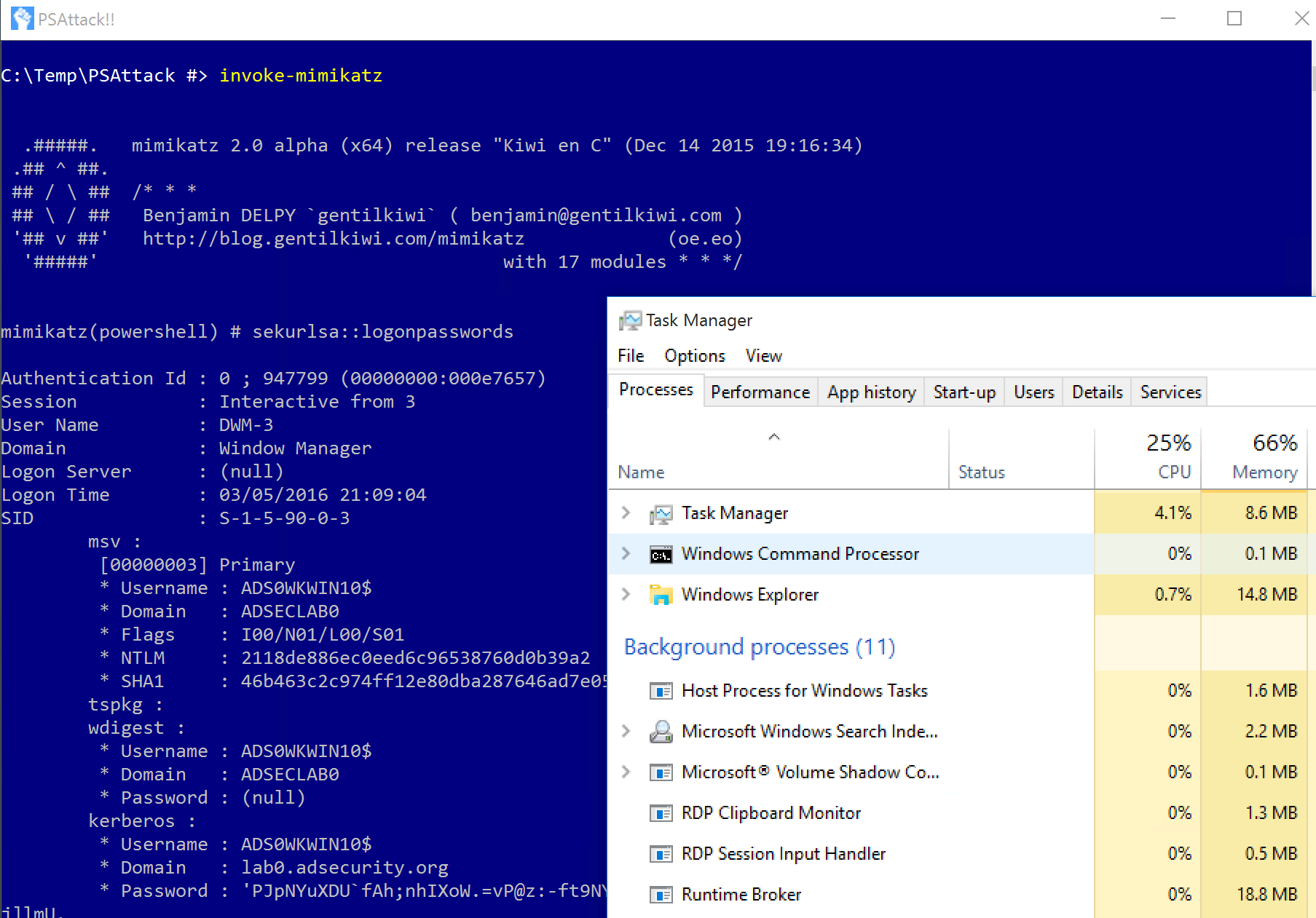
PowerShell PSAttack
Detects the use of PSAttack PowerShell hack tool
Sigma rule (View on GitHub)
1title: PowerShell PSAttack
2id: b7ec41a4-042c-4f31-a5db-d0fcde9fa5c5
3status: test
4description: Detects the use of PSAttack PowerShell hack tool
5references:
6 - https://adsecurity.org/?p=2921
7author: Sean Metcalf (source), Florian Roth (Nextron Systems)
8date: 2017-03-05
9modified: 2022-12-25
10tags:
11 - attack.execution
12 - attack.t1059.001
13logsource:
14 product: windows
15 category: ps_script
16 definition: 'Requirements: Script Block Logging must be enabled'
17detection:
18 selection:
19 ScriptBlockText|contains: 'PS ATTACK!!!'
20 condition: selection
21falsepositives:
22 - Unknown
23level: high
References
Related rules
- AWS EC2 Startup Shell Script Change
- Bad Opsec Powershell Code Artifacts
- Certificate Exported Via PowerShell
- Change PowerShell Policies to an Insecure Level - PowerShell
- Cmd.EXE Missing Space Characters Execution Anomaly