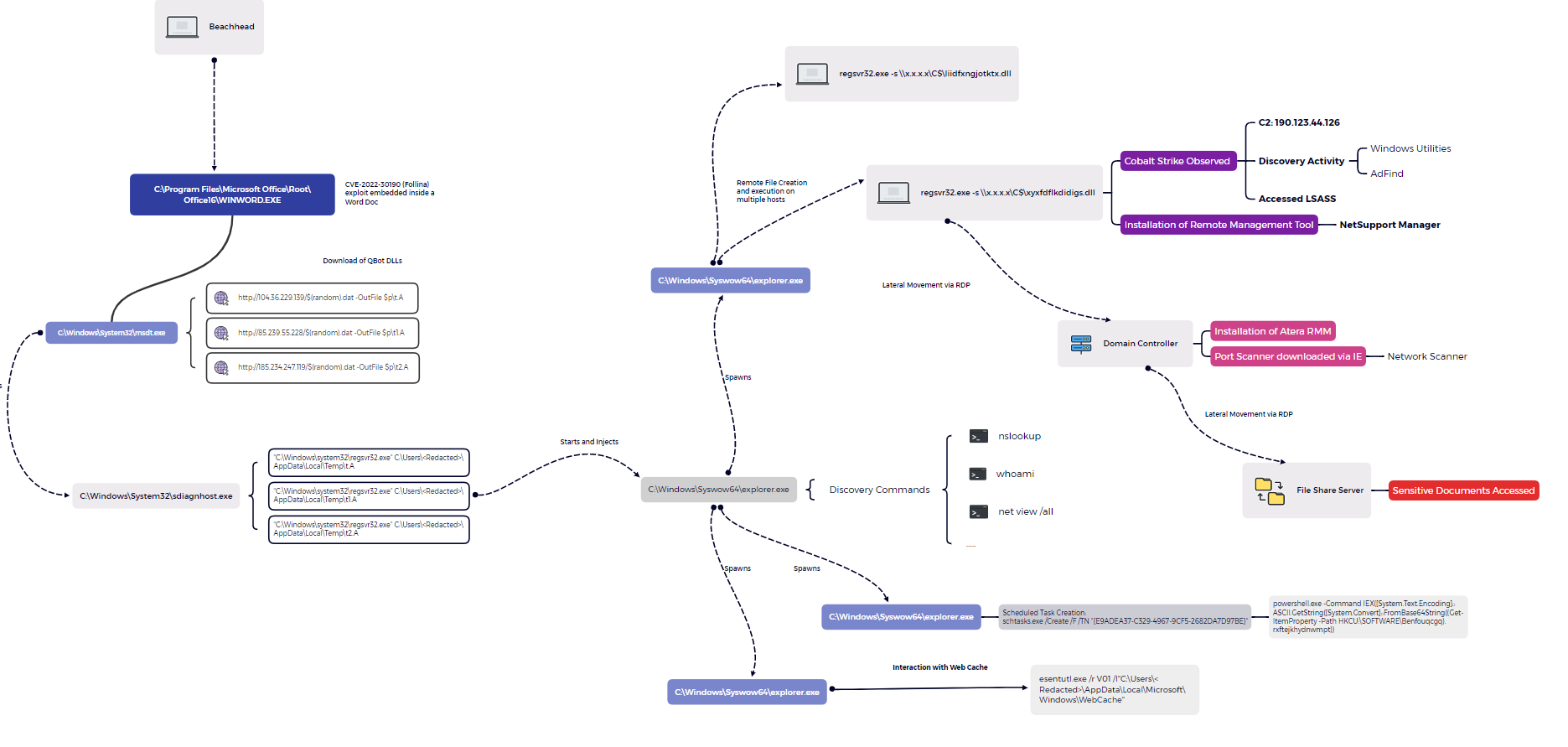
6 - https://thedfirreport.com/2022/10/31/follina-exploit-leads-to-domain-compromise/
7author: Nasreddine Bencherchali (Nextron Systems)
8date: 2022-10-31
9tags:
10 - attack.defense-evasion
11 - attack.t1218.010
12logsource:
13 category: process_creation
14 product: windows
15detection:
16 selection_img:
17 - Image|endswith: '\regsvr32.exe'
18 - OriginalFileName: '\REGSVR32.EXE'
19 selection_cli:
20 CommandLine|contains: ' \\\\'
21 condition: all of selection_*
22falsepositives:
23 - Unknown
24# Decrease to medium if this is something common in your org
25level: high
References
Related rules
- DNS Query Request By Regsvr32.EXE
- HTML Help HH.EXE Suspicious Child Process
- Network Connection Initiated By Regsvr32.EXE
- Potential APT-C-12 BlueMushroom DLL Load Activity Via Regsvr32
- Potential EmpireMonkey Activity