Suspicious SysAidServer Child
Detects suspicious child processes of SysAidServer (as seen in MERCURY threat actor intrusions)
Sigma rule (View on GitHub)
1title: Suspicious SysAidServer Child
2id: 60bfeac3-0d35-4302-8efb-1dd16f715bc6
3status: test
4description: Detects suspicious child processes of SysAidServer (as seen in MERCURY threat actor intrusions)
5references:
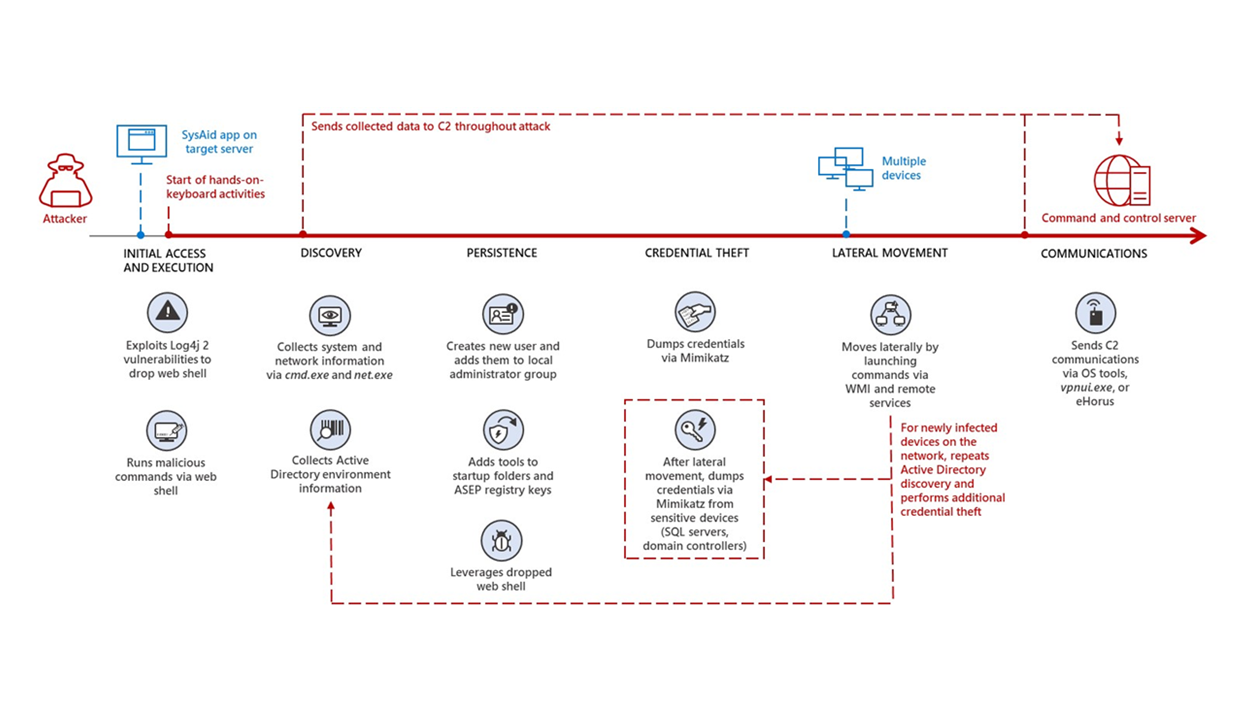
6 - https://www.microsoft.com/security/blog/2022/08/25/mercury-leveraging-log4j-2-vulnerabilities-in-unpatched-systems-to-target-israeli-organizations/
7author: Florian Roth (Nextron Systems)
8date: 2022-08-26
9tags:
10 - attack.lateral-movement
11 - attack.t1210
12logsource:
13 category: process_creation
14 product: windows
15detection:
16 selection:
17 ParentImage|endswith:
18 - '\java.exe'
19 - '\javaw.exe'
20 ParentCommandLine|contains: 'SysAidServer'
21 condition: selection
22falsepositives:
23 - Unknown
24level: medium
References
Related rules
- Apache Threading Error
- Audit CVE Event
- Terminal Service Process Spawn
- Zerologon Exploitation Using Well-known Tools
- Access To ADMIN$ Network Share