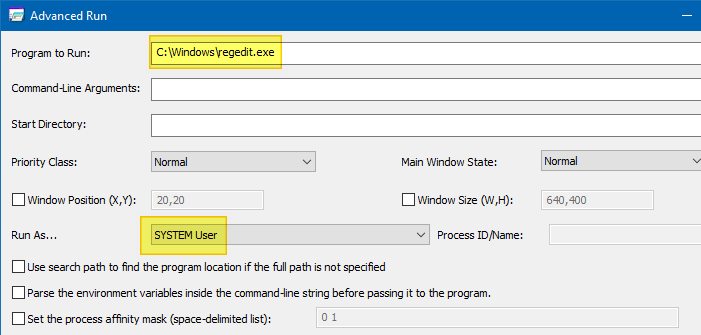
PUA - AdvancedRun Execution
Detects the execution of AdvancedRun utility
Sigma rule (View on GitHub)
1title: PUA - AdvancedRun Execution
2id: d2b749ee-4225-417e-b20e-a8d2193cbb84
3related:
4 - id: fa00b701-44c6-4679-994d-5a18afa8a707
5 type: similar
6status: test
7description: Detects the execution of AdvancedRun utility
8references:
9 - https://twitter.com/splinter_code/status/1483815103279603714
10 - https://medium.com/s2wblog/analysis-of-destructive-malware-whispergate-targeting-ukraine-9d5d158f19f3
11 - https://www.elastic.co/security-labs/operation-bleeding-bear
12 - https://www.winhelponline.com/blog/run-program-as-system-localsystem-account-windows/
13author: Florian Roth (Nextron Systems)
14date: 2022-01-20
15modified: 2023-02-21
16tags:
17 - attack.execution
18 - attack.defense-evasion
19 - attack.privilege-escalation
20 - attack.t1564.003
21 - attack.t1134.002
22 - attack.t1059.003
23logsource:
24 product: windows
25 category: process_creation
26detection:
27 selection:
28 - OriginalFileName: 'AdvancedRun.exe'
29 - CommandLine|contains|all:
30 - ' /EXEFilename '
31 - ' /Run'
32 - CommandLine|contains|all:
33 - ' /WindowState 0'
34 - ' /RunAs '
35 - ' /CommandLine '
36 condition: selection
37falsepositives:
38 - Unknown
39level: medium
40regression_tests_path: regression_data/rules/windows/process_creation/proc_creation_win_pua_advancedrun/info.yml
References
Related rules
- Powershell Executed From Headless ConHost Process
- Exploiting SetupComplete.cmd CVE-2019-1378
- PUA - AdvancedRun Suspicious Execution
- Unsigned .node File Loaded
- HackTool - CrackMapExec Execution