RestrictedAdminMode Registry Value Tampering - ProcCreation
Detects changes to the "DisableRestrictedAdmin" registry value in order to disable or enable RestrictedAdmin mode. RestrictedAdmin mode prevents the transmission of reusable credentials to the remote system to which you connect using Remote Desktop. This prevents your credentials from being harvested during the initial connection process if the remote server has been compromise
Sigma rule (View on GitHub)
1title: RestrictedAdminMode Registry Value Tampering - ProcCreation
2id: 28ac00d6-22d9-4a3c-927f-bbd770104573
3related:
4 - id: d6ce7ebd-260b-4323-9768-a9631c8d4db2 # Registry
5 type: similar
6status: test
7description: |
8 Detects changes to the "DisableRestrictedAdmin" registry value in order to disable or enable RestrictedAdmin mode.
9 RestrictedAdmin mode prevents the transmission of reusable credentials to the remote system to which you connect using Remote Desktop.
10 This prevents your credentials from being harvested during the initial connection process if the remote server has been compromise
11references:
12 - https://github.com/redcanaryco/atomic-red-team/blob/a8e3cf63e97b973a25903d3df9fd55da6252e564/atomics/T1112/T1112.md
13 - https://social.technet.microsoft.com/wiki/contents/articles/32905.remote-desktop-services-enable-restricted-admin-mode.aspx
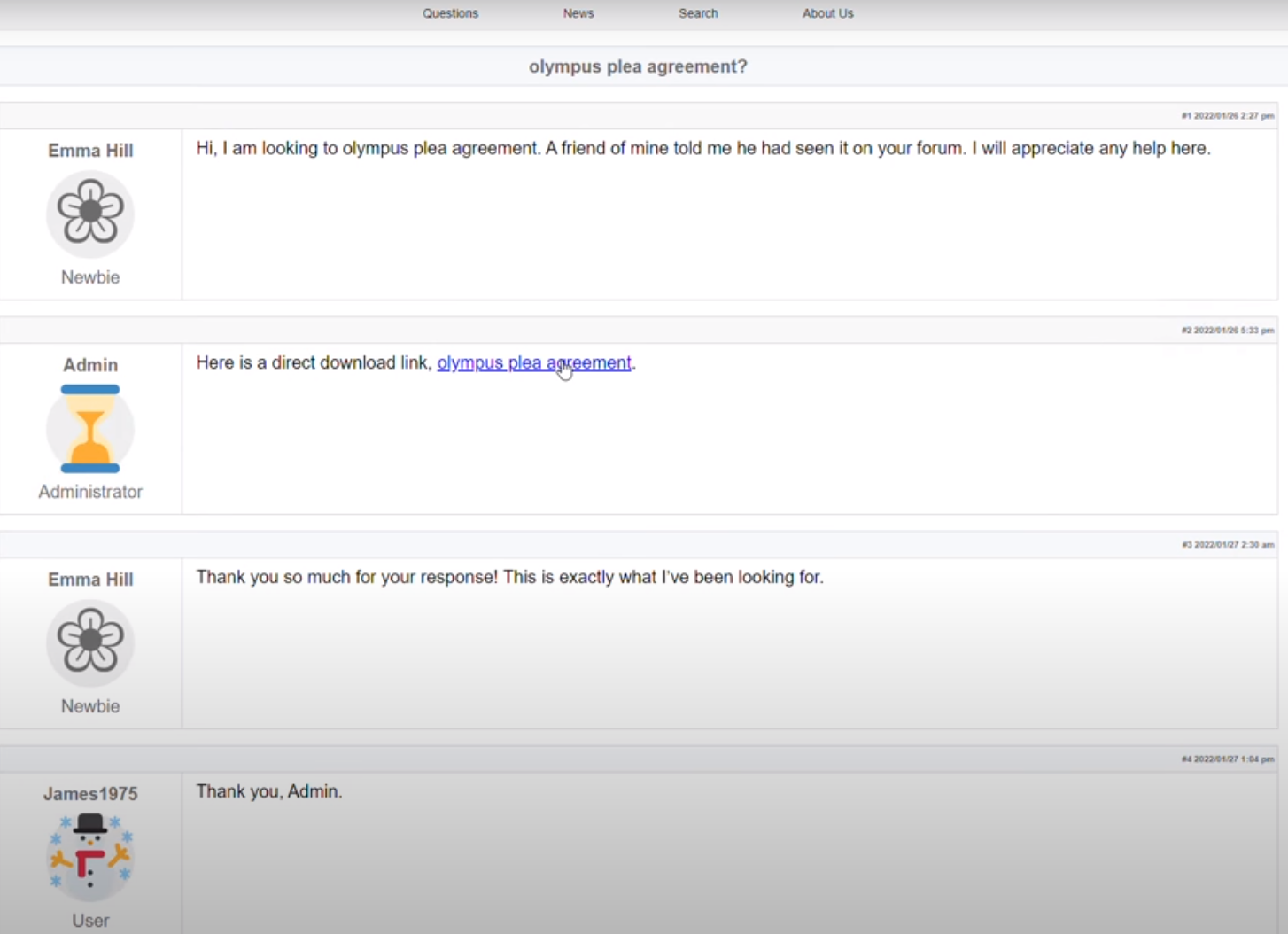
14 - https://thedfirreport.com/2022/05/09/seo-poisoning-a-gootloader-story/
15author: frack113
16date: 2023-01-13
17modified: 2025-08-28
18tags:
19 - attack.persistence
20 - attack.defense-evasion
21 - attack.t1112
22logsource:
23 product: windows
24 category: process_creation
25detection:
26 selection:
27 CommandLine|contains|all:
28 - '\System\CurrentControlSet\Control\Lsa'
29 - 'DisableRestrictedAdmin'
30 condition: selection
31falsepositives:
32 - Unknown
33level: high
References
Related rules
- Activate Suppression of Windows Security Center Notifications
- Add DisallowRun Execution to Registry
- Blackbyte Ransomware Registry
- Blue Mockingbird
- Change User Account Associated with the FAX Service