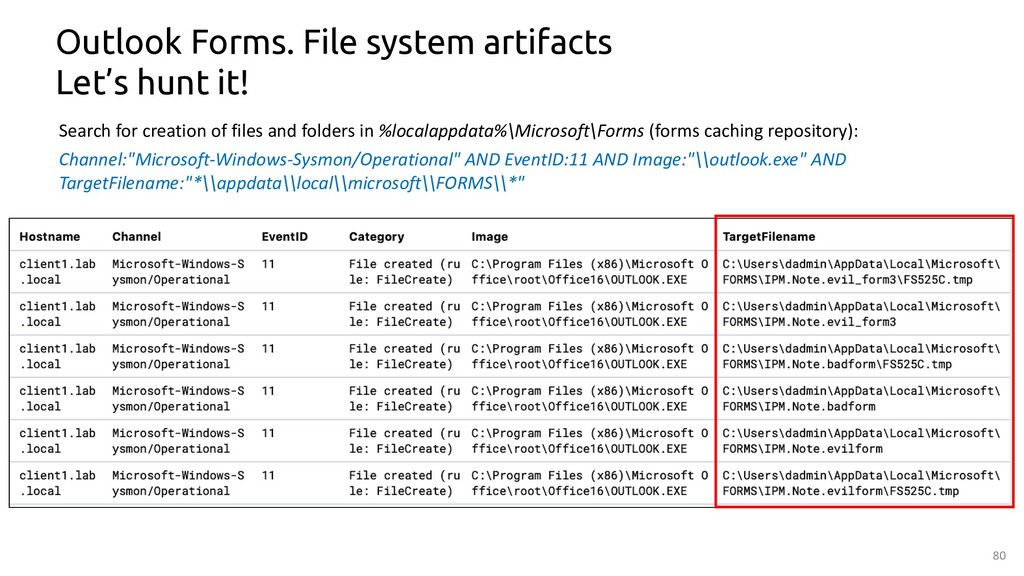
Potential Persistence Via Outlook Form
Detects the creation of a new Outlook form which can contain malicious code
Sigma rule (View on GitHub)
1title: Potential Persistence Via Outlook Form
2id: c3edc6a5-d9d4-48d8-930e-aab518390917
3status: test
4description: Detects the creation of a new Outlook form which can contain malicious code
5references:
6 - https://speakerdeck.com/heirhabarov/hunting-for-persistence-via-microsoft-exchange-server-or-outlook?slide=76
7 - https://speakerdeck.com/heirhabarov/hunting-for-persistence-via-microsoft-exchange-server-or-outlook?slide=79
8 - https://learn.microsoft.com/en-us/office/vba/outlook/concepts/outlook-forms/create-an-outlook-form
9 - https://www.slipstick.com/developer/custom-form/clean-outlooks-forms-cache/
10author: Tobias Michalski (Nextron Systems)
11date: 2021-06-10
12modified: 2023-02-22
13tags:
14 - attack.persistence
15 - attack.t1137.003
16logsource:
17 product: windows
18 category: file_event
19detection:
20 selection:
21 Image|endswith: '\outlook.exe'
22 TargetFilename|contains:
23 - '\AppData\Local\Microsoft\FORMS\IPM'
24 - '\Local Settings\Application Data\Microsoft\Forms' # Windows XP
25 condition: selection
26falsepositives:
27 - Legitimate use of outlook forms
28level: high
References
Related rules
- AWS ECS Task Definition That Queries The Credential Endpoint
- AWS ElastiCache Security Group Created
- Abuse of Service Permissions to Hide Services Via Set-Service
- Abuse of Service Permissions to Hide Services Via Set-Service - PS
- Activity From Anonymous IP Address