PetitPotam Suspicious Kerberos TGT Request
Detect suspicious Kerberos TGT requests. Once an attacer obtains a computer certificate by abusing Active Directory Certificate Services in combination with PetitPotam, the next step would be to leverage the certificate for malicious purposes. One way of doing this is to request a Kerberos Ticket Granting Ticket using a tool like Rubeus. This request will generate a 4768 event with some unusual fields depending on the environment. This analytic will require tuning, we recommend filtering Account_Name to the Domain Controller computer accounts.
Sigma rule (View on GitHub)
1title: PetitPotam Suspicious Kerberos TGT Request
2id: 6a53d871-682d-40b6-83e0-b7c1a6c4e3a5
3status: test
4description: |
5 Detect suspicious Kerberos TGT requests.
6 Once an attacer obtains a computer certificate by abusing Active Directory Certificate Services in combination with PetitPotam, the next step would be to leverage the certificate for malicious purposes.
7 One way of doing this is to request a Kerberos Ticket Granting Ticket using a tool like Rubeus.
8 This request will generate a 4768 event with some unusual fields depending on the environment.
9 This analytic will require tuning, we recommend filtering Account_Name to the Domain Controller computer accounts.
10references:
11 - https://github.com/topotam/PetitPotam
12 - https://isc.sans.edu/forums/diary/Active+Directory+Certificate+Services+ADCS+PKI+domain+admin+vulnerability/27668/
13 - https://github.com/splunk/security_content/blob/88d689fe8a055d8284337b9fad5d9152b42043db/detections/endpoint/petitpotam_suspicious_kerberos_tgt_request.yml
14author: Mauricio Velazco, Michael Haag
15date: 2021-09-02
16modified: 2022-10-05
17tags:
18 - attack.credential-access
19 - attack.t1187
20logsource:
21 product: windows
22 service: security
23 definition: 'The advanced audit policy setting "Account Logon > Kerberos Authentication Service" must be configured for Success/Failure'
24detection:
25 selection:
26 EventID: 4768
27 TargetUserName|endswith: '$'
28 CertThumbprint|contains: '*'
29 filter_local:
30 IpAddress: '::1'
31 filter_thumbprint:
32 CertThumbprint: ''
33 condition: selection and not 1 of filter_*
34falsepositives:
35 - False positives are possible if the environment is using certificates for authentication. We recommend filtering Account_Name to the Domain Controller computer accounts.
36level: high
References
Related rules
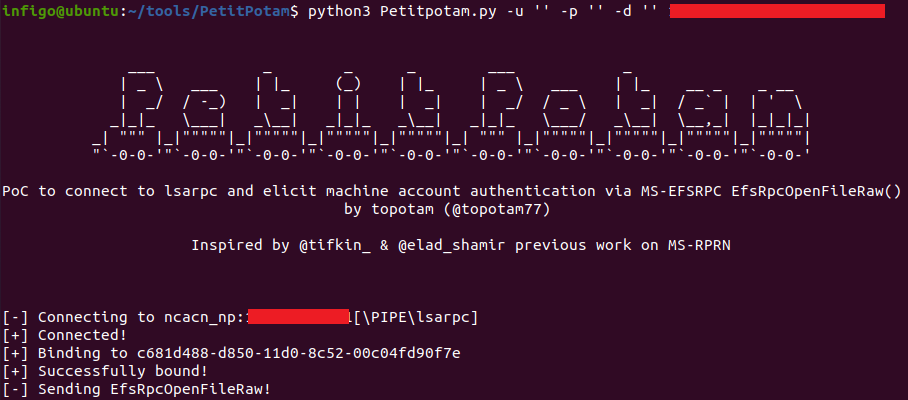
- Possible PetitPotam Coerce Authentication Attempt
- Azure Kubernetes Network Policy Change
- Azure Kubernetes RoleBinding/ClusterRoleBinding Modified and Deleted
- HackTool - Potential Remote Credential Dumping Activity Via CrackMapExec Or Impacket-Secretsdump
- Access To Crypto Currency Wallets By Uncommon Applications